⏱ 26 min read
Enterprise Architecture Principles Template with Real Examples | Guide Sparx EA guide
Discover an enterprise architecture principles template with real-world examples. Learn how to define, document, and apply architecture principles for governance, standards, and decision-making. how architecture review boards use Sparx EA
enterprise architecture principles template, enterprise architecture principles examples, architecture principles template, enterprise architecture governance, architecture decision-making, EA principles, enterprise architecture standards, TOGAF architecture principles, architecture governance framework, enterprise architecture best practices Sparx EA best practices
Introduction
Enterprise architecture principles are a small set of durable rules that guide how an organization designs and governs business processes, applications, data, and technology. They are not detailed standards, and they are not project-specific requirements. Their purpose is more fundamental: to provide a stable basis for decision-making across programs, delivery teams, and governance forums.
Their value becomes clear in large organizations managing several forms of change at once—cloud migration, application modernization, data platform redesign, regulatory remediation, and operating model transformation. Without shared principles, teams optimize locally. One program prioritizes speed over maintainability. Another chooses local customization over reuse. A third introduces a duplicate capability because no enterprise rule is strong enough to challenge the decision. Over time, those choices produce fragmented architecture, inconsistent controls, rising technical debt, and avoidable governance friction.
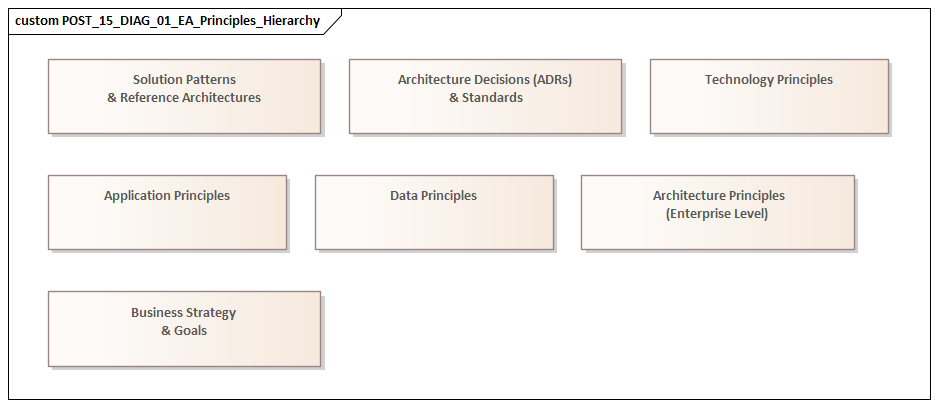
Principles help prevent that drift. They translate strategic intent into design expectations that can be applied repeatedly. A strategy may call for lower cost, faster product delivery, stronger resilience, or tighter regulatory control. Principles turn those ambitions into practical rules. For example, “Reuse before buy before build” influences portfolio planning, solution design, and investment decisions. “Data has an accountable owner and an authoritative source” shapes ownership models, integration choices, and reporting consistency. In that sense, principles sit above standards, patterns, and roadmaps: they establish direction, while downstream artifacts provide detail.
For principles to be useful, they must be more than slogans. A good principle is concise, tied to business need, and clear enough to test against real decisions. If a proposed solution duplicates customer data, bypasses enterprise integration patterns, or selects a nonstandard platform without a compelling reason, the relevant principle should make the conflict obvious. That is why structure matters. At a minimum, each principle should include a clear statement, a business rationale, and practical implications. Together, those elements make principles easier to remember, defend, and apply.
This article provides a practical template for writing enterprise architecture principles and making them usable. It begins by clarifying what principles are and why they matter, then outlines the core elements of an effective template. From there, it looks at how to create principles that can actually be governed, offers examples across key architecture domains, and closes with guidance on applying and maintaining them over time. The objective is not to produce a long list of abstract ideals, but a small set of durable rules that improve decision-making across the enterprise.
What Enterprise Architecture Principles Are and Why They Matter
Enterprise architecture principles are foundational decision rules that shape how an organization evolves its operating model and technology landscape over time. They are broader than solution requirements and more durable than project priorities. Strategies may shift with market conditions, and roadmaps may change with funding cycles, but principles provide continuity. They become the reference point for recurring trade-offs across business capability design, application portfolios, data management, integration, security, and infrastructure.
A useful way to think about principles is as the link between strategy and execution. Strategy defines intent: improve agility, reduce cost, strengthen compliance, simplify operations, or enhance customer experience. Principles convert that intent into architectural expectations teams can apply repeatedly. If the business wants greater agility, the architecture may need principles that favor modularity, loosely coupled integration, and standardized platforms. If the enterprise needs tighter control, it may need principles around traceability, secure-by-design delivery, and authoritative data sources.
This role matters because large organizations rarely suffer from a lack of ideas. More often, they struggle because decisions are made inconsistently across teams and programs. One initiative optimizes for immediate delivery speed. Another responds to local business preference. A third pursues technical elegance. Each choice may be defensible in isolation, but together they create duplication, brittle integration, fragmented user experience, and growing support costs. Principles provide a common lens for evaluating options before local decisions harden into enterprise complexity.
They matter most when they influence real choices. They should help answer questions such as:
- Should we extend an existing platform or introduce a new one?
- Should this capability be standardized globally or allowed to vary locally?
- Where should this data be mastered?
- When is customization justified?
- What level of interoperability is mandatory?
- What happens if a team needs to deviate?
Used well, principles align stakeholders who naturally approach decisions from different angles. Executives focus on outcomes. Engineers focus on feasibility. Risk teams focus on control. Product teams focus on speed and usability. A well-written principle gives them common ground by connecting enterprise value to design consequences.
Principles also create disciplined flexibility. They do not eliminate choice; they define the boundaries within which choice remains productive. Teams can still select tools and implementation patterns that fit their context, but those choices should remain aligned with enterprise expectations for interoperability, supportability, security, and cost. This balance is especially important in federated organizations, where central architecture cannot—and should not—control every decision directly.
In practice, the benefit is concrete. A bank may allow a temporary local onboarding workflow to meet a country-specific regulatory deadline, but reject a second customer master because it violates the principle of authoritative data ownership. A manufacturer might approve a plant-specific analytics dashboard while refusing a separate identity store for contractors because the enterprise IAM service already exists. Principles make those trade-offs explicit, repeatable, and easier to defend.
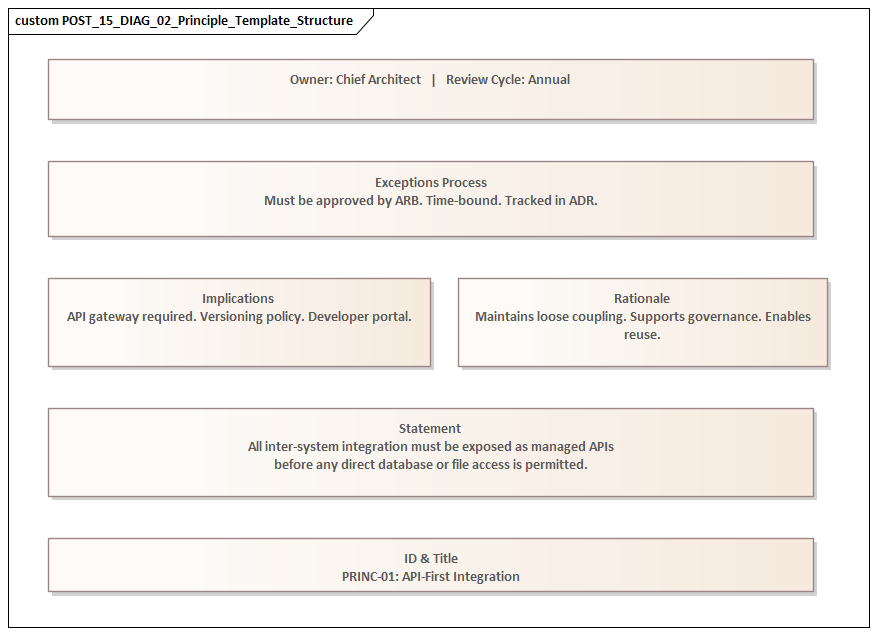
Core Elements of an Effective Enterprise Architecture Principles Template
If principles are meant to function as decision rules rather than slogans, they need a consistent structure. A strong template forces clarity, surfaces trade-offs, and makes principles easier to use in governance and delivery. Without that structure, some principles become vague aspirations, while others drift into detailed standards in disguise. The result is uneven quality and weak adoption.
An effective template should include the following elements.
1. Principle statement
This is the core rule or preference. It should be short, direct, and easy to remember. Examples include:
- Reuse before buy before build
- Data has an accountable owner
- Integration is API-first
- Security is designed in
The statement should not carry the full explanation. If it becomes long or heavily conditional, too many ideas have probably been combined and should be separated.
2. Business rationale
The rationale explains why the principle exists and what enterprise outcome it supports. This is where the principle is tied to concerns such as cost efficiency, resilience, compliance, speed to market, customer experience, or operational simplicity.
This matters because people are more willing to accept constraints when they understand the business value behind them. It also helps architecture teams explain decisions in language executives and delivery leaders recognize, rather than relying only on technical arguments.
3. Architectural implications
Implications translate the principle into expected behavior. They describe what the principle means for solution design, technology selection, funding decisions, and delivery practices.
For example, if the principle is “Prefer strategically approved platforms and managed services,” the implications might include defaulting to enterprise cloud services, justifying any nonstandard hosting model, and designing for operational automation. In an IAM modernization program, the same principle might mean using the enterprise identity provider and standard access patterns rather than embedding authentication separately in each application.
4. Scope of applicability
Not every principle applies equally in every context. Some are enterprise-wide. Others matter most in regulated domains, business-critical services, greenfield products, or post-merger integration work. Sparx EA training
Declaring scope up front avoids misuse and unnecessary debate. It also helps architects explain when a principle is mandatory, when it is directional, and when legacy containment or experimentation may justify a different approach.
5. Compliance indicator or evidence
Principles should be testable. A template should therefore make clear how adherence will be assessed. That does not mean every principle needs a hard metric, but there should be observable evidence.
Examples include:
- use of approved platforms
- reduction in duplicate applications
- identified system of record for critical data
- conformance to integration patterns
- documented exception approvals
This shifts governance away from subjective interpretation and toward more consistent evaluation.
6. Trade-offs and exception conditions
Principles are strong defaults, not absolute laws. In practice, they will sometimes conflict. Standardization may clash with local market needs. Reuse may conflict with speed. Data minimization may pull against analytics ambitions.
A good template acknowledges those tensions and sets out likely exception conditions. That makes principles more credible and supports disciplined exception handling instead of informal negotiation.
7. Owner and review cadence
Principles need stewardship. Each one should have an accountable owner—usually within enterprise architecture or a cross-functional governance body—and a review cadence to confirm that it still reflects enterprise priorities.
Without that, principles can become static artifacts that outlive the operating model, technology strategy, or risk posture they were meant to support. For example, a technology lifecycle principle may be reviewed annually to confirm whether a database platform has moved from strategic to contain or retire status.
A simple template
A practical enterprise architecture principle can usually be captured in the following format:
- Name
- Statement
- Business rationale
- Architectural implications
- Scope
- Evidence of compliance
- Trade-offs / exception conditions
- Owner
- Review cadence
This structure provides enough discipline to make principles governable without making them too heavy to use. The next section looks at how to create principles with this template so they influence real decisions.
How to Create Enterprise Architecture Principles That Are Actionable and Governable
Creating enterprise architecture principles is not primarily a writing exercise. It is a design and governance exercise. Many organizations can produce a list of sensible statements; far fewer produce principles that consistently shape investment decisions, solution designs, and delivery behavior. The difference lies in how the principles are derived, tested, and embedded.
Start from recurring enterprise decisions
The best principles come from recurring pain points, not abstract ideals. Architects should look for places where the organization repeatedly encounters inconsistency or friction, such as:
- platform proliferation
- duplicate capabilities
- fragmented data ownership
- inconsistent security controls
- local process variation
- rising integration complexity
These are the areas where principles add real value because they reflect decisions the enterprise keeps making. If a principle does not address a meaningful class of recurring decisions, it is unlikely to matter in practice.
For example, an enterprise struggling with overlapping SaaS products may need a principle focused on capability reuse and platform consolidation. A heavily regulated business may need stronger principles around traceability, data lineage, and secure-by-design delivery.
Test principles against real scenarios
A simple way to check whether a principle is usable is to ask: What would this principle cause a team to do differently next quarter? If the answer is unclear, the principle is probably too vague.
Scenario-based testing is especially useful. Take recent or active initiatives and ask whether the draft principle would have:
- clarified the preferred direction
- exposed a risk
- narrowed the option set
- triggered an exception process
This confirms whether the principle can influence real choices in vendor selection, integration design, data ownership, hosting, and funding. For instance, if a team proposes direct system-to-system messaging while the enterprise event strategy is Kafka-based, the principle should make clear whether they must publish through governed Kafka topics instead.
A retail example makes the point. Suppose an e-commerce team wants to add a niche promotions engine because the current commerce platform cannot support one campaign type. A reuse principle should force a fit-gap review first: can the existing platform be configured, can the campaign be handled through a rules service, or is a new product genuinely justified? Without that test, “reuse” remains aspirational.
Write at the right level of abstraction
A principle should be durable enough to survive technology change but specific enough to guide downstream standards and patterns. Too broad, and it becomes generic. Too detailed, and it turns into a standard disguised as a principle.
For example:
- Principle-level: “Solutions must expose business capabilities through governed interfaces.”
- Not principle-level: “All APIs must use product X gateway with policy set Y.”
The first can remain valid over time and drive multiple technical standards. The second belongs in a standard or reference architecture.
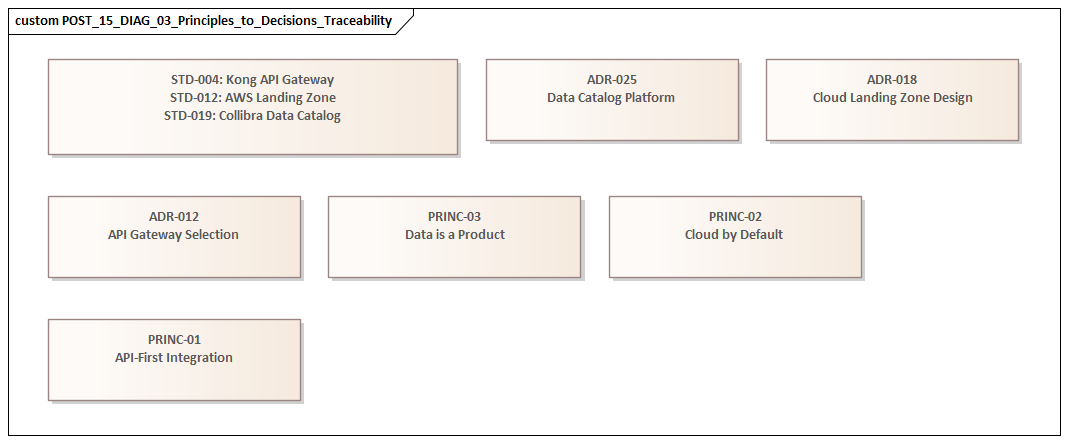
Link principles to governance processes
Each principle should be mapped to the forums and artifacts where it will be assessed. Otherwise, it remains advisory.
Typical integration points include:
- business case templates
- architecture review checklists
- solution design documents
- platform selection criteria
- risk assessments
- exception workflows
Mature architecture teams often translate each principle into a small set of review questions. For example:
- Does this initiative reuse an existing enterprise capability?
- Has an authoritative data source been identified?
- Is the integration approach aligned with enterprise patterns?
- Is any deviation temporary, and what is the exit plan?
These questions make principles operational without forcing everyone to interpret abstract wording on their own.
Define consequences and exception handling
Governability depends on consequences. Teams need to know what happens when a principle is not followed. Depending on the case, nonconformance may require:
- formal exception approval
- compensating controls
- a remediation roadmap
- explicit risk acceptance
- time-bound transitional architecture
This is especially important in federated enterprises. Local autonomy is often necessary, but it still has to operate within enterprise guardrails. Transparent exception handling gives principles credibility.
Build social adoption, not just formal approval
A principle set can be formally approved and still fail in practice if delivery teams do not understand it or trust it. Enterprise architects should socialize principles with product leaders, security teams, data owners, engineering leads, and finance stakeholders before finalization.
That does not mean removing every tension. It means making sure the wording, rationale, and implications are clear enough that different groups can apply them consistently. The strongest principles are the ones teams can cite in delivery conversations without needing an architect in the room every time a trade-off appears.
One practical approach is to use short architecture clinics during major programs. In a cloud migration, for example, platform engineering, security, and application teams can walk through a handful of representative decisions—managed database versus self-hosted, shared identity versus local authentication, event integration versus file transfer—and test the draft principles against them. That kind of rehearsal often reveals ambiguity faster than any workshop document.
Real Example Principles for Business, Data, Application, Technology, Security, and Integration
The template becomes most useful when it is applied consistently across architecture domains. The examples below follow the same structure and show how a compact principle set can cover major enterprise concerns without becoming bloated.
1. Business Principle: Standardize business capabilities before customizing processes
Statement: Core business capabilities should be standardized at the enterprise level unless a clear regulatory, market, or strategic reason requires variation.
Business rationale: Excessive process variation leads to duplicated systems, fragmented reporting, inconsistent controls, and higher support costs. Standardization improves scalability, training efficiency, and platform reuse.
Architectural implications: During operating model and solution design, architects should challenge requests for local process uniqueness unless they are tied to measurable business value or compliance needs. This principle is especially relevant in ERP transformation, shared services design, and post-merger harmonization. For example, a global manufacturer may allow country-specific tax handling, but not separate order-to-cash processes in every region if the same ERP platform can support a common model.
Scope: Enterprise-wide, with exceptions where legal or market conditions require local variation.
Evidence of compliance: Reduced process variants for core capabilities, documented justification for local deviations, and alignment of major platforms to agreed enterprise process models.
Trade-offs / exceptions: This may conflict with speed or local market responsiveness. Exceptions should be time-bound or explicitly tied to strategic differentiation.
2. Data Principle: Data has a single accountable owner and an authoritative source
Statement: Every critical data domain must have defined ownership and a recognized system of record or system of reference.
Business rationale: Unclear ownership creates conflicting definitions, duplicate stores, reconciliation effort, and weak trust in reporting and analytics.
Architectural implications: Solution designs should identify where critical data is created, maintained, and consumed. Architects should challenge uncontrolled replication of customer, product, employee, or financial data without stewardship and synchronization rules. In IAM modernization, this often means defining the HR platform as the authoritative employee source and the central directory as the operational identity service, rather than letting each application maintain its own user records.
Scope: Enterprise-wide for critical and regulated data domains.
Evidence of compliance: Named data owners, documented authoritative sources, lineage visibility, and reduced duplicate master data stores.
Trade-offs / exceptions: Analytics or local performance needs may justify replication, but only with governance, lineage, and synchronization controls.
3. Application Principle: Reuse existing enterprise capabilities before acquiring or building new ones
Statement: New business requirements should first evaluate reuse or extension of existing enterprise applications and services before introducing additional products or bespoke solutions.
Business rationale: Application sprawl increases licensing cost, integration overhead, operational complexity, and user inconsistency. Reuse protects prior investment and reduces duplicated functionality.
Architectural implications: Portfolio and solution architects should include capability mapping and fit-gap analysis in option evaluation. New tools should require explicit justification if an existing platform can meet the need with reasonable configuration or extension. In a sales organization, for instance, a request for a standalone partner portal should first assess whether the current CRM and API layer can support partner onboarding and case management before a new SaaS product is approved.
Scope: Enterprise-wide, particularly relevant to SaaS procurement and digital product delivery.
Evidence of compliance: Capability reuse analysis in business cases, reduction in overlapping tools, and fewer duplicate platforms serving the same business capability.
Trade-offs / exceptions: Speed, niche functionality, or strategic differentiation may justify a new application, but the enterprise impact must be made explicit.
4. Technology Principle: Prefer strategically approved platforms and managed services
Statement: Technology choices should align with the enterprise platform strategy, with managed and standardized services preferred over bespoke infrastructure.
Business rationale: Platform consistency improves supportability, resilience, automation, security integration, and cost transparency. It also reduces the number of unique skills and tooling stacks the organization must maintain.
Architectural implications: Engineering teams should default to approved cloud, hosting, observability, identity, and database services unless a nonstandard choice is justified by workload-specific needs. This also supports technology lifecycle governance: if a middleware product is in “retire” status, new solutions should not adopt it even if teams already know it well.
Scope: Enterprise-wide, with special review for business-critical and regulated workloads.
Evidence of compliance: Adoption of approved platform services, reduced bespoke infrastructure patterns, and lower operational variance across environments.
Trade-offs / exceptions: Legacy constraints, sovereignty requirements, or specialized performance needs may require alternatives, but those should be governed as exceptions.
5. Security Principle: Security is designed in, not added after deployment
Statement: Security, privacy, and control requirements must be addressed from the start of design and delivery.
Business rationale: Retrofitted security is more expensive, less effective, and more disruptive. Early integration reduces delivery risk and supports compliance, resilience, and trust.
Architectural implications: Solution designs should include threat assessment, identity design, data protection, logging, and control requirements early in the lifecycle. Security should be visible in design artifacts, not deferred to testing or operations. In practice, this often means modernizing IAM by adopting single sign-on, centralized policy enforcement, and role-based access before onboarding new business applications.
Scope: Enterprise-wide, with heightened rigor for regulated, customer-facing, and business-critical services.
Evidence of compliance: Early threat modeling, security requirements in design documentation, automated control checks, and reduced late-stage remediation.
Trade-offs / exceptions: Delivery urgency may pressure teams to defer some controls, but compensating controls and formal risk acceptance are required.
6. Integration Principle: Integrate through governed, reusable interfaces
Statement: Systems should exchange information through standardized, governed interfaces rather than point-to-point or database-level coupling.
Business rationale: Direct and inconsistent integration creates brittle dependencies, slows change, and increases replacement cost. Governed interfaces improve interoperability and architectural agility.
Architectural implications: Solution teams should expose capabilities through APIs, events, or approved integration services based on enterprise patterns. Direct database access and one-off file transfers should be treated as transitional and tightly controlled. In an event-driven architecture, for example, order, payment, and shipment updates may be published to Kafka topics with agreed schemas and ownership rather than exchanged through custom batch feeds.
Scope: Enterprise-wide, especially important in modernization and ecosystem integration programs.
Evidence of compliance: Increased use of approved integration patterns, reduced point-to-point connections, documented APIs and events, and lower integration remediation effort.
Trade-offs / exceptions: Transitional integrations may be necessary for legacy containment, but they should include an exit plan and clear ownership.
Taken together, these examples show how the template creates consistency across domains while staying grounded in practical decisions. They also illustrate an important point: principles are most effective when they can be applied quickly, without lengthy interpretation, during portfolio planning, design review, and exception handling.
How to Apply Enterprise Architecture Principles in Governance, Decision-Making, and Change Initiatives
Principles create value only when they are used at the points where organizations commit money, design choices, and delivery effort. The goal is not simply to publish a principle set, but to put it to work.
Embed principles into existing governance
Principles should be built into the forums that already shape enterprise decisions:
- investment boards
- portfolio reviews
- architecture review boards
- design authorities
- risk and control committees
- procurement evaluations
If a proposal introduces a new workflow platform, for example, the discussion should not begin with technical preference alone. It should be tested against the principles on capability reuse, platform standardization, authoritative data, governed integration, and security by design.
This creates coherence across governance forums and reduces a common problem: a project is approved financially, only to be challenged architecturally later. A typical architecture board decision might approve a local workflow tool for 12 months to meet a regulatory deadline, while requiring integration through enterprise APIs, use of central IAM, and a decommission plan aligned to the target platform.
Convert principles into governance questions
A practical way to operationalize principles is to convert each one into a small number of review questions. This builds directly on the template’s evidence of compliance element.
Examples include:
- Does this initiative duplicate an existing capability?
- Has the authoritative data source been identified?
- Does the solution use approved platform services?
- Are integrations aligned with governed interface patterns?
- Have security and privacy requirements been addressed in design?
- If there is a deviation, is it transitional and does it have an exit plan?
These questions make principles easier to use in steering committees, design checkpoints, and business case reviews.
Use principles in option analysis, not only final approval
Principles are most effective when applied early. Delivery teams often face choices such as:
- buy versus build
- centralize versus federate
- standardize versus customize
- extend an existing platform versus introduce a new one
Principles provide the lens for evaluating these trade-offs. A locally optimized option may look faster or easier in the short term, but still conflict with principles around reuse, interoperability, or supportability. Applying principles early helps teams avoid spending time on options that are unlikely to be approved or sustained.
Translate principles into program guardrails
Large initiatives such as cloud migration, ERP transformation, digital platform rollout, and merger integration generate too many design decisions for central architecture to review one by one. In these cases, enterprise architecture should derive initiative-specific guardrails from the principle set.
Examples might include:
- API-mediated integration only
- managed database services by default
- no new system of record without data governance approval
- no local process customization for defined core capabilities
- all customer-facing services must include identity and audit controls from day one
These guardrails allow teams to move quickly within clear boundaries. They are the program-level expression of the principles defined earlier.
Govern exceptions deliberately
Even strong principles will not fit every situation. Legacy constraints, contractual obligations, market deadlines, and regulatory requirements often force compromise. The key is to make those deviations visible and deliberate.
A sound exception process should capture:
- what principle is being deviated from
- why the deviation is necessary
- what risks it creates
- what compensating controls exist
- whether the deviation is temporary or permanent
- what remediation or exit plan applies
This distinguishes acceptable transitional debt from uncontrolled divergence and creates a feedback loop for refining principles over time.
Measure progress using principle outcomes
Principles should also influence how architecture value is measured across portfolios. Instead of tracking only project completion, organizations can assess whether change is improving the outcomes the principles were meant to drive, such as:
- greater platform reuse
- fewer duplicate applications
- clearer data accountability
- stronger integration consistency
- earlier security control adoption
- reduced operational variance
This turns principles from a passive review mechanism into an active way of steering enterprise change.
A healthcare provider, for example, might track whether new clinical applications are integrating through the enterprise API layer rather than direct database extracts. An insurer may measure how many customer-facing services have adopted central authentication and audit controls before production release. These are not abstract architecture metrics; they show whether the principles are changing delivery behavior. ArchiMate layers explained
Common Mistakes, Anti-Patterns, and Best Practices for Maintaining Principles
Once principles are defined and embedded, they still need active maintenance. Many organizations start with a strong principle set, then lose momentum because the principles are not reviewed, reinforced, or kept aligned with changing enterprise realities.
Common mistakes and anti-patterns
Too many principles
When the list grows too large, teams stop remembering it and governance becomes a checklist exercise. A principle set should stay small enough to be usable in live decision-making. Detailed controls belong in policies, standards, or reference architectures.
Principles as slogans
Statements like “We value innovation” or “Technology should support the business” may be true, but they do not resolve real trade-offs. Principles need rationale, implications, and evidence of compliance if they are going to be operational.
Frozen artifacts
Enterprises change. Acquisitions, regulatory shifts, platform strategy updates, and new delivery models can all make old principles less useful. If they are not reviewed, teams will either ignore them or work around them informally.
Unmanaged conflicts between principles
Reuse may conflict with speed. Standardization may conflict with local responsiveness. Data minimization may conflict with analytics goals. If these tensions are not acknowledged, governance starts to look inconsistent or political.
Separation from delivery reality
If only a central EA team maintains the principles, they can drift away from what engineering, data, security, and business teams can actually implement. Principles need stewardship, but they also need feedback from delivery.
Best practices for maintaining principles
Treat principles as a governed product
Each principle should have an owner, a review cadence, and a defined update process. Reviews should be infrequent enough to preserve stability but regular enough to reflect strategic change. An annual review, combined with event-driven updates after major shifts, is often effective.
Track exception patterns
Repeated exceptions are useful signals. They may point to poor compliance, weak enterprise capability, unrealistic governance, or a principle that no longer fits current conditions. Looking at exception patterns helps architecture teams respond with evidence rather than opinion.
Use practical examples to keep principles alive
Principles are easier to apply when teams see them used in real cases. Architecture teams should reinforce them with case studies, review findings, and examples of both successful alignment and costly deviation. A technology lifecycle review, for example, may reveal that teams keep requesting exceptions for an end-of-life integration product, signaling a need to accelerate the migration path.
Clarify precedence where conflicts are predictable
Not every conflict can be resolved in advance, but common tensions should at least be documented. For example, a regulated control requirement may take precedence over standardization speed, or a strategic market opportunity may justify temporary nonstandard tooling with an agreed exit plan.
Keep downstream artifacts aligned
Because principles sit above standards, patterns, and roadmaps, those downstream artifacts should be reviewed for alignment whenever principles change. Otherwise, teams receive mixed messages: the principle points one way, but standards and governance criteria still reflect an older direction.
Maintained in this way, principles remain stable in intent while adapting in application. That is what allows them to continue guiding enterprise evolution over time.
Conclusion
Enterprise architecture principles are most effective when they become part of how the enterprise makes decisions, not just part of how architecture documents are written. Their value lies in creating continuity across changing programs, technologies, and leadership priorities.
Strong principles are concise, business-aligned, and structured for use. They need a clear statement, a rationale, practical implications, evidence of compliance, and an explicit approach to trade-offs and exceptions. They should be derived from recurring enterprise decisions, tested against real scenarios, and embedded into the governance mechanisms that shape investment and design.
The example principles in this article show that an effective set does not need to be large. A small number of clear rules around process standardization, data ownership, capability reuse, platform strategy, secure-by-design delivery, and governed integration can guide a wide range of decisions when applied consistently.
The goal is not to eliminate flexibility. It is to create disciplined flexibility: enough freedom for teams to move quickly, but within boundaries that protect enterprise coherence. Used this way, principles do more than support architecture governance. They help the organization reduce complexity, protect strategic investments, and ensure that change adds up to a more coherent whole.
At that point, an enterprise architecture principles template becomes more than a documentation aid. It becomes a practical instrument for steering change at scale with consistency, transparency, and intent.
Frequently Asked Questions
What is enterprise architecture?
Enterprise architecture is a discipline that aligns an organisation's strategy, business processes, information systems, and technology. It provides a structured approach to understanding the current state, defining the target state, and managing the transition — using frameworks like TOGAF and modeling languages like ArchiMate.
How does ArchiMate support enterprise transformation?
ArchiMate supports transformation by modeling baseline and target architectures across business, application, and technology layers. The Implementation and Migration layer enables architects to define transition plateaus, work packages, and migration events — creating a traceable roadmap from strategy through to implementation.
What tools are used for enterprise architecture modeling?
The most widely used tools are Sparx Enterprise Architect (ArchiMate, UML, BPMN, SysML), Archi (ArchiMate-only, free), and BiZZdesign Enterprise Studio. Sparx EA is the most feature-rich — supporting concurrent repositories, automated reporting, scripting, and integration with delivery tools like Jira and Azure DevOps.