⏱ 24 min read
API Architecture Lessons from Enterprise Modernization | Best Practices for Scalable Integration enterprise architecture principles template
Explore key API architecture lessons from enterprise modernization, including scalability, governance, security, integration patterns, and legacy transformation strategies. ArchiMate for governance
API architecture, enterprise modernization, API design, legacy modernization, scalable integration, API governance, enterprise integration, API security, digital transformation, microservices architecture, modernization strategy, system interoperability architecture governance checklist
Introduction
Enterprise modernization rarely starts with APIs. It usually begins with a cloud move, an infrastructure refresh, application rationalization, or process automation. APIs move to the center only when systems must share data and business capabilities across domains. At that point, they stop being simple interfaces and become operating contracts. They shape how quickly the business can adapt, how safely teams can change systems, and how effectively capabilities can be reused.
One lesson appears repeatedly in modernization work: APIs should not be treated as a thin integration layer added after the major platform decisions are made. When they arrive late, they tend to mirror internal complexity, expose unstable implementation details, and bind consumers to specific applications. When they are designed early, they help establish cleaner domain boundaries, more consistent interaction patterns, and a reusable base for future change. In that role, APIs are not project byproducts. They are enterprise products with owners, lifecycle expectations, and measurable value.
Modernization also exposes a persistent tension between speed and control. Business leaders want new services delivered quickly. Security, compliance, and operations teams need consistency, visibility, and resilience. API architecture sits squarely in that gap. A well-structured API landscape lets teams move independently while still operating within enterprise guardrails for identity, traffic management, observability, and version governance. In practice, this shows up in concrete decisions. An architecture board may approve a common gateway pattern and domain ownership model, yet reject a proposal for direct channel-to-database access because it bypasses policy, monitoring, and change control. architecture decision record template
Another durable lesson is that APIs last longer when they are designed around business capabilities rather than applications. Capabilities such as customer profile, pricing, order status, or payment authorization usually outlive the systems that implement them at any given moment. Exposing those capabilities through stable contracts reduces disruption during platform replacement and supports incremental modernization, which is usually more realistic than a large cutover in a complex enterprise. It also allows legacy systems, packaged platforms, and cloud-native services to coexist during transformations that often run for years.
These choices have long-term economic consequences. Inconsistent contracts, duplicated services, and tightly coupled integrations increase maintenance cost and slow future delivery. Standardized patterns, clear ownership, discoverable catalogs, and automated governance do the opposite. They limit drift and improve reuse. Enterprises that modernize well tend to treat API architecture as a strategic discipline spanning design, security, governance, integration, platform enablement, and runtime operations. ARB governance with Sparx EA
The sections that follow build on those ideas. First comes the role of APIs in creating controlled separation from legacy complexity. From there, the discussion moves to capability and domain alignment, governance and security across the lifecycle, APIs alongside event-driven and hybrid integration patterns, platform enablement and delivery, and finally the measures that show whether the architecture is producing real enterprise value.
1. Legacy Complexity and the Case for API-First Modernization
Legacy environments are rarely difficult simply because they are old. They become difficult because they accumulate years of business exceptions, undocumented dependencies, and tightly coupled process logic. In many industries, core platforms remain in place for a practical reason: they still perform essential functions reliably. The challenge is therefore not to replace everything at once. It is to create a controlled way to evolve around systems that are still operationally necessary.
That is where an API-first modernization approach proves useful. The goal is not to expose every legacy function directly. In most cases, that only pushes existing complexity outward and makes future change harder. A better approach starts by identifying which business capabilities need to be consumed across domains, then defining stable contracts around those capabilities before deciding how the underlying implementation should work.
The sequence matters. If teams begin with the legacy interface, they usually reproduce old transaction models, field names, and processing assumptions. If they begin with the business capability, they are more likely to design interfaces that remain useful for future channels, analytics platforms, partner ecosystems, and new digital products. This is the first practical expression of capability-based API design. capability map example
From an architectural perspective, APIs create separation between the pace of change in the consumer landscape and the slower pace of change in systems of record. Front-end channels, workflow tools, and cloud services usually evolve much faster than mainframes, ERP platforms, or monolithic business applications. An API layer can absorb protocol translation, data shaping, authentication mediation, and policy enforcement without forcing immediate replacement of the underlying platform. That makes incremental modernization possible and avoids high-risk cutovers.
Not every legacy system should be handled in the same way. Some are good candidates for façade APIs because their functions are coherent and stable. Others need anti-corruption layers to shield consumers from inconsistent data models or proprietary semantics. In more complicated cases, event capture, replication, or process decomposition may be necessary before a useful API can exist. A practical classification helps:
- Retain and wrap: keep the system in place and expose stable access through APIs.
- Refactor and expose: improve internal structure before exposing broader capability APIs.
- Decompose progressively: split out services over time while maintaining stable external contracts.
- Retire and redirect: move consumers to replacement capabilities and phase out the legacy interface.
This avoids a common mistake: assuming one integration pattern can solve every legacy problem.
A simple example illustrates the point. A bank may keep its core deposit platform in place because it is operationally stable, but expose account balance and transaction history through a domain API rather than letting mobile and branch applications call host transactions directly. The API can normalize field names, enforce authentication, and hide host-specific codes. Later, if transaction history moves to a new data service, the consumer contract can remain intact.
API-first thinking also improves portfolio planning. Once business capabilities are expressed as APIs, architects can see where applications overlap, where dependencies are concentrated, and where ownership is unclear. That visibility supports rationalization. It becomes easier to distinguish strategic capabilities that deserve long-term product investment from temporary interfaces that exist only to support transition states.
There is an organizational benefit as well. Legacy estates often reflect siloed teams and fragmented knowledge. Defining APIs early forces conversations about ownership, lifecycle expectations, service levels, and consumer responsibilities. In many cases, those conversations matter more than the interface style itself because they establish how modernization will be governed across teams.
The central lesson is straightforward: API-first modernization is not about exposing legacy systems faster. It is about creating deliberate contracts that reduce dependency on legacy internals while preserving continuity in the business services that matter. That leads directly to the next question: what should those contracts be organized around?
2. Aligning API Architecture with Business Capabilities and Domain Boundaries
If API-first modernization creates separation from legacy complexity, capability and domain alignment determine whether that separation is coherent. API quality depends less on syntax than on the boundary the API represents. Portfolios become hard to govern when services are organized around applications, databases, or projects instead of durable business capabilities.
Business capability alignment begins with a basic question: what must the organization be able to do consistently, regardless of which system currently performs the work? Examples include managing customer identity, calculating eligibility, pricing an offer, scheduling fulfillment, or authorizing payment. These capabilities usually outlast individual applications. APIs designed around them are therefore more likely to remain stable through transformation because they reflect business intent rather than technical structure.
That stability is one of the main reasons capability-based APIs support incremental modernization. If a pricing API expresses a stable pricing capability, the underlying pricing engine can change without forcing every consumer to change with it. If the API is only a wrapper around a specific application, the contract becomes fragile as soon as that application changes.
Domain boundaries add another layer of discipline. In large enterprises, terms like customer, order, account, claim, or asset often mean different things in different business units. Effective API architecture does not force artificial uniformity too early. It makes explicit which domain owns a concept, which domains consume it, and what level of consistency is required between them. Without that clarity, portfolios drift into overlapping endpoints, conflicting definitions, and constant negotiation between teams.
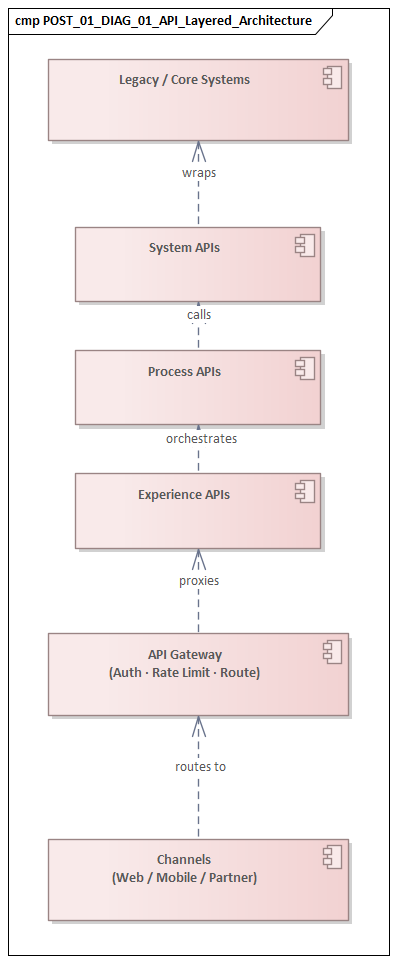
A useful operating model is a layered API structure:
- System APIs encapsulate access to systems of record and shield consumers from platform-specific details.
- Domain APIs express business capabilities in language meaningful across teams and compose underlying data or rules where needed.
- Experience APIs tailor interactions for specific channels such as mobile apps, partner portals, or internal workflow tools.
This layered model reinforces the separation described earlier. System APIs protect consumers from platform volatility. Domain APIs provide the stable capability contracts modernization depends on. Experience APIs allow channels to move quickly without distorting core business contracts.
Ownership should follow the same pattern. APIs should be owned by the domain accountable for the capability, not simply by the technical team that built the first version. That distinction becomes especially important during change. When ownership stays only with platform teams, interfaces often reflect operational convenience. When ownership follows domain accountability, versioning decisions, service levels, and roadmap priorities are more likely to align with enterprise needs.
Consider a retail example. A company may have separate e-commerce, store, and loyalty platforms, each with its own notion of customer. If every team exposes its own “customer API,” duplication and conflict are inevitable. A better model assigns ownership of the core customer profile capability to a customer domain, while channel teams build experience APIs for their specific needs. The mobile app may need lightweight profile retrieval and preferences, while the call center needs richer service history. Both consume the same domain capability without redefining it.
Domain boundaries should also be tested against realistic change scenarios. Architects should ask whether the API boundary still makes sense when pricing rules change, a new sales channel is introduced, a merger brings in duplicate master data, or regulation changes retention policy. If every likely change cuts across multiple APIs and teams, the boundary is probably wrong. Good boundaries localize change and make exceptions visible rather than accidental.
The same principle applies in identity and access management. Instead of each application exposing its own user and role model, the enterprise can define a shared identity capability while leaving authorization decisions with the domains that own the underlying business actions. Authentication becomes consistent; business authority remains local.
This capability-and-domain model becomes the base for everything that follows. Governance depends on clear ownership and defined boundaries. Security depends on knowing which domain owns which data and decisions. Integration patterns depend on understanding which interactions are transactional and which are better handled as cross-domain propagation. Platform enablement depends on giving teams repeatable ways to implement those patterns. Without that foundation, later controls become inconsistent and expensive.
3. Designing for Governance, Security, and Compliance at Enterprise Scale
Once APIs are aligned to business capabilities and domain boundaries, the next challenge is making them governable at scale. Governance, security, and compliance are not concerns to bolt on later. They are structural conditions that determine whether an API portfolio stays safe, understandable, and sustainable as adoption grows.
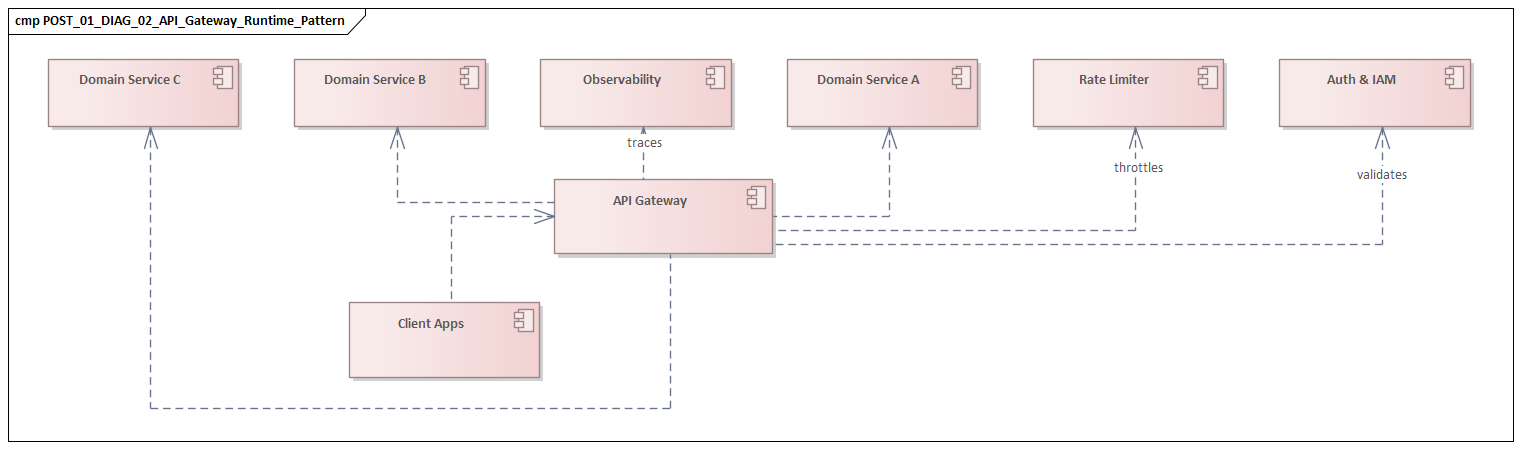
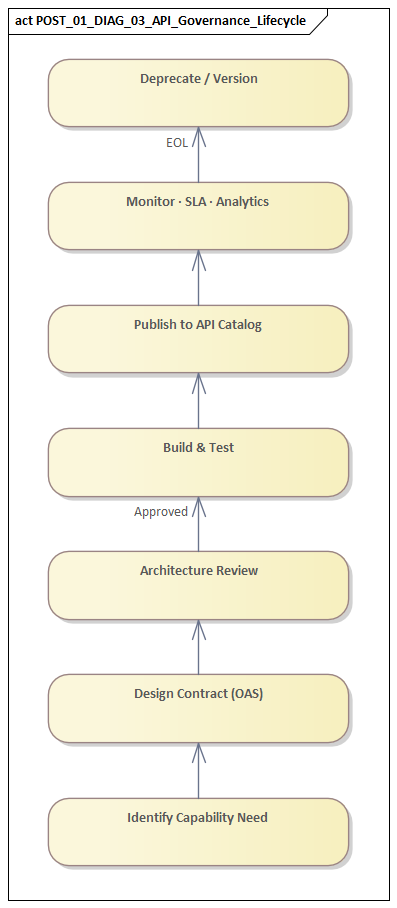
Governance has to operate at several levels. At the portfolio level, enterprises need visibility into what APIs exist, which capabilities they expose, who owns them, what data they handle, and which consumers depend on them. Without that visibility, duplication grows quickly and unmanaged dependencies accumulate. At the design level, teams need standards for naming, error handling, authentication patterns, documentation, and versioning. At runtime, governance extends into traffic control, observability, resilience policies, and deprecation management.
Organizations often struggle because they address only one of those layers. They may publish standards without enforcing them at runtime, or deploy a gateway without establishing ownership and lifecycle rules. Governance works best when it rests on clear domain ownership and capability boundaries.
Security architecture matters just as much because APIs often become the most direct route into critical business data and transactions. Modernization programs usually inherit inconsistent identity models from legacy applications, partner integrations, and cloud platforms. A practical response is to separate authentication, authorization, and policy enforcement from individual services wherever possible. Centralized identity federation, token-based access control, mutual TLS where appropriate, and reusable policy enforcement at gateway or service mesh layers reduce inconsistency and keep each team from inventing its own approach.
Still, centralized controls solve only part of the problem. Domain-level authorization remains essential. A user may be authenticated correctly and still not be allowed to perform a sensitive business action. That is why security needs both enterprise-wide identity patterns and domain-specific authorization logic, fine-grained entitlements, and auditable decision paths inside the API implementation.
A healthcare example makes this concrete. An enterprise may authenticate clinicians through a common identity provider and issue standard access tokens across all applications. Even so, a patient-record API still has to enforce local rules: whether the clinician is assigned to the patient, whether access is permitted for the treatment context, and whether certain fields must be masked for regional privacy requirements. Enterprise identity gets the caller in; domain policy decides what the caller can actually do.
Compliance introduces another set of demands. Requirements around privacy, consent, auditability, retention, and data residency rarely line up neatly with technical boundaries. APIs therefore need explicit data classification and handling rules from the start. A customer data API, for instance, may require field-level masking, purpose-based access restrictions, and immutable audit trails depending on jurisdiction and use case. Controls like these are difficult to retrofit once adoption is broad.
The most scalable approach is to automate as much governance and compliance as possible. Review boards can define principles and manage exceptions, but they cannot manually inspect every contract change. Effective organizations codify standards into reusable templates, linting rules, security tests, and platform guardrails. API specifications can be validated for required metadata, naming conventions, and backward compatibility. Deployment pipelines can verify authentication settings, certificate handling, logging requirements, and rate-limiting policies before promotion.
That automation only works when ownership is explicit. Every API should have a defined owner responsible for contract quality, consumer communication, operational health, and compliance posture. A central catalog should link each API to its domain, data classification, service objectives, and dependency map. In large estates, that catalog becomes indispensable during audits, incident response, and modernization planning.
The broader point is simple: governance, security, and compliance are not obstacles to API-led modernization. They are what make it sustainable. Once those controls are in place, architects are in a much stronger position to decide something else that repeatedly shapes modernization outcomes: which interaction pattern fits which business exchange.
4. Integration Patterns, Event-Driven Architecture, and Hybrid Environments
The earlier sections established two principles: APIs should represent stable business capabilities, and those capabilities need clear ownership and policy. The next lesson is that even strong APIs are only part of the integration picture. Modern enterprises operate in hybrid environments where SaaS platforms, cloud-native services, packaged applications, data platforms, and legacy systems interact under different latency, consistency, and availability constraints. APIs are essential, but they are not the right mechanism for every interaction.
A practical starting point is to distinguish interaction types before choosing technology:
- Request-response APIs are suited to immediate queries and transactional operations where the consumer needs a prompt answer.
- Event-driven patterns are suited to communicating that something has happened without creating tight runtime dependency for downstream consumers.
- Batch or bulk transfer patterns still make sense for high-volume extracts, reporting, or transitional integration with platforms that cannot support real-time access economically.
Modernization programs become more stable when architects define where each pattern belongs instead of defaulting to synchronous APIs everywhere.
Event-driven architecture is especially valuable in hybrid estates because it reduces direct coupling between producers and consumers. Rather than having every downstream system poll or invoke a source application repeatedly, an event can be published once and consumed by many parties according to their own needs. That supports scalability and makes it easier to add new consumers—analytics platforms, workflow engines, notification services, machine learning pipelines—without major disruption.
A common example is order processing. Once an order is confirmed, the commerce platform can publish an OrderConfirmed event to Kafka or a cloud event bus. Fulfillment subscribes to start picking, billing subscribes to create the invoice, and analytics subscribes to update sales dashboards. None of those consumers needs a direct synchronous dependency on the commerce application at the moment of confirmation.
But event-driven architecture comes with its own discipline. Events should represent meaningful business facts, not internal technical state changes. An event such as OrderConfirmed communicates a stable business occurrence. An event such as DatabaseRowUpdated usually exposes source-system internals and creates fragile downstream dependencies. The principle is the same one introduced earlier for APIs: contracts should express business meaning, not implementation detail.
Architects also need to decide whether events should be simple notifications or richer business messages. Notifications tell consumers that something changed and require follow-up retrieval. Rich events include enough data to support more independent processing. The right choice depends on payload sensitivity, replay needs, operational cost, and consistency expectations.
Hybrid environments also force realism about consistency. Teams often assume APIs can preserve immediate consistency across old and new platforms, only to discover that network boundaries, transaction scopes, and vendor constraints make that unrealistic. A more durable approach is to design for eventual consistency where appropriate and make that behavior explicit. That means defining idempotency, duplicate handling, retry behavior, ordering expectations, and reconciliation processes up front. These are architectural decisions, not implementation details to sort out later.
For example, an insurer modernizing claims may keep adjudication on a legacy platform while moving document intake and customer communication to cloud services. A synchronous API may still be appropriate for claim status lookup, because the portal needs an immediate answer. Document ingestion, however, may publish events that trigger fraud checks, indexing, and downstream notifications asynchronously. Trying to force all of that into a single synchronous chain would increase latency and failure coupling without improving business outcomes.
As with governance, pattern selection should follow business criticality and domain context. High-value transactional paths may require synchronous APIs with strong timeout discipline, observability, and compensating actions. Cross-domain propagation of state changes may be better handled through event brokers with schema management, dead-letter handling, and replay controls. Legacy platforms that cannot publish events natively may need change data capture or integration mediators so they can participate without invasive modification.
In practice, the target architecture in most enterprises is neither purely API-led nor purely event-driven. It is a deliberate combination: APIs handle interaction at the point of need, while events distribute change across the wider ecosystem. That combination only works if teams can implement it consistently, which leads directly to platform enablement and lifecycle management.
5. Developer Experience, Platform Enablement, and API Lifecycle Management
If the previous sections describe what good API architecture looks like, platform enablement determines whether delivery teams can implement it consistently. Many organizations define sound principles for capability alignment, governance, and integration patterns, yet still end up with fragmentation because teams experience those principles as friction rather than support. In practice, developer experience is an architectural issue.
Developer experience covers the full path from design to consumption: templates, specification tooling, mock services, test environments, onboarding guides, SDK generation, portal usability, sample policies, and support channels. Strong standards are not enough if publishing, discovering, securing, testing, and evolving APIs is difficult. Teams under pressure will create workarounds, duplicate services, or bypass shared patterns.
For that reason, platform enablement should be treated as an internal product. A well-designed API platform provides reusable capabilities such as identity integration, secrets handling, traffic management, schema validation, telemetry, and developer portal services. Its purpose is not to impose uniform technology for its own sake. It is to create predictable delivery mechanics across heterogeneous environments.
Platform teams should provide paved roads rather than ticket-driven gatekeeping. Scaffolding can include standard logging, correlation IDs, health endpoints, authentication hooks, and baseline policy definitions. CI/CD pipelines can automatically run specification linting, backward compatibility checks, security scans, and documentation publication. Self-service environment provisioning can allow teams to test integrations and policies earlier, reducing late surprises.
This platform model directly supports the governance approach described earlier. Automated guardrails make standards scalable. It also supports the integration model from the previous section by giving teams repeatable ways to implement synchronous APIs, event publication, schema management, and observability.
Lifecycle management matters just as much because enterprise APIs rarely stay static. Modernization efforts often produce interfaces quickly to support transition states, but without disciplined lifecycle management those interfaces linger indefinitely. Architects need clear models for introduction, evolution, deprecation, and retirement.
A mature lifecycle approach includes:
- versioning rules based on consumer impact,
- support windows and deprecation timelines,
- dependency visibility before contract changes,
- usage analytics to confirm what consumers actually rely on,
- communication channels for roadmap and change notices.
One of the most important distinctions is the difference between contract stability and implementation change. Teams should be encouraged to improve internals aggressively while preserving external reliability whenever possible. That requires contract testing, consumer communication, and observability that shows who is using which operations and fields. In many cases, field-level usage analytics are more useful than aggregate traffic counts because they show whether a simplification is actually safe.
A realistic example comes from platform migration. Suppose an enterprise is replacing an older API gateway with a managed cloud gateway. If the platform team treats the change as purely infrastructural, downstream teams may discover policy differences late and scramble to adapt. A stronger approach publishes migration templates, validates policies in CI/CD, exposes test environments early, and tracks which APIs still depend on deprecated gateway features. The platform change becomes manageable because the lifecycle is visible and supported.
Managing APIs as products reinforces this discipline. Product thinking brings roadmaps, service objectives, feedback loops, and adoption metrics. An API is not successful simply because it has been deployed. It is successful when it is understandable, trusted, reusable, and maintainable over time. The same discipline should apply to platform components: a technology lifecycle board might set a deadline to retire an unsupported gateway version, require migration plans for affected APIs, and block new deployments on the old stack.
At this stage, the architecture has clear capability boundaries, embedded governance, appropriate interaction patterns, and a platform model that helps teams deliver consistently. The final question is whether all of this is producing better enterprise outcomes.
6. Measuring Outcomes: Resilience, Observability, and Business Value
A common weakness in modernization programs is that API success is measured too narrowly. Counts of published APIs, migrated integrations, or gateway traffic are easy to report, but they reveal little about whether the architecture is improving enterprise performance. API architecture should be measured by outcomes: resilience under failure, operational transparency, speed of safe change, and contribution to business capability delivery.
Resilience is one of the most important indicators because modernization increases distributed dependencies. APIs should be assessed not only against availability targets, but also by how they behave under stress. Useful measures include timeout rates, retry amplification, dependency failure propagation, saturation under peak load, and recovery time after partial outages. In practice, an API that remains available in a degraded mode may support business continuity better than one that fails hard in the name of technical purity.
Observability provides the evidence needed to make those judgments. Logs and infrastructure dashboards alone are not enough because they do not show how business transactions move across domains. Effective observability connects technical telemetry with business context: correlation IDs across services, traces for end-to-end transaction paths, metrics by capability and consumer, and structured events that show where requests fail, queue, retry, or require manual intervention.
This should not be treated as an afterthought. As discussed in the governance and platform sections, observability needs to be designed into standards, contracts, and delivery pipelines from the start. Trace propagation, error categorization, audit event structure, and minimum telemetry expectations should be part of the API model. Telemetry should also be enriched with domain metadata such as channel, region, product line, or process stage so teams can assess business impact rather than just technical severity.
Business value measurement matters just as much because not every API deserves the same level of investment. Some interfaces are strategic enablers of reuse and channel growth; others are transitional assets that support coexistence. Architects need a way to tell the difference. Useful indicators include:
- adoption across domains,
- reduction in duplicate integrations,
- faster launch of new channels or products,
- reduced incident rates in critical journeys,
- lower dependency on legacy-specific interfaces,
- ability to replace underlying platforms without consumer disruption.
In some cases, value can be measured directly through revenue enablement or cost avoidance. In others, the signal is architectural: fewer point-to-point integrations, lower change failure rates, or better reuse of common capabilities.
A logistics organization, for instance, might track whether a shipment-status API is reused by customer portals, warehouse systems, and partner integrations instead of maintaining separate feeds for each. If a later warehouse platform replacement leaves those consumers unaffected, that is strong evidence that the API created real architectural value, not just another interface.
Outcome measurement should be built into portfolio governance. Significant APIs should have a small set of indicators spanning reliability, usage, and business contribution, reviewed regularly by both domain and platform stakeholders. Service-level objectives should reflect consumer experience, not just internal component health. Dependency maps and tracing should be used during architecture reviews to identify where resilience risks or low-value complexity are accumulating.
The broader lesson is simple: an API program becomes credible when it is measured by enterprise outcomes rather than interface volume. Modernization creates value when APIs make the organization more durable, more transparent, and easier to change.
Conclusion
Enterprise modernization shows that API architecture is most valuable when it becomes part of how the enterprise is designed, governed, and evolved, not merely how systems are connected. The strongest organizations do not use APIs as technical wrappers around change. They use them to make change safer, more visible, and more repeatable across complex portfolios.
The pattern across these lessons is clear. APIs create controlled separation from legacy complexity. That separation only holds when interfaces align with durable business capabilities and clear domain boundaries. Governance, security, and compliance must be built into the lifecycle rather than added later. APIs also need to be combined with the right integration patterns, especially in hybrid and event-driven environments. Platform enablement and lifecycle management are what make good architecture practical for delivery teams. And success should be judged through resilience, observability, and business value, not raw interface counts.
Taken together, these lessons point to a broader conclusion: API architecture creates optionality. Stable contracts allow enterprises to replace platforms, onboard partners, reorganize teams, and introduce new digital capabilities without renegotiating every integration from scratch. That optionality becomes strategically valuable in environments shaped by regulatory change, mergers, market shifts, and ongoing cloud transformation.
The practical implication is straightforward. Enterprises should build API portfolios deliberately, with explicit principles for capability alignment, ownership, security, runtime behavior, and retirement. Architects should favor measurable consistency over theoretical perfection and design for coexistence rather than assume clean replacement paths. Modernization rarely ends in a single target state. API architecture matters because it provides the continuity layer that lets the enterprise keep changing without losing coherence.
Frequently Asked Questions
What are the key lessons from enterprise API architecture?
Key lessons include: design APIs around business capabilities not applications, establish clear domain ownership before exposing endpoints, automate governance and compliance checking, choose the right integration pattern (request-response vs event-driven) for each interaction type, and treat APIs as long-lived products with lifecycle governance.
What is API-first modernisation?
API-first modernisation means defining stable API contracts aligned to business capabilities before deciding how the underlying implementation should work. It creates separation between the pace of change in consumer channels and the slower pace of change in systems of record, enabling incremental modernisation without high-risk cutovers.
How do you govern APIs at enterprise scale?
Enterprise API governance requires portfolio visibility (catalogue), design standards (naming, versioning, authentication), runtime controls (gateway policies, rate limiting, observability), and ownership accountability (domain-based ownership, lifecycle responsibility). Automation of standards checking and compliance validation is essential at scale.