⏱ 24 min read
Enterprise Architecture for Cloud Migration Programs: Strategy, Governance, and Target-State Design architecture decision records
Learn how enterprise architecture enables successful cloud migration programs through target-state design, governance, application rationalization, security alignment, and roadmap planning. how architecture review boards use Sparx EA
enterprise architecture, cloud migration, cloud migration program, target-state architecture, cloud strategy, application rationalization, cloud governance, migration roadmap, cloud operating model, security architecture, hybrid cloud, technology modernization, IT transformation, architecture governance, cloud adoption framework architecture governance checklist
Introduction
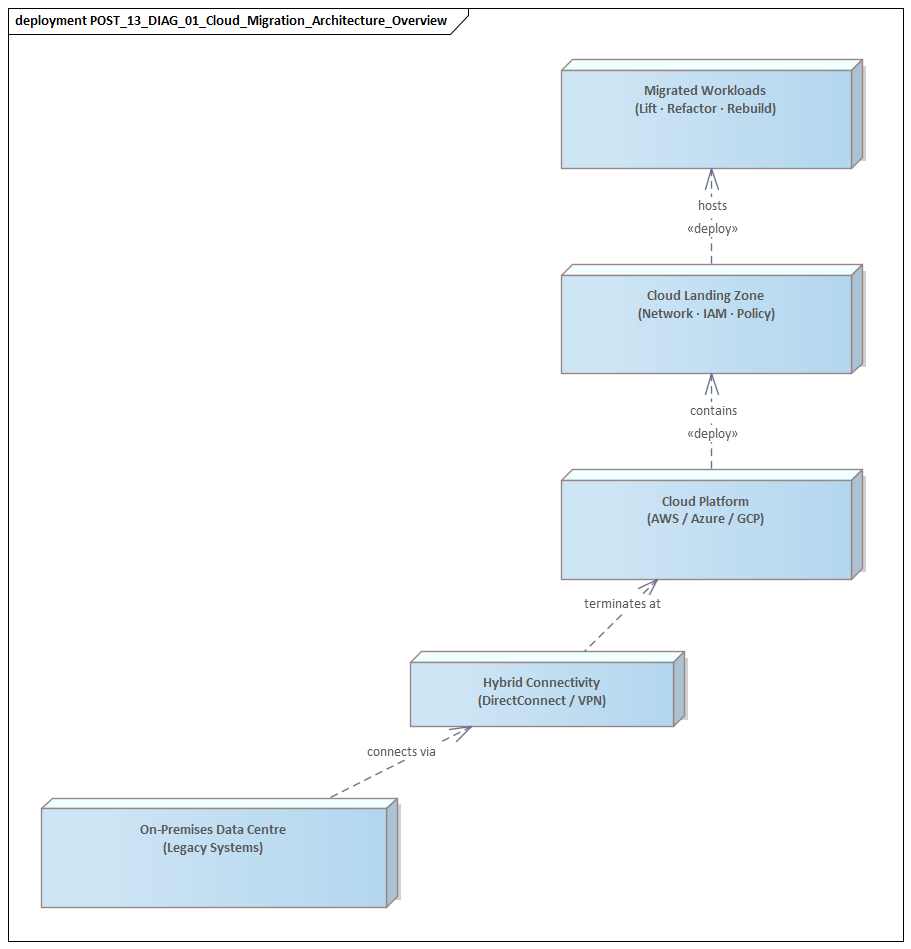
Cloud migration is seldom just a hosting change. In most enterprises, it becomes a broader transformation effort that affects the application portfolio, operating model, governance, security, financial management, and delivery practices. That is why enterprise architecture matters from the start. It aligns migration with business priorities and helps prevent a series of disconnected decisions that simply recreate existing complexity on a new platform.
Many migration programs begin under pressure. A data center lease is nearing expiry, infrastructure is aging, resilience expectations have increased, or a merger has expanded the estate. Those are legitimate catalysts. They are not, by themselves, a strategy. When business units and delivery teams move independently, the outcome is often predictable: duplicated platform services, inconsistent security controls, poorly sequenced dependencies, and rising operating costs. Enterprise architecture reduces that risk by establishing target-state principles, transition architectures, and decision frameworks that allow teams to move at pace without losing coherence.
It is also useful to treat cloud migration as a portfolio problem rather than a set of isolated technical projects. Every workload carries a different combination of business value, risk, dependency complexity, and modernization potential. Some applications can be rehosted quickly. Others need refactoring to meet resilience, performance, or integration requirements. Some should be replaced—or retired—rather than migrated at all. Enterprise architecture provides the structure for making those distinctions consistently and linking them to business outcomes.
Cloud environments are operating ecosystems, not just infrastructure platforms. Identity, network topology, landing zones, observability, data residency, encryption, backup patterns, and service management integration all require deliberate design before migration accelerates. If those foundations are weak, early progress is usually offset by rework, inconsistent controls, and avoidable cost. Architecture establishes the baseline capabilities that make migration repeatable, secure, and governable across teams.
Cloud also changes the economics of technology. Consumption-based services and managed platforms can increase agility, but they demand stronger discipline in cost transparency, platform engineering, and lifecycle governance. Enterprise architecture connects technical choices to financial and operational consequences, helping leaders decide where standardization is essential and where flexibility creates genuine value.
In this setting, enterprise architecture is not a parallel documentation exercise. It is the mechanism for shaping decisions, sequencing change, and balancing short-term delivery pressure against long-term sustainability. The sections that follow examine how architecture supports the business case, assesses the current estate, defines the target operating model, governs migration patterns, embeds control by design, and ensures value is realized after workloads move.
1. Strategic Drivers and the Business Case
A credible cloud migration program starts with a clear statement of why the enterprise is moving, what outcomes it expects, and how success will be measured. Without that foundation, migration can quickly become a technology-led initiative justified by generic claims about agility or cost reduction. Enterprise architecture brings discipline to this discussion by tying migration choices to business priorities rather than platform preference.
In many organizations, the initial trigger is straightforward: aging infrastructure, expiring data center contracts, hardware refresh avoidance, or the need to reduce technical debt. All are valid drivers. But if they dominate the case, the program can become narrowly focused on infrastructure savings. An architecture-led perspective broadens the discussion. It asks how cloud capabilities might support faster product delivery, stronger disaster recovery, better data accessibility, shorter environment provisioning times, and more scalable integration patterns. The conversation shifts from where systems run to what the business can do differently once they move.
Enterprise architects also help separate strategic drivers from assumed benefits. Cloud does not automatically reduce cost, and moving applications without changing delivery or operating practices does not automatically improve agility. The business case therefore needs to distinguish between three forms of value: Sparx EA best practices
- Direct benefits, such as reduced capital expenditure, data center exit savings, or lower provisioning effort
- Indirect benefits, such as improved developer productivity, reduced outage impact, or faster onboarding of acquired businesses
- Enabling benefits, such as reusable platforms, standardized security controls, and API-based integration that support later transformation
That distinction matters. Cloud programs often overstate direct savings and undervalue enabling capabilities. Architecture helps leaders make more realistic investment decisions by showing which benefits should appear quickly, which will emerge over time, and which depend on capabilities that must be built first.
The business case should also operate at more than one level. At the enterprise level, leadership needs a view of strategic outcomes, investment profile, operating model implications, and major risk reduction. At the portfolio level, decision-makers need workload segmentation showing which applications should be rehosted, refactored, replaced, retained, or retired. At the initiative level, delivery teams need migration hypotheses tied to measurable outcomes such as deployment frequency, recovery time, latency, or cost-to-serve.
Architecture also exposes constraints that can materially change both economics and sequencing. Licensing terms, data sovereignty requirements, latency-sensitive integrations, vendor dependencies, and legacy support arrangements can all reshape the business case. A claims platform, for example, may be approved for rehosting to meet a data center exit date, while its planned modernization is deferred because proprietary database licensing and batch dependencies would otherwise erase the expected savings.
In another common scenario, a manufacturer may initially frame cloud migration around infrastructure consolidation. Portfolio analysis then shows that the larger benefit lies elsewhere: moving plant analytics and quality reporting onto a shared cloud data platform shortens reporting cycles from overnight to near real time. The infrastructure move still matters, but the real business case shifts toward operational visibility and faster decision-making on the factory floor.
A final contribution from architecture is the definition of value realization milestones. Because migration programs often run for several years, benefits cannot be deferred to a distant end state. Interim milestones might include establishing a secure landing zone, reducing environment build time through automation, consolidating identity services, or migrating development and test workloads ahead of production systems. These milestones provide evidence that the program is progressing toward the outcomes defined in the case. Sparx EA training
The business case, then, is more than a funding document. It is the first architecture artifact that links strategy, economics, and delivery logic. The next step is to test that logic against the reality of the current estate.
2. Current-State Assessment and Application Portfolio Analysis
Before defining migration waves or selecting target services, enterprise architecture needs a reliable view of the current environment. Weak baseline knowledge is one of the most common causes of delay, rework, and unexpected risk in cloud programs. Application inventories are often incomplete, ownership may be unclear, interfaces undocumented, and infrastructure records may describe components without showing how they support business capabilities. A current-state assessment turns that uncertainty into decision-ready evidence. free Sparx EA maturity assessment
The objective is not exhaustive documentation. Architecture exists to improve decision quality, not to produce paperwork. Current-state analysis should gather the information needed to make migration choices with confidence. That usually includes application purpose, business criticality, lifecycle status, deployment model, data classification, integration dependencies, peak usage patterns, resilience requirements, technology stack, support arrangements, and regulatory obligations. Architects also need to understand where duplication exists, which platforms are nearing end of life, and which systems are tightly coupled to on-premises infrastructure or specialized appliances.
Portfolio analysis becomes useful when it moves beyond inventory into segmentation. Not all applications are equally suitable for migration. Some are strategic differentiators that justify modernization investment. Others are commodity capabilities better replaced with SaaS. Some are stable but low-value legacy systems that should simply be contained until retirement. A practical architecture approach classifies applications across several dimensions:
- business value
- technical health
- operational risk
- dependency complexity
- data sensitivity
- change readiness
This multidimensional view supports rational pathway selection rather than decisions driven by executive preference or technical enthusiasm.
Dependency mapping is particularly important. Migration often fails when applications are assessed one by one but moved within tightly coupled ecosystems. Interfaces with identity services, shared databases, file transfer platforms, reporting tools, batch schedulers, and network-bound integrations can all change sequencing decisions. In practice, the sensible migration unit is often not a single application but a service group, business domain, or dependency cluster. A customer onboarding application may appear to be a simple rehost candidate until assessment reveals hard dependencies on an on-premises LDAP directory, a nightly ETL job, and a shared integration broker. That usually changes both the target pattern and the migration wave.
Operational characteristics matter as much as architecture diagrams. Teams should understand incident history, recovery procedures, release frequency, monitoring coverage, manual support effort, and known performance bottlenecks. These factors shape whether a workload is suitable for straightforward relocation or whether migration would simply carry instability into a new environment. In some cases, the most valuable conclusion is that operational remediation should happen first.
A retail organization, for instance, may discover that its store replenishment application is technically easy to move but operationally fragile. The system depends on manual overnight batch restarts and has limited monitoring beyond server health checks. Migrating it as-is would shift the hosting model without improving reliability. The better decision may be to stabilize batch orchestration and observability first, then migrate once operational risk is under control.
A strong assessment should produce decision-ready outputs, not just descriptive reports. Typical outputs include:
- a heat map of migration complexity
- a shortlist of retirement candidates
- a set of applications requiring deep remediation
- a grouping of workloads suitable for early waves
- a list of “no-regret” actions such as clarifying ownership, removing obsolete interfaces, or standardizing runtime versions
These outputs feed directly into the target-state design and migration roadmap discussed in the next sections.
Current-state assessment is also where architecture can challenge assumptions. An application described as business critical may turn out to have low usage and no strategic future. A system believed to be difficult to move may become far simpler once hidden dependencies are removed. Conversely, an apparently simple rehost candidate may carry licensing, compliance, or latency constraints that make migration expensive. By bringing structure to these realities, enterprise architecture creates a credible foundation for both the target state and the migration sequence.
3. Target-State Enterprise Architecture and Cloud Operating Model
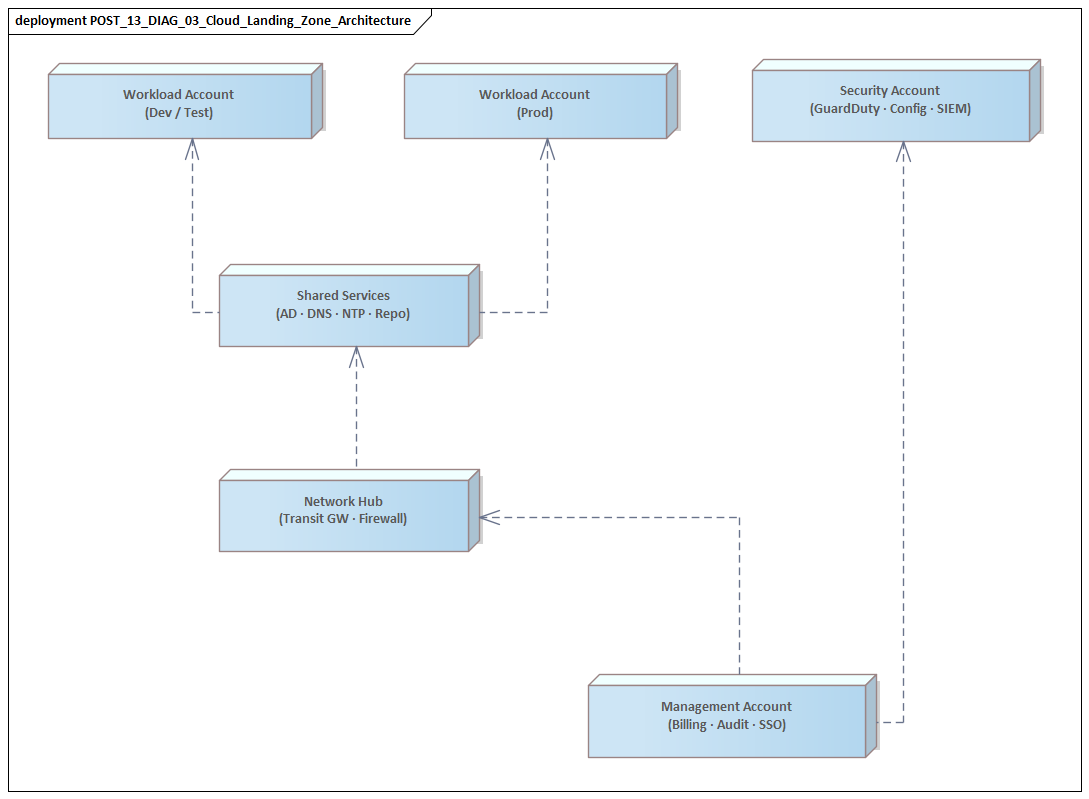
Once the current estate has been assessed and migration pathways identified, the next task is to define the target state clearly enough to guide execution without overconstraining delivery. That target state cannot be described only as a future hosting environment. It needs to show how business capabilities, platforms, data, security, integration, and operations will work together in the cloud.
A useful target-state architecture begins with a concise set of enterprise-wide design principles. Typical examples include identity as the primary control plane, automation by default, policy-driven security, API-first integration, managed services where appropriate, and observability built into platforms rather than added later. These principles become valuable when they are translated into standards, reference architectures, and reusable patterns that delivery teams can adopt without ambiguity.
The target state should also define the structural building blocks of the cloud environment. In most enterprises this includes:
- landing zones
- account or subscription structures
- network segmentation and connectivity patterns
- shared platform services
- data management patterns
- resilience designs across regions or availability zones
- logging, monitoring, and secrets management foundations
These are not minor technical choices. They shape long-term cost, control, and supportability. Weak account structures make cost allocation and access control difficult. Inconsistent network patterns introduce avoidable security and performance issues. Poorly designed shared services create duplication and support complexity. Enterprise architecture brings the cross-domain perspective needed to make these foundational decisions once, and make them well.
Just as important is the cloud operating model. Technical design alone does not create a workable cloud environment. The operating model must clarify who owns platform engineering, who approves exceptions, how security controls are implemented, how reliability is measured, and how responsibilities are divided between central teams and product-aligned delivery teams. In mature models, central teams provide reusable capabilities and guardrails, while application teams consume them through self-service mechanisms. That balance supports standardization without turning architecture into a delivery bottleneck.
Identity is often the clearest example. Many enterprises use migration to modernize fragmented IAM, replacing local directories and application-specific access models with federated identity, centralized role design, and automated joiner-mover-leaver processes. A target-state decision to make cloud IAM the default control plane can simplify access governance across hundreds of workloads, but only if it is designed before migration waves begin.
Another important design choice is the balance between enterprise platforms and local variation. Not every workload needs the same deployment model, but unconstrained choice quickly creates sprawl. Enterprise architecture should therefore define a limited set of approved runtime patterns, integration approaches, data service options, and security models. This does not remove flexibility; it channels flexibility into supportable paths. An architecture board might, for example, approve Kafka as the standard event backbone for domain events and asynchronous integration, while restricting point-to-point messaging products to approved legacy exceptions. The result is less duplication and a clearer integration direction across teams.
A bank modernizing customer channels might make a similar choice around runtime platforms. Rather than allowing each team to select its own container platform, serverless framework, or CI/CD tooling, the target state could define two supported paths: managed Kubernetes for stateful and integration-heavy services, and serverless for event-driven digital interactions. That is enough choice to accommodate different workload types without creating an estate that operations cannot support.
A strong target state also includes transition intent. Architects should identify which capabilities must be in place before large-scale migration begins—identity federation, network connectivity, centralized logging, secrets management, and cost management tooling, for example. This ties the target state directly to the roadmap. The target architecture is not just a future vision; it is the blueprint that determines what must be built first, what can vary later, and how migration can scale without losing control.
4. Migration Patterns, Roadmap, and Program Governance
Once the target state has been defined, the challenge shifts from design to controlled execution. This is often where cloud migration programs begin to lose coherence. Teams choose locally efficient approaches that conflict with enterprise standards, or leadership pushes for aggressive timelines without accounting for dependencies and control readiness. Enterprise architecture translates the target-state blueprint into a roadmap that is technically feasible, economically defensible, and governable at scale.
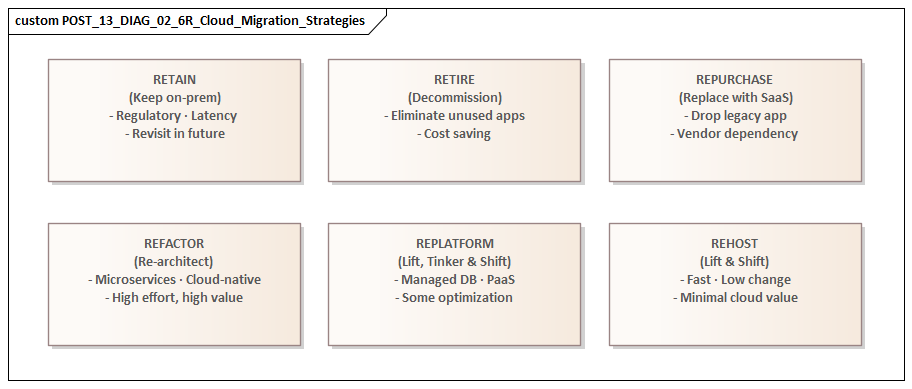
A practical starting point is to define migration patterns explicitly rather than letting each project invent its own. The familiar categories remain useful:
- rehost
- replatform
- refactor
- replace
- retire
- retain
These should be treated as decision patterns tied to business and operational intent, not as labels applied loosely after the fact. Rehosting may be appropriate when speed is the priority, such as during a data center exit, but it should usually be understood as a transitional state. Replatforming can improve manageability and resilience without requiring a full redesign. Refactoring is justified where cloud-native capabilities materially improve scalability, release velocity, or service reliability. SaaS replacement may be preferable for low-differentiation capabilities. Retirement should be treated as a first-class outcome, especially where portfolio analysis has already shown low value or duplication.
Consistency matters more than terminology. Architects should define entry criteria, design implications, control requirements, and expected benefits for each pattern. That supports better funding decisions and avoids familiar confusion—such as describing a major redesign as a rehost, or committing to a refactor without understanding the delivery effort involved.
The roadmap itself should be organized into migration waves, but those waves need to reflect both the findings of the current-state assessment and the prerequisites of the target operating model. Early waves should do more than move workloads. They should validate landing zones, deployment pipelines, support processes, observability, and cost baselines. For that reason, first-wave candidates should be important enough to test real conditions, but not so fragile or complex that they undermine program credibility. Later waves can then take on larger dependency clusters, regulated workloads, or systems requiring deeper modernization.
A sound roadmap also includes enabling work that is often missing from executive plans. Identity integration, network routing, data replication, service management alignment, tagging standards, backup validation, and operational readiness all affect migration pace. If these items are not planned explicitly, delivery teams end up solving them repeatedly during execution, which increases both delay and architectural drift. The roadmap should therefore combine workload moves with platform capability milestones and decision checkpoints.
Governance is what keeps the roadmap coherent when delivery pressure rises. In cloud migration, governance should be layered:
- Strategic governance aligns migration waves with business priorities, funding constraints, and risk appetite
- Architectural governance manages standards, approved patterns, and exception handling
- Delivery governance embeds controls into templates, reference implementations, and automated policy checks
This layered model reflects a central principle of successful migration programs: architecture must be operationalized, not left as a document set. In practice, it also means governance bodies need to make concrete decisions quickly—for example, approving a temporary dual-run pattern for a regulated payment system, or rejecting a proposed bespoke CI/CD stack because the standard platform already meets the need.
Roadmaps are strongest when they acknowledge that migration is not linear. A healthcare provider, for example, may plan to move patient scheduling early because the application appears technically straightforward. Governance review then identifies a hidden dependency on an on-premises imaging archive and a third-party support contract that prohibits database relocation. Rather than forcing the move, the program can resequence the wave, migrate surrounding services first, and use the delay to negotiate vendor support terms. That is architecture adding control without blocking progress.
A mature governance model also depends on measurable indicators. Migration volume alone says very little. Architects should track pattern mix, exception rates, unresolved technical debt, control compliance, post-migration incident trends, and cost variance against assumptions. These measures reveal whether the program is creating a sustainable cloud estate or merely relocating complexity.
In practice, migration patterns, roadmap design, and governance cannot be treated separately. The roadmap should express the target state, the migration patterns should reflect portfolio realities, and governance should keep execution aligned with both.
5. Security, Risk, Compliance, and Resilience by Design
Cloud migration succeeds only when control objectives evolve at the same pace as platform adoption. A common failure pattern is to treat security, risk, compliance, and resilience as downstream assurance activities, applied only after migration decisions have already been made. That approach creates delays, rework, and inconsistent control implementation. A better model is to build control into platforms, patterns, and operating processes from the beginning.
One of the most important architectural shifts in cloud is the move from perimeter-oriented control thinking to identity-centered, policy-based, continuously enforced models. Traditional assumptions about trusted internal networks are far less useful when services are distributed across accounts, regions, managed platforms, and automated pipelines. Enterprise architecture should therefore define security around identity federation, least-privilege access, workload isolation, secrets management, key management, and traceable administrative activity. These controls should be built into landing zones and deployment templates so that secure configuration becomes the default path rather than an optional enhancement.
Risk management also changes in cloud because the risk profile is dynamic. Misconfiguration, excessive permissions, unmanaged interfaces, and uncontrolled service adoption can introduce exposure quickly. Risk therefore cannot be assessed only at project approval points. Architects should help establish continuous control models in which configuration compliance, vulnerability posture, logging coverage, and policy conformance are monitored throughout the service lifecycle. This reinforces the broader governance model: control should be continuous, automated where possible, and tied to operational evidence.
Compliance requirements need the same architectural treatment. Obligations related to data residency, retention, privacy, encryption, segregation of duties, and auditability usually span multiple technology domains. During migration, these obligations are often weakened when teams focus only on infrastructure relocation and overlook how managed services, cross-border replication, or provider operating models affect compliance interpretation. Enterprise architects should define platform-level control mappings that show how enterprise obligations are implemented through cloud capabilities, operational processes, and evidence collection mechanisms. This reduces duplication across projects and gives control owners more confidence in the migration model.
Resilience deserves equal attention, because cloud availability is not automatic. Many migrated workloads remain vulnerable to the same weaknesses they had before migration: single points of failure, untested recovery procedures, tightly coupled dependencies, and unclear incident ownership. Architecture must therefore define resilience deliberately across application, platform, data, and operational layers. This includes failure-domain design, backup and restore patterns, recovery time and recovery point alignment, dependency failover behavior, and crisis communication paths.
The most effective way to scale these concerns is to express them as reusable control patterns rather than isolated review findings. Examples include:
- approved privileged access models
- standardized encryption and key rotation patterns
- reference designs for high availability
- policy-as-code for mandatory tagging and network restrictions
- predefined evidence trails for regulated workloads
As with migration patterns, consistency is what allows speed without sacrificing control. A simple example is IAM modernization: replacing shared administrator accounts with federated privileged access and short-lived elevated roles improves auditability and removes one of the most common inherited control weaknesses during migration.
Another example is resilience testing for regulated services. An insurer migrating its claims intake platform may discover that production backups exist but have never been restored under time-bound conditions. Rather than accepting backup configuration as sufficient evidence, the architecture team can require a tested restore pattern, documented recovery ownership, and monitoring of cross-region replication lag before production cutover. That is a far more meaningful control than a checklist confirmation that backups are enabled.
Security, risk, compliance, and resilience are not separate workstreams attached to migration. They are architectural qualities of the target state and operating model. When designed into the migration approach, they become enablers of scale rather than obstacles to delivery.
6. Value Realization, FinOps, and Continuous Architecture Evolution
A cloud migration program creates value only when migrated workloads deliver measurable business, financial, and operational improvement after the move. Migration completion is not the same as value realization. An enterprise can relocate a large portion of its estate and still fail to improve cost efficiency, delivery speed, resilience, or business responsiveness. Enterprise architecture helps close that gap by linking post-migration outcomes back to the business case, operating model, and control framework established earlier.
Value realization should be treated as a structured discipline, not as a retrospective benefits statement. At the start of each migration wave, architects should work with finance, product, and operations leaders to define expected outcomes at both workload and platform level. These may include reduced environment lead time, lower recovery effort, improved elasticity during demand spikes, retirement of duplicate tooling, or reduced manual support overhead. The key is to connect technical changes to observable indicators so the organization can test whether a migration pattern is actually producing the intended result.
FinOps becomes especially important at this stage because cloud economics are dynamic and highly sensitive to design choices. Cost is shaped not only by consumption volume, but also by storage patterns, resilience configurations, data transfer design, environment sprawl, licensing treatment, and the use of managed services. Enterprise architecture contributes by ensuring that financial accountability is built into the architecture itself. This includes:
- standard tagging models
- account or subscription structures aligned to business ownership
- service catalog controls
- cost visibility dashboards
- design standards that support unit economics analysis
These foundations become essential for proving whether the business case is being realized.
FinOps should not be separated from design governance. Cost optimization without architectural context can damage resilience, performance, or supportability. Architects should therefore define cost-aware reference patterns that balance service quality with financial impact. A highly available design may be justified for revenue-critical services but excessive for internal batch workloads. Likewise, refactoring to serverless or managed services may improve agility and reduce support effort, but only if workload behavior fits the pricing model. Architecture provides the context for making these trade-offs intelligently.
Another important point is that value realization often depends on post-migration change, not just migration execution. Once workloads are in the cloud, telemetry, incident data, and cost trends usually reveal opportunities that were not visible during planning. Some applications may need rightsizing, automation improvements, storage lifecycle policies, or redesigned integration flows. Others may show that a temporary rehost should now be followed by deeper modernization or replacement.
This is also where technology lifecycle governance becomes important. Cloud estates evolve quickly, and unmanaged service adoption can recreate the same fragmentation migration was meant to remove. An architecture review may, for example, set a retirement date for self-managed Kafka clusters once the managed enterprise streaming platform is proven, or phase out unsupported runtime versions within two release cycles. That kind of lifecycle discipline helps the target state remain coherent over time.
A consumer business may see this clearly after moving its e-commerce platform. Initial migration reduces infrastructure risk, but FinOps reporting later shows persistent overspend in non-production environments and high data transfer charges between the web tier and a legacy on-premises recommendation engine. The architecture response is not simply to cut spend. It may involve introducing automated environment shutdown policies, redesigning integration flows, and accelerating the move of the recommendation service to the cloud to eliminate avoidable transfer costs. Value realization, in other words, comes from architectural follow-through.
Cloud platforms, provider services, regulatory expectations, and internal delivery maturity all change quickly. Architects should therefore maintain a living set of standards, reference architectures, and approved patterns that can evolve without destabilizing the broader estate. Governance should encourage controlled learning: exceptions, pilot patterns, and optimization findings should be reviewed for wider architectural implications and, where appropriate, incorporated into enterprise standards.
Ultimately, enterprise architecture extends beyond enabling migration into governing the value produced after migration. By linking outcome measurement, FinOps discipline, and continuous adaptation, it helps ensure that cloud adoption remains economically transparent, operationally effective, and strategically aligned over time.
Conclusion
Enterprise architecture gives cloud migration programs something more valuable than technical consistency: enterprise-level decision quality under conditions of speed, uncertainty, and scale. The challenge is rarely just choosing a cloud service or moving a server. It is maintaining alignment across business priorities, platform evolution, regulatory obligations, delivery autonomy, and cost accountability while the estate is actively changing.
The strongest migration programs treat architecture as an operational capability rather than an upfront documentation exercise. Architects help define the business case, expose portfolio realities, shape the target operating model, standardize migration patterns, embed controls into platforms, and measure whether value is actually being realized. Their contribution is visible in clearer sequencing, fewer avoidable exceptions, faster onboarding to approved platforms, and stronger traceability from design choice to business outcome.
Cloud migration should leave the enterprise with more than a relocated application estate. It should produce a more coherent technology model, a more disciplined operating environment, and a stronger foundation for future transformation. Enterprise architecture is what makes that outcome intentional, so the organization does not reproduce old fragmentation in a new environment.
Frequently Asked Questions
What is architecture governance in enterprise architecture?
Architecture governance is the set of practices, processes, and standards that ensure architectural decisions are consistent, traceable, and aligned to strategy. It includes an Architecture Review Board, modeling standards, lifecycle management, compliance checking, and exception handling.
How does Sparx EA support architecture governance?
Sparx EA supports governance through package-level security, model validation rules, tagged value lifecycle tracking, baseline management, and report generation. Architecture decisions, compliance status, and review outcomes can all be tracked as model elements with defined owners and statuses.
What are the key elements of an effective EA governance checklist?
An effective EA governance checklist covers: principles alignment, standards compliance, integration impact assessment, security and data classification review, requirements traceability, roadmap alignment, and operational readiness. Each gate should produce model-based evidence, not just a presentation.