⏱ 26 min read
Using Sparx EA for Architecture Traceability in Transformation Programs
Learn how to use Sparx Enterprise Architect (EA) to improve architecture traceability across transformation programs, linking strategy, capabilities, requirements, applications, and delivery outcomes. how architecture review boards use Sparx EA
Sparx EA, Sparx Enterprise Architect, architecture traceability, transformation programs, enterprise architecture, traceability matrix, requirements traceability, capability mapping, application architecture, solution architecture, business architecture, digital transformation, architecture governance, change impact analysis, architecture repository EA governance checklist
Introduction
Transformation programs rarely fail because ambition is lacking. More often, they lose coherence between strategic intent and day-to-day delivery. Goals are agreed in one forum, operating model changes are defined in another, and delivery teams make implementation decisions under a different set of constraints. As the program progresses, the links between business motivation, architectural choices, solution scope, and delivered outcomes weaken. Traceability is what keeps those links intact.
In enterprise transformation, traceability is the ability to follow a line from strategy through capabilities, processes, requirements, applications, data, and technology, and then into initiatives, releases, and implemented change. That line matters because enterprise change rarely stays contained. A regulatory update can affect process design, data definitions, application behavior, integration patterns, and platform choices at the same time. A reprioritized capability can disrupt assumptions across several roadmaps. Without traceability, impact assessment slows down, becomes more subjective, and depends too heavily on individual recollection.
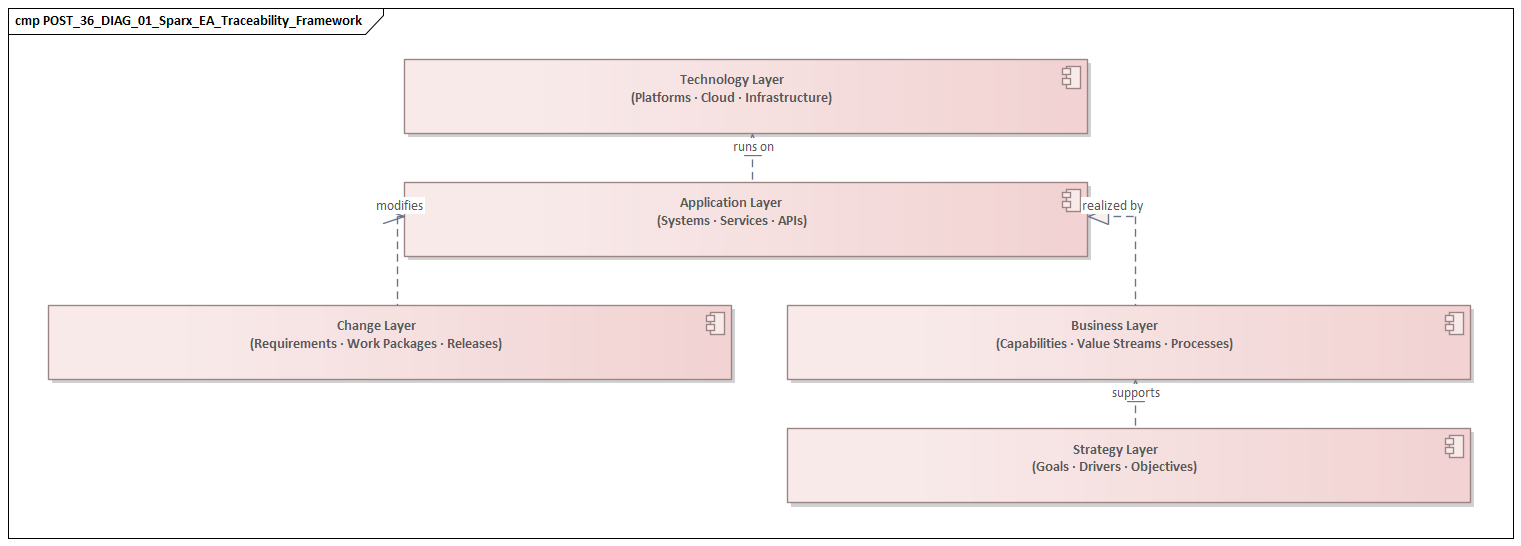
Sparx Enterprise Architect (EA) is well suited to this problem because it supports architecture as a connected repository rather than a loose collection of diagrams. The value is not simply that teams can create capability maps, process models, or application landscapes. The real advantage comes from linking those views into a coherent model. A capability can be tied to strategic objectives, realized by processes, enabled by applications, dependent on data, constrained by technology, and changed through initiatives or releases. When those relationships are explicit, architects, program leaders, and governance forums are working from the same model rather than from parallel interpretations.
This becomes practical very quickly. Governance forums repeatedly ask the same kinds of questions. Which applications support the capabilities being modernized? Which projects are changing the same process or data domain? Which requirements still have no solution component attached? Which legacy technologies remain because critical services still depend on them? These are not modeling niceties. They influence sequencing, funding, risk, and stakeholder alignment. If an architecture board is deciding whether to extend a legacy CRM for another year, it needs to see more than the application itself. It needs visibility of the capabilities, integrations, data dependencies, and planned releases still tied to it.
To make EA useful in that role, an organization needs more than well-drawn diagrams. It needs a deliberate meta-model, clear relationship semantics, and a traceability path that reflects how strategy is translated into delivery. It also needs working disciplines so that multiple teams can contribute without fragmenting the model. Used in that way, Sparx EA becomes a traceability platform: a place where business intent, architectural structure, and change execution can be connected, examined, and governed over time. Sparx EA training
The sections that follow set out how to do that in practice: why traceability matters, how to position EA effectively, how to define a workable meta-model, how to establish end-to-end traceability, and how to use the repository for governance, scaling, and adoption.
Why Traceability Matters in Enterprise Transformation Programs
Transformation programs operate at a scale where informal alignment breaks down quickly. A single initiative may affect customer journeys, controls, processes, data ownership, integrations, and platform roadmaps at the same time. In that setting, traceability is not a documentation preference. It is what keeps architecture usable as complexity increases.
The first reason is volatility. Transformation programs rarely move in a straight line. Funding changes, leadership priorities shift, mergers intervene, and regulatory demands arrive midstream. When architecture artifacts are only loosely connected, every change triggers a rediscovery exercise. Teams have to reconstruct why a requirement exists, what capability it supports, which solutions depend on it, and whether planned work still aligns with the original intent. A traceable repository preserves that chain of reasoning and makes replanning faster.
The second reason is impact analysis. Architects are regularly asked time-sensitive questions: what happens if a platform migration slips by two quarters, which business areas are affected by a data model change, where duplicate investment is emerging across portfolios. Without traceability, the answers come from interviews, spreadsheets, and whoever remembers the history. With traceability, the repository becomes the basis for structured analysis. It can show direct dependencies and second-order effects such as downstream reporting impacts, shared services disrupted by interface changes, or several initiatives converging on the same capability.
A third reason is alignment between planning and delivery. Many programs produce persuasive target-state architectures but struggle to connect them to executable change. Capabilities are prioritized, principles are approved, transition states are defined, yet delivery backlogs evolve on a separate track. The pattern is familiar: architecture looks complete in governance forums but has limited influence on implementation decisions. Traceability helps close that gap by linking strategic drivers and target-state decisions to requirements, work packages, and releases. It allows architects to test whether delivery is genuinely moving the enterprise toward the intended target state. In an IAM modernization, for example, traceability can show whether the objective of stronger access governance is reflected in process redesign, identity platform changes, and onboarding releases, rather than sitting only in policy documents.
Traceability also sharpens accountability. In large organizations, decisions are distributed across portfolio boards, architecture review forums, product teams, and operational leaders. A connected model makes those decisions easier to inspect. It becomes possible to show which requirement led to a design choice, which standard justified a technology selection, or which exception allowed a departure from a reference architecture. In regulated environments, that matters even more because stakeholders may need evidence that an obligation has been translated into process, application, and data changes rather than merely acknowledged.
Continuity is another practical benefit. Transformation programs often run for years, while people, vendors, and organizational structures change several times. If architectural knowledge lives mainly in slide decks or in the heads of a few individuals, continuity erodes quickly. A traceable repository preserves institutional understanding in a form others can inspect, challenge, and extend.
A retail bank, for instance, may launch a customer onboarding simplification program while a separate compliance initiative updates KYC controls. Without traceability, both teams can change the same onboarding process and customer data objects in parallel without realizing where their scope overlaps. By the time the collision becomes visible, delivery dates and budgets are already committed.
The core point is simple: traceability preserves a visible line from intent to execution. The next question is how to position Sparx EA so it can support that line effectively. Sparx EA best practices
Positioning Sparx EA as a Traceability Platform
In a transformation program, Sparx EA should be positioned not primarily as a diagramming tool, but as a structured architecture knowledge base. The distinction is important. Many organizations use EA to create diagrams and still fail to use it as a repository. They produce capability maps, process views, and application landscapes, but the artifacts remain only loosely connected. The documentation looks rich; the analytical value remains limited.
For traceability to work, EA must be treated as a platform for relationships. The repository should be designed around how stakeholders need to navigate change: from strategic objective to capability, from capability to process, from process to application and data, and from those elements to initiatives, releases, and migration activities. In other words, the repository should reflect the logic of the transformation, not merely store architecture content by domain.
That requires a deliberate meta-model rather than an accumulation of diagrams. Teams need agreement on which element types represent the core objects of the transformation and which relationship types carry meaning. If a capability is associated with a strategic outcome, realized by a process, enabled by an application service, and changed by a work package, those links need to be modeled consistently. Once they are, EA can support impact analysis, roadmap validation, and governance reporting without manual reconstruction each time a question is raised.
EA should also act as a federating layer across architecture domains. Business architecture, solution architecture, data architecture, and portfolio planning often mature at different rates and use different structures. The repository does not need every domain to model everything exhaustively. It needs each domain to contribute the elements and relationships that matter for enterprise-level decisions. That is usually the difference between a repository that is theoretically complete but operationally ignored, and one that becomes part of routine governance.
Scope matters as well. EA is not a replacement for agile delivery tooling, CMDB platforms, or portfolio systems of record. Its role is to provide the architectural line of sight across them. Delivery tools manage backlog items and execution detail. CMDBs manage operational configuration. Portfolio systems manage funding and planning records. EA should sit above those systems as the place where transformation logic is made explicit: why a change exists, what enterprise structures it affects, how it relates to other changes, and whether the overall program remains aligned to target intent.
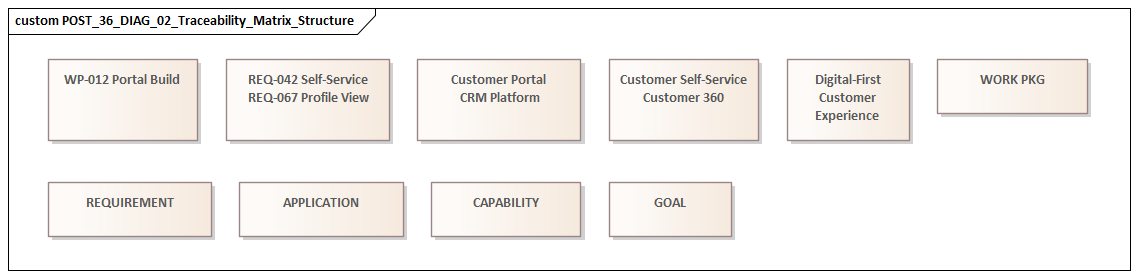
This positioning also allows multiple views to be generated from the same underlying model. Executives may need a capability-to-investment view. Domain architects may need process-to-application mappings. Delivery teams may need requirement-to-solution traceability. If the repository is structured properly, these are not separate documentation exercises. They are different views of the same connected architecture. An architecture board reviewing a proposal to adopt Kafka as an event backbone, for example, should be able to see which business events, producer systems, consumer services, and legacy integrations would be affected before approving the pattern.
A healthcare provider offers another good illustration. If it is consolidating patient administration systems across several hospitals, the repository should not only show the target application landscape. It should also show which admission processes are changing, which patient data entities are being standardized, which regulatory controls are affected, and which releases will retire which local systems. That is the level at which EA becomes operationally useful.
Once EA is positioned in this way, the next requirement is clear: define the meta-model and traceability framework that make those connections consistent and usable.
Defining the Meta-Model and Traceability Framework
Effective traceability starts with a disciplined meta-model. Without one, repositories become collections of locally useful artifacts that cannot be connected reliably across a transformation program. The goal is not to model everything in the enterprise. It is to define a manageable set of concepts and relationships that support the decisions the program actually needs to make.
A practical starting point is to identify the core object classes that must be traceable end to end. In most transformation programs these include:
- strategic drivers or objectives
- business capabilities
- value streams or business processes
- requirements
- application components or services
- data entities
- technology platforms
- change constructs such as initiatives, work packages, increments, and releases
Some organizations will also include principles, policies, risks, controls, organizational units, or customer journeys where those are central to governance. The important point is that these are not just labels on diagrams. They are the stable nouns of the repository.
The next step is to define relationship semantics. This is where many repositories become ambiguous. If teams use generic associations for everything, traceability may look possible but remains analytically weak. A smaller set of meaningful relationships is far more useful: drives, realizes, enables, uses, depends on, constrains, changes, and serves. For example:
- a strategic objective drives a capability uplift
- a capability is realized by a process
- a process is enabled by an application service
- an application uses a data entity
- a technology platform hosts or supports an application
- an initiative changes one or more of these elements
These semantics matter because they make impact analysis credible. If relationships are vague, the results will be vague too.
The meta-model should be shaped by use cases rather than theoretical completeness. Architects should ask which governance questions the repository must answer. If the program needs to identify which projects affect the same customer data domain, then data entities, applications, and initiatives must be linked explicitly. If governance depends on proving that regulatory obligations are reflected in solution scope, then obligations, requirements, controls, and solution elements need a defined trace path. If technology lifecycle governance is a concern, the model should also show which applications and services still depend on a platform marked end-of-life.
Granularity requires the same discipline. If one team models applications at enterprise-system level while another models every interface and deployment node, traceability becomes uneven and hard to interpret. The repository should define the level at which each domain is expected to model for enterprise purposes. Detailed design can still exist, but not every level of detail needs to participate in enterprise traceability. In practice, organizations benefit from a minimum viable architecture standard for each element type: enough detail to support ownership, lifecycle, dependency analysis, and planned change.
In Sparx EA, this framework is usually implemented through stereotypes, tagged values, package structures, naming conventions, and relationship constraints. Tagged values can hold attributes such as lifecycle state, criticality, regulatory relevance, target disposition, and owning domain. Relationship matrices and validation rules can then be used to check consistency.
One distinction is especially important: structural architecture versus change architecture. Structural elements describe the enterprise as it exists or is intended to exist. Change elements describe how that structure is being modified through programs and releases. Keeping those concerns separate, while still related, prevents confusion between what the enterprise is and what a project is doing to it. This becomes essential when multiple initiatives affect the same capability or application over time.
A realistic example helps here. In an insurance claims transformation, “Claims Assessment” is a structural business capability, “Claims Workflow” is a structural process, and “Claims Platform Replacement Wave 2” is a change object. If those are blurred together, stakeholders cannot tell whether they are looking at the enterprise design, the target operating model, or the current project scope.
With that framework in place, the repository can support the end-to-end trace path from strategy to delivery.
Establishing End-to-End Traceability from Strategy to Delivery
End-to-end traceability only becomes valuable when it is modeled as a navigable chain of decisions rather than a set of disconnected links created for compliance. The aim is to move through the repository in either direction: downward from strategy into implementation scope, and upward from a delivery item back to the business intent that justifies it.
A common traceability route in transformation programs looks like this:
strategic objective -> business capability -> value stream or process -> requirement -> application or service component -> initiative / work package / release
Data entities, controls, and technology platforms sit alongside this path where they materially affect design or sequencing. Not every organization will use exactly this chain, but every organization needs an explicit one. If architects do not define the intended route, teams will create local interpretations and traceability will fragment.
A useful discipline is to model the decision handoffs between layers. Strategy does not directly produce software components. It is translated through intermediate architectural choices. A strategic objective leads to a capability investment priority. That priority shapes process redesign and information requirements. Those requirements then inform solution building blocks and delivery scope. Capturing these handoffs helps explain why a solution exists in its current form and makes it easier to see where interpretation has drifted between planning levels.
This becomes particularly important when delivery structures do not align neatly with architecture structures. Programs are often funded by initiative, product, or regulatory deadline, while architecture is organized around capabilities, domains, and platforms. EA can bridge that mismatch by allowing the same architecture element to be linked to multiple delivery constructs. A capability may be changed by several projects across different increments. A single release may implement requirements tied to multiple strategic themes. Traceability therefore needs to support many-to-many relationships rather than assume a simple top-down hierarchy.
Another important distinction is between direct realization and indirect contribution. Not every work package fully realizes a requirement or target capability. Some create enabling conditions by improving data quality, retiring technical debt, or laying integration foundations. Making that difference explicit leads to better roadmap interpretation. It prevents stakeholders from assuming that every linked delivery item produces immediate business outcomes and helps architects explain foundational investments that are necessary even when they are not visibly transformational on their own. A Kafka implementation is a good example: the first release may not transform a customer journey directly, but it can establish event topics, producer standards, and consumer integration patterns that later releases depend on.
Time matters as well. End-to-end traceability should show not only what is connected, but when the connection becomes true. A target application may support a target process, but only after a later release. A capability gap may be partially addressed in one transition state and fully resolved in another. Modeling these temporal aspects allows traceability to support transition architecture rather than static target-state documentation alone.
A public-sector example makes this concrete. Suppose a benefits agency has a strategic objective to reduce claim processing time. That objective drives improvement in the “Case Management” capability. The capability is realized through an eligibility assessment process. The process generates requirements for digital document intake, automated rules evaluation, and case status visibility. Those requirements are implemented across a workflow platform release, a document management upgrade, and a later analytics release. Without explicit traceability, it is difficult to tell whether the released scope is actually contributing to the strategic objective or simply modernizing technology in isolation.
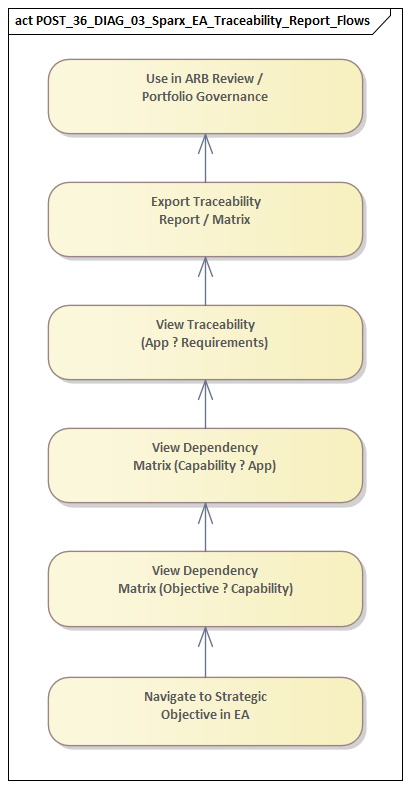
In practice, architects should test the trace path against real governance questions:
- Which strategic objectives are receiving investment, and through which initiatives?
- Which capabilities are being changed in the next increment?
- Which requirements remain unrealized?
- Which releases affect a critical data object or control?
- Which platform retirements are blocked by unresolved business dependencies?
If those questions can be answered quickly and consistently, end-to-end traceability is working. Once it is working, the repository can play a more active role in governance, dependency management, and impact analysis.
Using Sparx EA for Governance, Dependency Management, and Impact Analysis
Once traceability is established, the next challenge is to use it operationally. The repository should not remain a passive model structure. It should support governance decisions about consequence, timing, sequencing, and control.
A practical approach is to treat each significant change as an architectural event with explicit relationships to the enterprise elements it affects. Initiatives, epics, work packages, transition increments, and releases can all be modeled as change objects linked to capabilities, processes, applications, data entities, and technologies. This makes it possible to see where multiple changes converge on the same part of the landscape.
Convergence is not automatically a problem, but it is often where delivery risk, design inconsistency, and sequencing conflicts first surface. If two programs are changing the same customer data domain, redesigning the same operational process, or introducing overlapping capabilities, EA should make that visible early enough for governance intervention.
Dependency analysis should also extend beyond narrow technical dependencies. In enterprise transformation, critical dependencies often involve policy approval, data ownership, organizational readiness, contract timing, or external obligations. Traceability is most useful when it reflects how the enterprise actually changes, not just how solutions are built. The repository should therefore allow change objects to connect not only to solution components, but also to controls, standards, organizational elements, and external constraints.
Impact analysis works best when it is assessed across several dimensions at once:
- Structural impact – which architecture elements are directly or indirectly affected
- Operational impact – which services, users, or controls may experience disruption or changed responsibilities
- Roadmap impact – which other planned changes become blocked, accelerated, duplicated, or invalidated
A repository that shows only direct technical dependencies will miss many of the real consequences, which usually emerge at the intersection of business timing, delivery coordination, and architectural integrity.
This is where EA’s relationship views, matrices, and filtered queries become genuinely useful. Rather than relying on static diagrams, architects can produce targeted views such as:
- applications impacted by a specific release
- initiatives affecting a regulated data set
- capabilities dependent on a legacy platform marked for retirement
- projects converging on the same process area
- requirements linked to no current delivery scope
These views work well in governance forums because they shift discussion from opinion to evidence. Instead of debating abstractly whether a deferral is low risk, stakeholders can inspect what the deferral touches and which downstream commitments it puts at risk. For example, a technology governance forum reviewing an end-of-support database can see exactly which applications, interfaces, and releases would be affected by extending or retiring it.
EA is also useful for exception management. Transformation programs inevitably generate waivers, interim states, and tactical compromises. If waivers, architecture decisions, and transition constraints are linked directly to the affected elements and initiatives, the repository creates a visible record of where temporary complexity is being introduced, why it was accepted, and what future change is needed to remove it. Without that trace, exceptions have a habit of becoming permanent architecture.
Consider a manufacturer retiring an on-premise integration broker in favor of an API platform. One plant may receive a temporary waiver because a production scheduling interface cannot move before a contractual system upgrade. If that waiver is captured only in meeting minutes, it will be forgotten. If it is linked in EA to the application, interface, plant operations process, and target release, governance can see both the reason for the exception and the dependency that must be resolved.
Used in this way, EA does not replace governance judgment. It improves it by making dependencies and consequences visible. The next challenge is sustaining this approach across multiple teams and portfolios without losing consistency.
Scaling Traceability Across Teams, Portfolios, and Program Increments
The challenge with traceability is rarely proving its value. The harder part is sustaining it as the transformation grows. What starts as a coherent approach in one program can fragment quickly when multiple teams and portfolios begin contributing at different speeds and with different levels of maturity. free Sparx EA maturity assessment
The first scaling challenge is distributed authorship. Business architects may maintain capabilities and operating model changes, solution architects may model application impacts, data architects may curate information objects, and PMO or portfolio functions may own initiative and milestone data. If these contributors work independently, traceability degrades into partial chains with inconsistent semantics. A scalable operating model therefore needs clear ownership boundaries for element types, relationship types, and mandatory attributes. Someone must be accountable for the creation, update, approval, and retirement of each class of repository object.
The second challenge is balancing standardization with flexibility. Teams need enough freedom to model what matters in their domain, but not so much that every portfolio invents its own traceability pattern. A practical approach is to define an enterprise-level traceability spine that all programs must use, while allowing domain-specific extensions where necessary. For example, every portfolio may be required to connect initiatives to capabilities, impacted applications, and target releases, while only certain domains add specialist concepts such as control objectives or canonical data entities.
Traceability remains useful only when it is embedded in real decision flow. Repository updates should happen at the same points where architecture and delivery naturally intersect: intake, solution outline, design review, increment planning, and release governance. If updates are treated as separate documentation tasks completed after decisions are made, they will lag behind reality. If a project cannot pass architecture review without linking its scope to impacted capabilities, applications, and milestones, traceability becomes part of governance rather than an optional follow-up activity.
Program increments create another challenge of granularity. EA should represent enduring structure and planned change intent, not every movement in the backlog. In most organizations, the right level is feature group, work package, or release-train objective rather than individual user story. That preserves meaningful traceability to enterprise impact without turning the repository into something too volatile to manage.
Cross-portfolio coordination also depends on shared reference views. As multiple investment streams evolve, architects need a way to compare where change is concentrating, where dependencies cross funding lines, and where target-state assumptions diverge. Common dashboards, matrices, and heatmaps generated from EA can support this, but only if the underlying metadata is disciplined. Lifecycle status, target disposition, increment, owning portfolio, and criticality are especially important because they allow the same model to be sliced for different governance audiences.
At scale, quality assurance becomes a capability in its own right. Repository health checks, trace completeness rules, duplicate detection, and periodic model reviews are necessary to prevent slow degradation. This is not administrative overhead. It is what preserves confidence that traceability outputs can be trusted in governance decisions.
Common Pitfalls and Practical Success Factors
Even when the case for traceability is accepted, organizations often struggle to make it stick. The issue is rarely the tool alone. More often, the repository is expected to compensate for unclear ownership, inconsistent governance, fragmented terminology, or unrealistic modeling expectations.
One common pitfall is trying to model too much too early. Programs often begin with ambitions for comprehensive enterprise coverage, but that can produce a repository that is complex, slow to maintain, and difficult to trust. Teams create too many element types, too many custom relationships, and too much metadata before there is a clear operational need. A better approach is to start with a small number of traceability scenarios tied to immediate governance needs, then expand only where value is proven.
Another pitfall is confusing completeness with usefulness. It is entirely possible to have a large volume of architecture content in EA and still be unable to answer basic transformation questions. This usually happens when teams focus on producing diagrams rather than maintaining relationship quality. A smaller repository with disciplined links is far more valuable than an extensive model with inconsistent semantics.
Weak business engagement is another recurring problem. Traceability fails when it is treated as an architecture-only concern. If business stakeholders do not recognize the capabilities, processes, outcomes, or initiative structures in the repository, the model may be technically coherent but organizationally disconnected. The concepts used in the repository must be understandable to portfolio leads, product owners, and business change teams. If the repository is not referenced in planning and governance meetings, it will not stay current for long.
Tool complexity can also undermine adoption. Over-customization, inconsistent naming, and uncontrolled package structures make EA harder to navigate, especially for occasional users. In large programs, the real test is not whether expert modelers can work around that complexity, but whether non-specialist stakeholders can interpret outputs confidently. Clear conventions, standard viewpoints, and reusable templates usually contribute more to long-term success than advanced features used by only a few architects.
A further challenge is change fatigue. As programs accelerate, teams naturally prioritize delivery outputs over repository discipline. If updating EA is seen as extra administration with no immediate payoff, model quality decays quickly. The practical response is to embed traceability into approval and planning mechanisms. Architecture review entry criteria, transition-state approvals, and release readiness checks can all require specific trace links to be present and validated.
Several success factors consistently help:
- Define a minimum mandatory trace set for every change initiative.
- Assign explicit stewardship for key element classes and relationship integrity.
- Use regular quality reviews to detect missing links, duplicates, and stale content.
- Produce stakeholder-specific views that demonstrate value quickly.
- Keep the meta-model small enough to remain understandable.
- Treat adoption as a change management effort, not just a tooling rollout.
A final success factor is to measure usefulness, not just repository volume. If the architecture team reports only counts of diagrams or elements, stakeholders will assume the exercise is administrative. If it reports reduced impact-assessment time, clearer dependency decisions, or fewer conflicting changes across portfolios, the value becomes tangible.
These practices reinforce the themes developed in the earlier sections: a clear repository role, a disciplined meta-model, an explicit end-to-end trace path, and governance processes that depend on the model. When those elements support one another, traceability becomes sustainable.
Conclusion
Sparx EA gives transformation programs something many organizations struggle to maintain: architectural memory that remains usable under pressure. Its value lies not simply in the ability to model relationships, but in making those relationships part of how the enterprise makes decisions.
Effective traceability depends on several things working together: a clear understanding of why traceability matters, a repository positioned as a connected knowledge base rather than a diagram store, a disciplined meta-model with meaningful relationship semantics, and an end-to-end trace path that links strategy to delivery. When those foundations are in place, EA can support governance, dependency management, impact analysis, and cross-portfolio coordination in ways that static documentation cannot.
The practical test is not whether every artifact is connected. It is whether the repository helps the organization act with greater confidence. Can leaders see which investments support which objectives? Can architects assess the consequences of a deferral or exception quickly? Can delivery teams understand how their scope contributes to target-state intent? If the answer is yes, traceability is functioning as an operational capability.
The longer a transformation runs, the more important this becomes. Strategies evolve, teams change, and delivery structures are reorganized. A traceable repository preserves the logic of change through that turbulence. For enterprise architects, that is the real contribution of Sparx EA in transformation programs: not better diagrams, but a stronger line of sight between intent, design, investment, and delivery reality. Sparx EA guide
Frequently Asked Questions
What is architecture traceability?
Architecture traceability is the ability to navigate from a business goal or requirement down through capabilities, applications, and technology components — and back up again. It makes architectural decisions auditable, enables impact analysis, and demonstrates that technology investment is aligned to business outcomes.
How do you implement traceability in Sparx EA?
In Sparx EA, traceability is built using Realisation and Dependency relationships between elements. A requirement element realises a business goal; an application component realises an application service; a technology node hosts the application. Traceability matrices can be generated as reports and impact analyses run through the relationship graph.
Why does traceability matter in transformation programs?
Transformation programs are long, involve many teams, and create many interdependencies. Traceability ensures that every design decision can be traced to a business requirement, that change impacts can be assessed before commitment, and that governance evidence is available for architecture reviews and regulatory audits.