⏱ 27 min read
Structuring a Multi-Domain Sparx Repository for Banking Architecture Teams Sparx EA training
Learn how to structure a multi-domain Sparx repository for a banking architecture team, covering governance, domain separation, traceability, standards, and scalable enterprise architecture management. Sparx EA best practices
Sparx repository, multi-domain architecture, banking architecture, enterprise architecture, Sparx EA, repository structure, architecture governance, banking IT, domain modeling, traceability, architecture standards, enterprise repository, solution architecture, banking technology, architecture team how architecture review boards use Sparx EA
Introduction
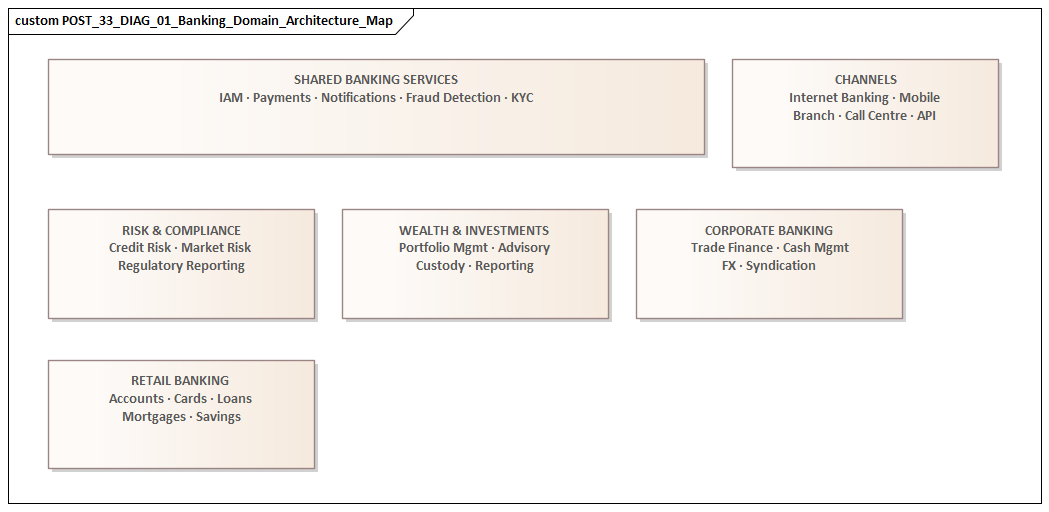
In a banking architecture team, a Sparx Enterprise Architect repository is not just a diagram store. It becomes a shared working environment for business, application, data, technology, security, and regulatory architecture. Once several disciplines are using the same repository, structure is no longer a housekeeping matter. It becomes a practical control. It determines whether the model supports reuse, traceability, governance, and delivery—or whether it gradually fills with duplicates, local variants, and disconnected views. ARB governance with Sparx EA
That matters in banking because change rarely stays inside one domain. A payments modernization, onboarding redesign, IAM uplift, or core platform migration can affect capabilities, processes, applications, interfaces, data classifications, hosting patterns, resilience controls, and regulatory obligations at the same time. Different stakeholders need different views of that change, but those views still have to point back to the same enterprise objects. Without that common foundation, impact analysis slows, governance becomes inconsistent, and confidence in what is authoritative starts to erode. EA governance checklist
A well-structured repository therefore has to balance control with usability. Shared enterprise concepts—business capabilities, applications, data entities, technology platforms, control objects—need a governed home so they can be reused consistently. At the same time, domain teams and initiative teams need space to develop their own views, model transition states, and work at delivery pace without constantly redefining shared content. The repository should make the right behavior the easy behavior: find the authoritative object, reference it, extend it in the correct place, and preserve traceability.
Structure also shapes behavior. If reuse is awkward, teams copy elements. If ownership is vague, maintenance slips. If lifecycle and governance metadata are treated as optional, the repository becomes fragile just when architecture reviews, audits, or investment decisions need evidence. Repository design should therefore be treated as an architectural control in its own right. It influences not only how content is stored, but how architecture is practiced across the bank. ADR template
The most effective repositories are built on a small set of durable principles. First, separate enterprise reference content from domain detail and initiative-specific work. Second, define clear ownership and stewardship for shared objects. Third, standardize modeling, naming, and metadata enough to support cross-domain analysis. Fourth, embed the repository in delivery and governance processes so it becomes part of normal operations rather than an optional extra.
The sections that follow show how to apply those principles in practice: defining governance, designing package hierarchy, enforcing reuse, managing security and regulatory traceability, connecting the repository to change processes, and evolving it over time without losing coherence.
Why a Multi-Domain Sparx Repository Matters in Banking Architecture
Banking change rarely sits neatly within one architectural layer. Even a focused initiative, such as replacing a customer onboarding platform, can ripple across business processes, product rules, customer data, integration services, hosting patterns, identity controls, operational resilience requirements, and reporting obligations. A multi-domain repository matters because it makes those relationships visible in one structured environment instead of leaving them scattered across slide decks, spreadsheets, and individual memory.
The most immediate benefit is impact analysis. Architecture teams are constantly asked questions such as:
- Which applications support this capability?
- Which data objects are affected by this change?
- Which interfaces will be disrupted if a platform is replaced?
- Which controls need review if a workload moves to cloud hosting?
- Which target-state commitments or standards are affected by a proposed exception?
Those questions are difficult to answer consistently when business, application, data, technology, and security models are maintained separately. A shared repository allows architects to trace change across domains using governed objects and defined relationships.
Governance is the other major reason. Portfolio boards, design authorities, and risk forums need more than a project description. They need to know whether a proposal aligns with target architecture, duplicates existing capability, introduces new risk, or creates dependencies for other programs. A repository that spans domains gives those forums a stronger evidence base. Instead of debating from disconnected documents, architects can show that a proposed solution reuses an existing service, depends on regulated data, requires a mandated resilience pattern, or overlaps with an enterprise capability already on the roadmap.
A simple example is IAM modernization. A program may propose moving retail and corporate channels onto a central identity platform. In the repository, that change can be traced from customer access capabilities to channel applications, authentication services, privileged-access controls, regulated processes, and target hosting platforms. The architecture board can then approve phased adoption while explicitly retaining legacy privileged-access tooling until segregation-of-duties controls are proven.
A multi-domain repository is equally important because banks operate in layered estates rather than clean target environments. Strategic platforms sit alongside legacy systems, regional variants, tactical workarounds, and outsourced services. Architects need to represent not only ideal target states but also transition states, tolerated exceptions, and decommissioning paths. When those relationships are maintained in one repository, transformation can be modeled more realistically. An interim consolidation, for example, may be acceptable only if data lineage is preserved, controls remain effective, and servicing commitments are maintained.
There is also a team-level benefit. Banking architecture functions are usually divided into specialist roles, but major initiatives demand integrated reasoning. Business architects need to connect capabilities and value streams to real systems. Solution architects need to link interfaces and dependencies back to enterprise standards. Data architects need to understand which applications create or consume critical information. Security architects need to map controls to services, platforms, and trust boundaries. A shared repository provides that common working surface without forcing every discipline into the same level of detail.
It also strengthens institutional memory. Banking programs often run for years, while staff, suppliers, and priorities change around them. Decisions made during mobilization reappear later during implementation, remediation, audit, or post-merger rationalization. If the rationale, dependencies, and lifecycle of the relevant architecture objects have been captured in a governed repository, the bank is less dependent on individuals remembering why a choice was made.
In that sense, the repository becomes more than a modeling tool. It becomes a durable decision asset. That is why its internal structure matters so much: if the structure is weak, the repository cannot provide the traceability and trust that make it valuable.
Repository Governance, Ownership, and Operating Model
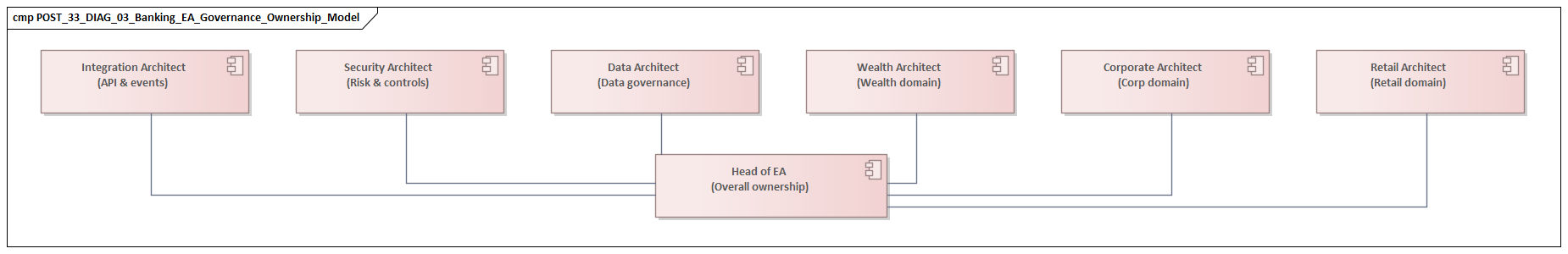
If the repository is to function as a durable decision asset, governance has to be designed as deliberately as the package structure. In practice, repositories usually fail not because the tool lacks capability, but because no one is clear who can create, change, approve, and retire content. Once that ambiguity sets in, shared objects are duplicated, diagrams become misleading, and ownership starts to drift.
A practical operating model defines ownership at three levels:
- Repository ownership for standards, conventions, access, and quality control
- Domain ownership for authoritative content within business, application, data, technology, security, and related domains
- Initiative ownership for project or program views, transition models, and solution-specific elaboration
This three-level split creates the balance between central control and team autonomy. Repository-level stewardship, often held by enterprise architecture or architecture operations, maintains the rules of the environment: package conventions, naming standards, meta-model usage, lifecycle states, and access controls. Domain stewards maintain the integrity of reusable enterprise objects in their own area. Initiative architects consume those objects, add delivery-specific relationships and views, and propose changes where enterprise content needs to evolve.
That distinction is especially important in banking because most initiatives touch shared assets. A payments change may affect applications, customer data, integration services, infrastructure zones, and control requirements, but it should reference the governed versions of those objects rather than create local substitutes. The operating model therefore has to make reuse easier than duplication.
In practice, this usually means:
- broad read access to authoritative enterprise content
- controlled write access for stewards of shared packages
- clearly defined working areas for initiative teams
- a lightweight promotion path from working content into governed domain content
Promotion into authoritative packages should be visible and deliberate, but not bureaucratic. If the process is too heavy, teams work around it. If it is too loose, trust in the repository weakens.
A RACI-style governance model is often effective:
- Responsible: domain stewards for maintaining content
- Accountable: architecture leadership or governance boards for major structural decisions
- Consulted: project and solution architects
- Informed: wider consumers such as portfolio, risk, and governance stakeholders
Formal boards matter, but they are not enough. Day-to-day control is better enforced through embedded quality checks: mandatory metadata, review workflows for changes to shared objects, and periodic scans for duplicates, broken relationships, orphaned elements, and stale content. In banking, those controls are valuable because architecture evidence is often needed at short notice for investment reviews, audits, and regulatory responses.
The operating model should also reflect different levels of control for different content types. Some assets need strong stewardship because they are widely reused and influence governance outcomes. These usually include:
- business capability maps
- application inventory objects
- core data entities and classifications
- technology standards and platform definitions
- security controls and policy mappings
Other content can be handled more flexibly, provided it is clearly temporary or local in scope. Examples include exploratory solution options, initiative working diagrams, and short-lived transition views. That distinction helps avoid over-governing early design while still protecting the integrity of enterprise reference content.
To make governance workable, repository users need simple cues. Each important object should make it easy to see:
- who owns it
- whether it is current, target, or transitional
- when it was last reviewed
- whether it is authoritative or local
- how change should be requested
These conventions matter because governance only works when it supports day-to-day delivery instead of obstructing it. The repository should feel like a managed service for the architecture community: protecting trust in shared content while still allowing domain and initiative teams to move at speed.
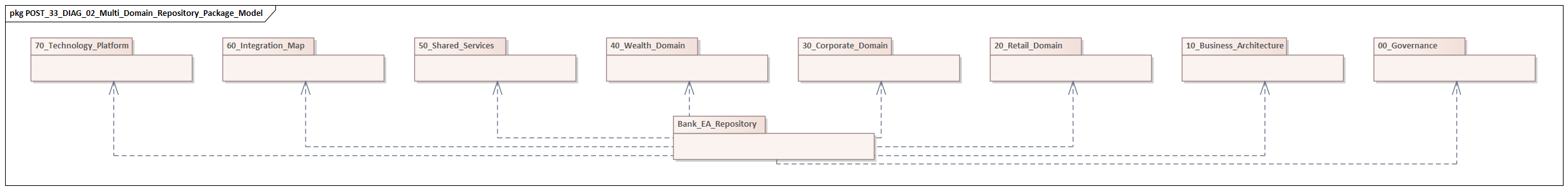
Designing the Domain Structure and Package Hierarchy
Once ownership is clear, the next question is how to organize the repository so users can find and reuse content without guesswork. The most durable pattern is to separate enterprise reference content, domain detail, and initiative-specific work. That principle should drive the package hierarchy from the start.
A practical top-level pattern is to divide the repository into four major zones:
- Enterprise reference architecture
- Domain architecture
- Initiatives and solutions
- Governance and decisions
This is not the only valid structure, but it works well in banking because it separates enduring enterprise objects from specialist elaboration and temporary project work.
1. Enterprise reference architecture
This zone contains the reusable, authoritative objects that should exist once and be referenced widely. Typical examples include:
- business capabilities
- application inventory
- core business services
- conceptual and logical data entities
- technology platforms and standards
- security principles, controls, and trust zones
- regulatory obligations or policy references where maintained architecturally
These are the assets most likely to support impact analysis, governance, and cross-initiative reuse. They therefore need the strongest stewardship.
2. Domain architecture
This zone contains detailed domain-owned viewpoints and relationships. For example:
- business architecture: capability maps, value streams, processes, products
- application architecture: services, interfaces, dependencies, lifecycle models
- data architecture: information domains, lineage, classifications, critical data elements
- technology architecture: environments, platforms, standards, patterns
- security architecture: controls, trust boundaries, identity dependencies, assurance views
This area gives each discipline room to work at the depth it needs without overloading the enterprise reference layer. For example, an event architecture package may contain Kafka topics, producers, consumers, schemas, and retention patterns, while the enterprise layer contains the shared event-streaming standard and approved platform object.
3. Initiatives and solutions
This zone supports change delivery. It typically includes:
- solution context diagrams
- option assessments
- transition architectures
- program-specific impact models
- delivery views and implementation relationships
The key rule is straightforward: initiative packages should consume and reference enterprise objects rather than redefine them.
4. Governance and decisions
Many teams benefit from a dedicated area for:
- architecture principles
- standards decisions
- review outcomes
- exceptions and waivers
- roadmaps and target-state commitments
This preserves decision context, especially where architecture governance depends on traceable rationale. For instance, a decision record might state that Kafka is the strategic event backbone for domain events, while point-to-point file transfer remains tolerated only for defined legacy flows until retirement dates are reached.
How to Structure Within Domains
Within each domain, hierarchy should reflect how architects actually search for and reuse information. It should not become deep merely to satisfy taxonomy. A good structure answers practical questions quickly: where is the master application object, where should an interface be modeled, where does a target-state capability view belong?
Examples:
- Business architecture: capabilities, value streams, processes, products, organizational mappings
- Application architecture: applications, services, interfaces, deployments, lifecycle states
- Data architecture: entities, data objects, information flows, classifications, lineage
- Technology architecture: platforms, environments, standards, patterns, infrastructure relationships
- Security architecture: controls, trust zones, identity services, security patterns, obligations
Predictability matters more than perfect classification. If users have to interpret the structure every time they navigate it, they will eventually create shortcuts outside it.
Keep Authoritative Objects in One Place
One of the most important design rules is to keep the master object at the highest reusable level. A core payments engine, for example, should exist once in the governed application portfolio package. Project teams can reference it in their own diagrams, add transition relationships, and create local views, but they should not create a second master version inside a program folder.
The same principle applies to:
- business capabilities
- data entities
- integration services
- technology products
- control objects
This is the simplest way to reduce duplication and preserve traceability.
A common micro-example is customer data. The enterprise data package should contain one authoritative Customer entity, with agreed classification and ownership. A mortgage transformation program may create a local view showing Customer, Application, and Property, but it should not create a second enterprise-level Customer Record object simply because its delivery team uses that phrase operationally.
Domain-First vs Business-Area-First
Banks often debate whether the repository should be structured by architecture domain or by business segment such as retail, cards, lending, or treasury. For repository integrity, domain-first is usually the stronger choice because it preserves consistent stewardship of shared concepts. Business-area perspectives can then be represented through:
- views
- matrices
- tagged classifications
- cross-references
- filtered reports
That approach avoids fragmenting the same application or data object across multiple line-of-business folders.
Distinguish Current, Target, and Transition States
State management should be visible either in the structure or in the metadata. Users need to distinguish current state, target state, and transition state clearly. In banking, where programs can run for years, confusion between implemented reality and strategic intent quickly undermines trust.
This can be handled through:
- dedicated sub-packages
- controlled status fields
- time-bound transition views
- lifecycle metadata linked to governance dates
Whichever method is chosen, consistency across domains matters more than the mechanism. This is particularly important for technology lifecycle governance. A database platform may be marked as Current for existing workloads, Restricted for new use, and Retire by Q4 2027 for governance and planning purposes. Similarly, a card-switch interface may be current in production, target for replacement, and transitional where a coexistence pattern remains approved for a fixed period.
A strong package hierarchy is therefore more than tidy storage. It makes reuse, ownership, and state clarity visible in everyday architecture work.
Standards for Modeling, Naming, and Reuse Across Domains
A sound hierarchy is necessary, but it is not enough. Architects can still create inconsistent content inside the correct package. To support cross-domain analysis, the repository needs practical standards for modeling, naming, metadata, and reuse.
Define a Small Working Meta-Model
Sparx is flexible, but most teams should resist the temptation to model everything it can represent. A better approach is to define a small, usable meta-model that captures the core enterprise relationships consistently.
For example, the team may agree that:
- business capabilities are realized by applications
- applications expose services
- services exchange data objects or events
- applications are hosted on technology platforms
- controls apply to services, platforms, data classes, or processes
The exact relationship set will vary, but consistency is the critical point. If one team uses arbitrary associations and another uses defined relationship types, repository analytics and impact views become unreliable.
A small meta-model also reduces training effort and makes quality easier to enforce. Architects know which connector to use and why. Governance forums can interpret the results with more confidence. ArchiMate layers explained
Standardize Naming
Names determine whether users can find and trust shared content. Naming standards should clearly distinguish enterprise concepts, systems, and implementation details.
Examples:
- Business capability: stable enterprise ability such as
Customer Onboarding - Application: authoritative system name such as
Payments Hub - Service: clear business-oriented or verb-noun name
- Data entity: singular business term such as
Customer,Account,Payment Instruction
Naming standards should also address abbreviations, regional variants, and legal-entity qualifiers where relevant. The goal is readability first, supported by enough consistency to make search, filtering, and reporting reliable.
Make Metadata Mandatory for Key Objects
The repository becomes operationally useful when key objects carry enough metadata to support governance without requiring teams to reconstruct context manually.
Typical mandatory fields include:
- owner
- lifecycle status
- current/target/transitional state
- review date
- criticality
- regulatory relevance
- source of truth
By object type, additional fields may include:
- Applications: vendor, deployment model, resilience tier, strategic disposition
- Data objects: classification, retention relevance, system of record
- Technology components: standards status, hosting pattern
- Controls: policy linkage, assurance owner, applicability scope
These standards reinforce the principle that the repository should support evidence-based governance, not just diagram production.
Define Explicit Reuse Rules
Reuse does not happen consistently unless it is governed. Teams should be expected to:
- search before creating
- reference before copying
- request updates to governed objects rather than creating substitutes
For certain high-value object types, duplicate creation should be strongly restricted outside governed packages. These usually include:
- business capabilities
- applications
- core data entities
- technology products
- security controls
If a project needs a local variation, it should usually create a view, instance, or transition relationship rather than a new enterprise object.
This matters especially in banking because duplicated master objects weaken rationalization, cost analysis, dependency mapping, and control traceability. If one payments program models Payments Hub and another creates Enterprise Payments Platform as a separate master object for the same system, application portfolio reporting and impact analysis will quickly become unreliable.
Keep Standards Lightweight
Standards only work when they remain usable under delivery pressure. The most effective teams support them with:
- templates
- example diagrams
- quick-reference guides
- preconfigured stereotypes
- simple review checklists
Review should focus on whether content is reusable and traceable, not whether a diagram looks polished. The standard is working when an architect can produce governance-ready content quickly and another architect can understand and reuse it later without additional explanation.
Security, Access Control, and Regulatory Traceability
A banking repository contains shared enterprise objects, governed domain content, and initiative-specific work. Access design therefore has to protect sensitive information without breaking cross-domain visibility.
Separate Visibility, Edit Rights, and Stewardship
Access should not be treated as a simple open-or-closed decision. Most architecture users need broad read access to authoritative content, because traceability loses value if only a small group can see dependencies. Write access, however, should be controlled, especially for objects that influence governance outcomes.
A practical approach is to separate:
- Visibility: who can see content
- Edit rights: who can change it
- Stewardship rights: who can approve or maintain authoritative versions
This aligns directly with the ownership model described earlier.
Typical restricted areas may include:
- security architecture detail
- audit or remediation content
- third-party risk mappings
- sensitive resilience designs
- regulatory response materials
Protect Sensitive Views as Well as Sensitive Objects
In banking, sensitivity often lies not only in an object itself but in how several objects are combined in a view. A high-level capability map may be broadly shareable, while a detailed diagram showing trust boundaries, privileged access paths, encryption dependencies, or failover design may require tighter restriction. capability map template
For that reason, access control should consider both:
- package and element sensitivity
- diagram or viewpoint sensitivity
This helps keep one connected repository without pushing security-relevant architecture into separate stores.
Build Regulatory Traceability into the Model
Banks are frequently asked to show how change aligns with policy obligations, control requirements, resilience expectations, or data handling rules. The repository should support this directly.
A useful pattern is to maintain a controlled library of:
- regulatory obligations
- internal policies
- standards
- control statements
These can then be linked to relevant architecture elements such as:
- business processes
- applications
- data objects
- interfaces
- technology platforms
- solution decisions
This does not turn the repository into a legal register. Its value is architectural: showing which parts of the estate are affected, where obligations are implemented, and where evidence or remediation is still needed.
Make Traceability Useful in Change Scenarios
Regulatory traceability is most valuable when it helps answer real delivery questions. If a payment service moves to a new hosting model, the team should be able to identify not only the technology impact but also related:
- resilience requirements
- data residency constraints
- identity and access controls
- logging obligations
- third-party risk implications
Likewise, if a policy interpretation changes, the repository should help identify the affected applications, processes, and data flows quickly. In an IAM modernization, this might mean tracing which applications still depend on local directories, which privileged roles map to regulated processes, and which customer channels require step-up authentication.
Another realistic example is cloud migration for a fraud analytics workload. The application architecture view may show the target cloud platform and new event ingestion path; the data architecture view identifies customer transaction data classes; the security domain links encryption and key-management controls; and the regulatory traceability layer highlights residency and monitoring obligations. Without those connected objects, the design review becomes guesswork.
Keep Security and Traceability Practical
Security and compliance controls should be embedded in normal modeling practice, not added later as procedural overhead. Useful mechanisms include:
- mandatory classification fields
- standard tags for sensitive diagrams
- controlled vocabularies for policy mappings
- reusable relationship patterns
- focused review workflows
Well-designed controls do not slow architecture down. They make the repository dependable enough to support governance, assurance, and regulatory response with confidence.
Integrating the Repository with Delivery, Change, and Architecture Governance Processes
A structured repository only creates value when it is embedded in how the bank delivers change. If it sits outside delivery and governance as an optional reference source, it becomes descriptive rather than operational.
Use the Repository at Initiative Intake
When a new initiative enters the portfolio, architects should anchor it to existing enterprise objects rather than start from a blank page. Even at concept stage, the initiative should link to:
- impacted capabilities
- affected applications
- relevant data domains
- target platforms
- applicable standards or controls
This creates an early architectural footprint for the change and allows the team to identify overlap, dependency, and strategic alignment quickly.
Support Progressive Design Elaboration
As initiatives mature, the repository should support staged refinement. Early context views can evolve into more detailed models of interfaces, data usage, deployment patterns, control mappings, and transition states.
That matters because architecture certainty increases over time. Vendor selection, regulatory interpretation, and legacy constraints often remain unresolved early in a program. The repository should therefore support progressive, traceable elaboration rather than only final-state documentation.
Use Repository Content Directly in Governance
Design authorities, investment forums, and risk committees should assess proposals using repository-backed evidence wherever possible. Reviews should be able to show:
- what enterprise assets are reused
- what standards are applied or breached
- what target-state dependencies are introduced
- what control obligations are relevant
- what exceptions or conditions are attached
This improves consistency because decisions are based on connected model content rather than bespoke slide packs. For example, a design authority reviewing an event-driven payments initiative might approve Kafka for internal domain events, but require synchronous APIs to remain for real-time balance checks and impose a condition that topic schemas use the bank’s canonical payment event model.
It also creates a durable record of what was reviewed and why a decision was made.
Connect Architecture to Change Control
In many banks, architecture review happens early, but later delivery changes are handled with limited architectural visibility. That creates a gap between approved design intent and implemented reality.
A stronger model is to treat the repository as the reference point for architecturally significant changes. Examples include:
- new interfaces
- hosting changes
- new data usage
- control deviations
- substitution of approved technologies
Not every sprint-level adjustment requires formal review, but there should be clear thresholds for when architecture updates and governance re-engagement are mandatory.
Track Transition and Delivery Outcomes
Where possible, roadmaps, milestones, and decommissioning commitments should be linked to the affected architecture objects. This allows the architecture team to see whether implementation is moving the estate toward the intended target state or simply adding more complexity.
This is especially useful in banking, where interim states often last longer than expected. The repository can help distinguish controlled transition architecture from unmanaged drift. For example, if a branch servicing platform is meant to be retired after digital onboarding rollout, the associated application objects, interface dependencies, and closure milestones should show whether that retirement is still on track or quietly slipping.
Make Integration Lightweight
Integration works best when repository use is built into existing delivery habits rather than added as extra administration. Effective mechanisms include:
- intake templates that require repository references
- review checkpoints that pull model evidence
- change processes that define architecture update triggers
- closure processes that update lifecycle and transition status
The repository should make governance faster and clearer, not create duplicate documentation effort.
Scaling, Maintaining, and Evolving the Repository Over Time
A repository that works for a small architecture team may not work once the model expands across portfolios, regions, controls, and transformation programs. Scaling requires operational discipline, not just a good initial design.
Manage Volume Actively
As repositories grow, navigation becomes harder and duplicate risk increases. Regular housekeeping is therefore essential. The team should routinely check for:
- stale diagrams
- duplicate elements
- broken links
- orphaned objects
- missing metadata
- expired transition views
Small, continuous maintenance is more effective than occasional large cleanup exercises because it preserves trust in the repository.
Protect Performance and Usability
Large repositories can become slow and awkward to use. When that happens, architects often move work outside the tool, which weakens the operating model.
Scalable practices include:
- limiting unnecessary package depth
- encouraging focused diagrams instead of “everything views”
- archiving obsolete working areas
- separating active content from historical reference material where needed
- avoiding uncontrolled attachment of heavy documents
Usability is not a cosmetic issue. If the repository is cumbersome, standards and governance will be bypassed.
Evolve the Meta-Model Carefully
No team gets the model structure exactly right at the start. New needs will emerge over time, such as:
- operational resilience mapping
- cloud service taxonomies
- third-party dependency modeling
- AI governance artifacts
- more detailed control-to-technology relationships
These additions should be introduced as controlled increments with clear purpose, guidance, and migration rules. If new stereotypes, tags, or relationship types are added ad hoc, repository semantics fragment and cross-domain consistency weakens.
Extend Use Cases in Stages
As the architecture function matures, the repository may begin to support additional use cases such as:
- portfolio rationalization
- technical debt tracking
- standards compliance reporting
- control coverage analysis
- decommissioning oversight
These are valuable extensions, but they should be introduced gradually. If the repository is overloaded with every governance demand at once, maintenance becomes unrealistic and quality falls.
Match Scope Growth with Stewardship Capacity
Growth in model scope must be matched by growth in stewardship. New domains or reporting needs should not be added without:
- named owners
- review routines
- training
- operational support
- retirement rules for obsolete content
Retirement rules are especially important. The repository should explicitly show when initiatives close, transition architectures expire, standards are superseded, and legacy assets are decommissioned. Otherwise, historical clutter accumulates and users lose confidence in what is current. This is where technology lifecycle governance becomes practical rather than theoretical: if a messaging product is marked as retiring, new solution packages should not be allowed to adopt it, and existing dependencies should remain visible until exit plans are complete.
Ultimately, a scalable repository is not the one that contains the most content. It is the one that preserves clarity about what is authoritative, current, transitional, and retired as the banking environment evolves.
Conclusion
Structuring a multi-domain Sparx repository in a banking architecture team is fundamentally about creating institutional coherence. The repository has to support more than modeling. It needs to support coordinated decision-making across strategy, delivery, governance, control, and operations. Sparx EA guide
The core principles are consistent throughout. Separate enterprise reference content from domain detail and initiative work. Define clear ownership and stewardship. Standardize modeling, naming, metadata, and reuse. Protect sensitive content while preserving cross-domain visibility. Integrate the repository into delivery and governance processes. Evolve it deliberately as scope and complexity grow.
When those principles are applied well, architects can distinguish authoritative enterprise objects from local working material, current state from target state, and governed reference content from temporary transition models. That clarity is what allows the repository to support impact analysis, architecture review, audit response, and long-running transformation without constant reconstruction of context.
In the long run, success is not measured by the number of diagrams produced. It is measured by whether the repository is trusted and used. Can architects find the right object quickly? Can initiatives show traceable impact across domains? Can governance forums make decisions from connected evidence? Can the bank revisit a past decision and still understand its rationale and dependencies?
If the answer is yes, then the repository is doing more than storing models. It is functioning as a durable architecture capability for the bank.
Frequently Asked Questions
What is enterprise architecture?
Enterprise architecture is a discipline that aligns an organisation's strategy, business processes, information systems, and technology. It provides a structured approach to understanding the current state, defining the target state, and managing the transition — using frameworks like TOGAF and modeling languages like ArchiMate.
How does ArchiMate support enterprise transformation?
ArchiMate supports transformation by modeling baseline and target architectures across business, application, and technology layers. The Implementation and Migration layer enables architects to define transition plateaus, work packages, and migration events — creating a traceable roadmap from strategy through to implementation.
What tools are used for enterprise architecture modeling?
The most widely used tools are Sparx Enterprise Architect (ArchiMate, UML, BPMN, SysML), Archi (ArchiMate-only, free), and BiZZdesign Enterprise Studio. Sparx EA is the most feature-rich — supporting concurrent repositories, automated reporting, scripting, and integration with delivery tools like Jira and Azure DevOps.