⏱ 21 min read
Architecture Modeling for Platform Transformation: Strategy, Frameworks, and Best Practices Sparx EA best practices
Learn how architecture modeling supports platform transformation by aligning business goals, technology strategy, target-state design, and implementation roadmaps for modern enterprises.
architecture modeling, platform transformation, enterprise architecture, target state architecture, transformation roadmap, business capability modeling, solution architecture, technology modernization, operating model transformation, architecture frameworks, digital transformation, platform strategy how architecture review boards use Sparx EA
Introduction
Platform transformation is not a one-off upgrade. It changes how an enterprise assembles, governs, operates, and improves its digital estate. Rather than optimizing a single application or running an isolated program, the organization is reshaping a shared foundation: common services, data capabilities, identity and access controls, integration patterns, developer tooling, observability, and policy enforcement. That is why architecture modeling matters. Sparx EA training
In this context, modeling is more than documentation. It is a decision tool. It helps executives link investment to business outcomes, gives platform and product leaders a clearer view of capability gaps and ownership boundaries, and gives engineering teams a practical understanding of service interactions, data responsibilities, deployment constraints, and non-functional requirements. Effective models do not force every stakeholder into the same level of detail. They connect viewpoints and keep the transformation aligned.
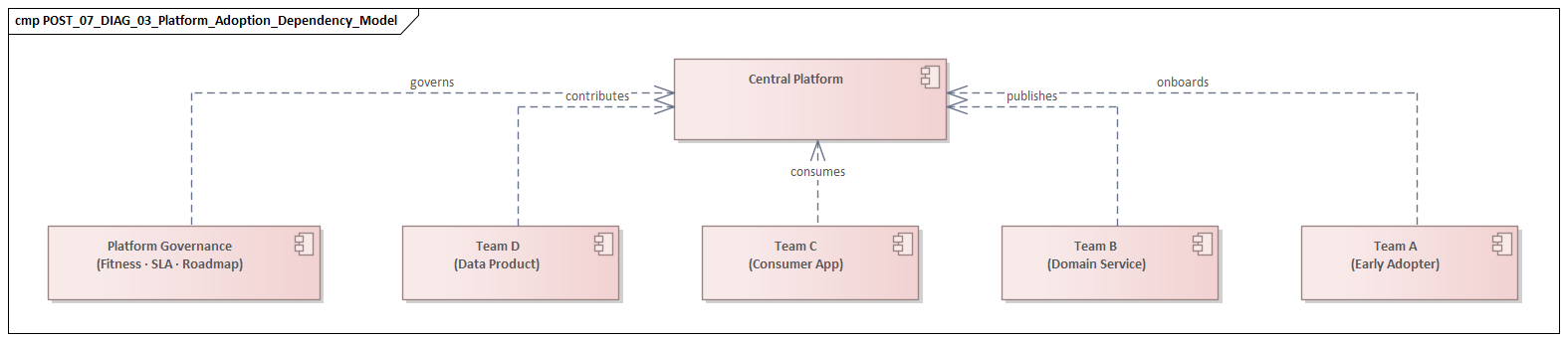
Platform transformation creates a distinctive architectural challenge because the platform itself must be modeled alongside the business domains that depend on it. When that relationship is left vague, familiar problems follow: central services become too broad, local teams rebuild the same capabilities, or governance slows adoption instead of enabling it. Modeling brings those trade-offs into view early. It shows where standardization improves security, resilience, and efficiency; where domain variation is justified; and where temporary coexistence with legacy systems is simply unavoidable.
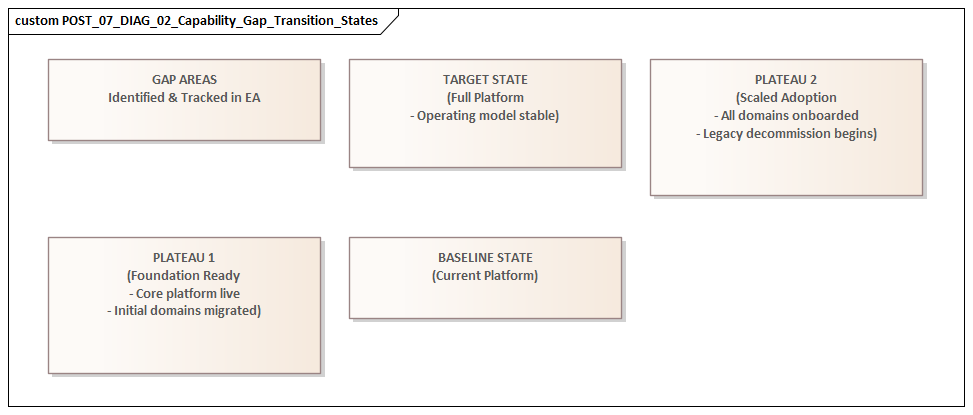
This is also why architecture modeling needs both layers and time. Static target-state diagrams have value, but they do not show how change will happen. Architects also need models that capture transition states, migration dependencies, stable interfaces during change, sensitive data flows, and the sequencing choices that determine whether value appears early or is delayed. In practice, transition architectures, capability heatmaps, and roadmaps often prove more useful than polished end-state diagrams because they support governance and delivery decisions in real time.
At its core, architecture modeling in platform transformation serves a simple purpose: it makes the platform understandable. Stakeholders need to see what the platform provides, who depends on it, how it is governed, where it can change safely, and where change introduces enterprise risk. When models are treated as living decision assets rather than passive documents, they help align strategy and execution, reduce transformation risk, and support the creation of a platform that is robust, governable, and usable.
1. Defining Architecture Modeling for Platform Transformation
Architecture modeling for platform transformation is the structured representation of how business capabilities, technology assets, operating controls, and delivery responsibilities come together in a platform-based operating model. It sits between high-level strategy and detailed solution design. Its purpose is not only to describe technical components, but to support decisions about how the platform will enable business change, how teams will consume it, and how it will evolve.
A complete model spans three dimensions. First, it shows business enablement: which business capabilities depend on the platform, what outcomes the platform is meant to improve, and where standardization creates measurable value. Second, it shows structural architecture: domains, services, data products, integration mechanisms, infrastructure patterns, and control points. Third, it shows operating model implications: ownership boundaries, support responsibilities, lifecycle management, service expectations, and governance paths. When one of these dimensions is missing, the model becomes either technically rich but organizationally disconnected, or strategically attractive but operationally weak.
Platform transformation also changes what architects need to model because platforms are consumed, not merely deployed. The emphasis shifts from isolated systems to relationships: producer and consumer interactions, APIs, onboarding paths, policy inheritance, dependency chains, and the experience of internal users such as product teams, developers, operators, and control functions. A platform can be technically sound and still fail to create value if it is difficult to adopt. For that reason, architecture modeling has to include adoption, compliance, and extensibility, not just internal structure.
One useful distinction is between modeling the platform as a product and the platform as shared infrastructure. The product view focuses on service offerings, tenant boundaries, service levels, release expectations, and feedback loops. The infrastructure view focuses on runtime environments, tools, network patterns, and technical controls. Both matter, but the product view is often the better corrective because it makes consumption and accountability visible. It forces a practical question: is the platform delivering reusable capabilities in a form that teams can depend on?
Good models also make constraints explicit. Regulatory obligations, resilience targets, data residency rules, legacy dependencies, vendor commitments, and skills availability often shape the transformation more than the ideal target architecture does. If those constraints remain hidden, the target state looks cleaner than reality and the roadmap becomes brittle. A common example is IAM modernization: the target may assume centralized identity, single sign-on, and role-based access, while the transition model has to account for legacy directories, application-specific entitlements, and phased federation.
A retail bank, for instance, may define a target identity model in which all workforce access flows through a central identity provider with MFA and role-based access. In practice, the payments platform may still depend on a legacy LDAP directory and locally managed privileged accounts. Unless the transition architecture captures that dependency, the roadmap will overstate what can be decommissioned in the first wave.
Architecture modeling also has to support decisions across multiple horizons. At the strategic horizon, it helps determine what should be centralized, federated, or left within domains. At the delivery horizon, it guides implementation patterns, integration standards, and migration sequencing. At the operational horizon, it clarifies observability responsibilities, incident boundaries, and control enforcement. That multi-horizon view is what makes architecture modeling a practical decision framework rather than a static description.
2. Business Drivers and Strategic Objectives
Architecture modeling matters only when it connects platform design to enterprise outcomes. Platform transformation is rarely funded for modernization alone. More often, it is driven by a mix of delivery pressure, operational inefficiency, and strategic need.
One common driver is speed with consistency. Delivery teams often solve the same foundational problems repeatedly: identity integration, environment provisioning, logging, API mediation, security controls, deployment pipelines, and data access patterns. That may create local progress, but across the enterprise it adds friction. A platform transformation addresses that friction by providing shared capabilities that reduce repeated effort while preserving the right guardrails. The goal is not centralization for its own sake. It is faster, more reliable delivery across domains.
A second driver is cost and complexity reduction. Over time, fragmented tooling, duplicated services, inconsistent hosting models, and unmanaged legacy dependencies increase both direct cost and operational overhead. Platform transformation seeks to simplify the estate through rationalized services, clearer lifecycle paths, and less unnecessary variation. Cost reduction is best understood as the result of simplification and reuse, not the sole reason for the transformation.
A third driver is risk reduction at scale. As digital dependency grows, weaknesses in security, resilience, recovery, and data governance stop being local issues and become systemic ones. A platform approach allows the enterprise to build controls into shared foundations instead of relying on every team to implement them independently. Standardized identity, policy enforcement, auditability, backup patterns, and observability can be designed once and inherited many times.
A fourth driver is business adaptability. Enterprises dealing with market shifts, regulatory change, mergers, new channels, or product diversification need a foundation that supports change without constant reinvention. In that setting, the platform becomes a reusable base for new products, partner integrations, and data-driven services. The strategic objective is flexibility built on reusable building blocks rather than bespoke project delivery.
These drivers should be translated into design implications. If delivery speed is the priority, the model should show self-service capabilities, standardized deployment paths, and reduced dependency friction. If risk reduction is the priority, it should show where controls are enforced, how exceptions are handled, and which controls are inherited by consuming teams. If cost efficiency is the goal, it should show where consolidation is realistic and where domain-specific diversity still makes sense.
The strongest platform strategies are stated in measurable terms. That might mean reducing environment provisioning time, lowering integration lead time, increasing reuse of shared services, improving recovery performance, or reducing unsupported technology patterns. Measures like these make the architecture accountable to outcomes and give later roadmap decisions a firmer basis. fixing Sparx EA performance problems
Consider a manufacturer that takes six weeks to provision a compliant integration environment for a new supplier-facing service. If the platform strategy includes a self-service environment template with built-in logging, network policy, and secrets management, the architecture model should make that path visible and measurable. Otherwise, “faster delivery” remains a slogan rather than a design commitment.
3. Core Architecture Domains and Modeling Perspectives
The three dimensions defined earlier—business enablement, structural architecture, and operating model—need to be grounded in a manageable set of architecture domains. Without that, the transformation either dissolves into infrastructure detail or drifts into abstract capability language.
3.1 Business Capability Domain
This domain shows which enterprise capabilities are enabled, constrained, or reshaped by the platform. It clarifies where platform investment changes how value is delivered. Customer onboarding, partner integration, or regulatory reporting, for example, may depend on different combinations of platform services. This view helps separate enterprise-wide needs from domain-specific variation.
3.2 Application and Service Domain
This domain defines service boundaries, interaction patterns, orchestration points, and the distribution of responsibilities between platform teams and consuming product teams. It is especially important because unclear service boundaries usually produce one of two outcomes: a platform that is hard to define or one that becomes overly controlling. The model should show which capabilities are reusable platform services, which remain within business applications, and where explicit contracts are needed.
A healthcare provider offers a useful illustration. The platform team may own API gateway services, audit logging, and identity federation, while the patient scheduling domain retains responsibility for appointment rules and booking workflows. If the platform starts to absorb scheduling logic in the name of “reuse,” service boundaries blur and accountability weakens.
3.3 Data Domain
Platform transformation often changes how data is stored, shared, governed, and observed. This domain should identify authoritative data sources, data product ownership, integration and replication patterns, lineage expectations, and policy controls such as classification, retention, and residency. Coexistence matters here. The model needs to distinguish logical consistency from physical centralization, especially when legacy and target environments operate side by side.
3.4 Technology and Infrastructure Domain
This domain covers runtime environments, network zones, identity foundations, compute patterns, developer platforms, observability tooling, and resilience mechanisms. It should also capture the technical guardrails that shape consumption: approved deployment patterns, secrets management, telemetry standards, and recovery architectures. These are not just implementation details. They determine whether the platform can operate consistently at scale.
Technology lifecycle governance belongs here as well. For example, a model may show that the architecture board has approved Kafka as the strategic event backbone, placed a legacy ESB in containment mode, and set a retirement date for unsupported Java runtimes. Those lifecycle decisions shape both platform design and migration sequencing.
3.5 Governance and Operating Model Domain
This domain is often under-modeled, even though it is central to success. It includes ownership, funding boundaries, control points, policy enforcement, support responsibilities, and lifecycle decisions. Because platform transformation creates shared assets that cut across team and budget lines, the architecture has to show who decides, who operates, who consumes, and how exceptions are handled.
3.6 Modeling Perspectives
These domains should be viewed through several perspectives:
- Structural perspective: components, boundaries, dependencies
- Behavioral perspective: flows such as provisioning, deployment, incident escalation, and data exchange
- Temporal perspective: transition states, coexistence arrangements, migration waves, and decommissioning
- Control perspective: standards, risk controls, policy enforcement, and exception paths
The most useful models connect these domains and perspectives. A business capability should trace to consuming applications, those applications to data dependencies, those dependencies to platform services, and those services to ownership and control mechanisms. That traceability supports impact analysis, migration planning, and governance.
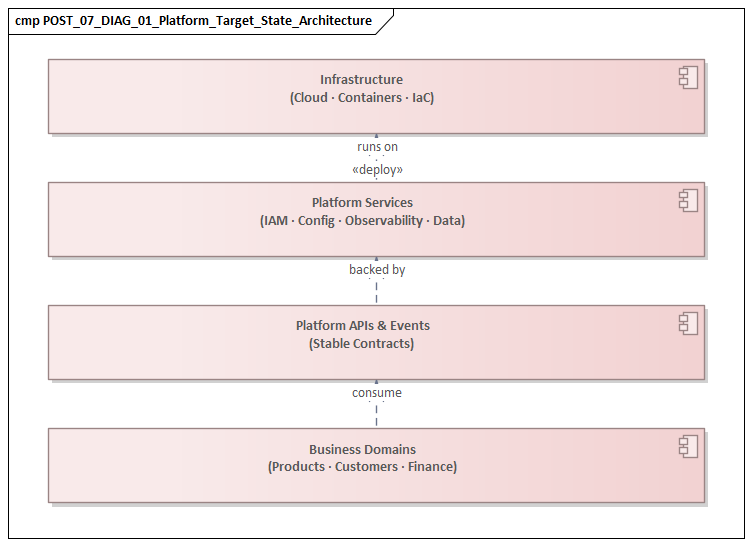
4. Target-State Design
The target state should be treated as a bounded direction, not a perfect snapshot of the future. Many transformations struggle because the target architecture is too polished, too complete, and too detached from organizational readiness. A credible target state defines intended structural outcomes clearly enough to guide decisions while leaving enough flexibility for phased adoption and legacy coexistence. Sparx EA guide
A strong target-state model answers a small set of critical questions:
- What capabilities will be provided centrally by the platform?
- Which capabilities remain within business domains?
- What standards are mandatory?
- Where is controlled variation acceptable?
- Which interfaces must remain stable during transition?
- What operating model changes are required for the target state to work?
These questions matter because platform transformation is not just a technology selection exercise. It is a redesign of responsibility, control, and reuse across the enterprise.
It is helpful to distinguish three elements in the target state:
- Core platform capabilities such as identity, engineering enablement, observability, runtime services, and common data access patterns
- Domain-facing services such as APIs, self-service workflows, templates, and managed offerings through which business teams consume the platform
- Enterprise control mechanisms such as security policy enforcement, resilience requirements, compliance checks, and financial accountability
This separation keeps the platform from turning into an undifferentiated collection of tools and controls. Just as important, it makes consumption clearer. Teams need to know not only what exists in the platform, but how they are expected to use it.
The target state also needs to reflect constraints and adoption realities. It has to account for regulatory obligations, legacy conditions, and skills availability. It also has to be usable by consumers. A target that is elegant on paper but difficult to adopt is not viable.
In practical terms, target-state design should identify a limited set of stable enterprise decisions: service boundary principles, identity and access foundations, integration conventions, data governance rules, observability expectations, and resilience patterns. For instance, an enterprise may standardize event-driven integration on Kafka for business events while keeping synchronous APIs for transactional queries. Decisions like that create coherence without prescribing every implementation detail. The aim is to standardize where consistency creates real value while leaving domains room to differentiate where business value depends on it.
A realistic target state also makes room for exceptions without normalizing them. A global insurer, for example, may standardize customer event publication through a central event backbone, yet allow a regional claims platform to retain a local batch integration for a fixed period because of regulatory reporting dependencies. The architecture should record both the standard and the exception path, including the conditions for retirement.
5. Transformation Roadmapping
If the target state provides direction, the roadmap provides realism. Static end-state diagrams do not show how change will actually unfold.
A transformation roadmap should identify:
- transition architectures
- migration waves
- enabling work packages
- major dependencies
- decision gates
- decommissioning triggers
The roadmap has to show not only what changes, but also what remains stable during change. In many transformations, the most important architectural work lies in designing the coexistence period: which interfaces remain fixed, how data is synchronized, where controls apply across old and new environments, and when legacy components can be retired.
A practical roadmap is usually organized around three criteria.
5.1 Capability Readiness
The platform has to be mature enough to support real consumption. Shared services should not be declared strategic before they offer acceptable reliability, documentation, support, and onboarding paths.
5.2 Dependency Reduction
Sequencing should reduce constraints such as brittle integrations, unsupported technologies, manual operational steps, and hard dependencies on legacy components. In many cases, this creates more long-term value than moving the most visible workloads first.
5.3 Value Release
The roadmap should deliver early, visible improvements. Faster provisioning, standardized deployment paths, better telemetry, simpler integration onboarding, or stronger recovery capabilities are often better early outcomes than ambitious but distant end-state moves.
Roadmapping should be evidence-based. Sequencing assumptions need to be tested against system criticality, team capacity, regulatory deadlines, vendor commitments, and data migration complexity. Some architectural moves are usually worth making early regardless of later detail—for example, identity standards, telemetry baselines, API conventions, and environment patterns—because they improve future optionality. By contrast, deep abstractions should not be fixed too early unless consumer needs are already clear.
Each transition stage should also have measurable exit criteria. A migration wave is not complete simply because workloads have moved. Completion should reflect operational stability, adoption quality, effective controls, and decommissioning progress. In an IAM modernization wave, for example, exit might require single sign-on in production, legacy admin accounts removed, and access recertification running through the new control path. That keeps the roadmap tied to transformation outcomes rather than technical activity alone.
A logistics company migrating warehouse applications to a new platform might therefore define wave completion in operational terms: deployment through the standard pipeline, telemetry feeding the central observability stack, privileged access moved to the enterprise PAM service, and the old batch scheduler decommissioned. Without those conditions, migration appears complete while legacy risk remains in place.
6. Governance, Decision-Making, and Stakeholder Alignment
The earlier sections describe what the platform is, why it exists, and how it should evolve. Governance determines whether those decisions can actually be made, applied, and sustained.
In platform transformation, governance should be understood as a system of decision rights, escalation paths, and accountability mechanisms. It is not primarily a review-heavy control layer. Its purpose is to allow the platform to evolve coherently while remaining usable for the teams that depend on it.
Platform transformation cuts across multiple authority structures. Enterprise architects define principles and guardrails. Platform teams own shared services and engineering standards. Security and risk functions impose mandatory controls. Product and domain teams remain responsible for delivery and local outcomes. If these roles are not modeled explicitly, governance becomes ambiguous, and teams either wait for decisions, duplicate them, or work around standards altogether.
A useful governance structure separates decisions into categories:
- Strategic decisions: platform scope, sourcing posture, centralization boundaries, enterprise standards
- Design decisions: reference patterns, integration conventions, data responsibilities, control implementation
- Operational decisions: service levels, incident boundaries, lifecycle management, exception handling
This prevents enterprise forums from being overloaded with local delivery matters while ensuring that enterprise-significant choices do not become fragmented. For example, an architecture board might decide that customer domain events must be published through Kafka with a standard schema contract, while leaving each product team free to choose its internal service decomposition.
Stakeholder alignment matters because different groups value the platform in different ways. Executives focus on risk, cost transparency, and transformation outcomes. Product leaders focus on speed, autonomy, and reliability. Engineers care about developer experience, documentation, and ease of integration. Control functions focus on auditability, resilience, and policy enforcement. Architecture models help align these interests by showing how one design choice can support several objectives at once—for example, how a standard deployment path can improve both delivery speed and control inheritance.
Governance works best when it is built into delivery flow. That means using architecture artifacts as decision instruments: standards profiles for mandatory rules, reference architectures for common patterns, exception registers for controlled deviations, and transition reviews for migration readiness. Pre-approved patterns should enable fast delivery in low-risk cases, while non-standard designs should trigger deeper review only when there is a clear reason.
The economic dimension matters as well. Shared capabilities are often funded centrally while adoption costs sit with domain teams, or domain teams are asked to consume services that are still immature. Governance should make funding and benefit flows visible. Otherwise, adoption may be mandated without a realistic path to success.
Finally, governance has to stay iterative. As platform adoption grows, consumer needs, regulatory pressures, and service boundaries will change. Feedback loops, adoption metrics, and periodic reassessment are essential if governance is to support learning rather than freeze the original design. free Sparx EA maturity assessment
7. Common Challenges, Risks, and Success Factors
The earlier sections describe a coherent transformation model. In practice, the difficulty is that technology, delivery practices, governance habits, funding logic, and team expectations often have to change at the same time. Several recurring risks deserve explicit attention.
7.1 Misalignment Between Platform Supply and Consumer Demand
Platform teams often build what they think teams should use, while product teams optimize for immediate delivery outcomes. The result is a gap between what is offered and what is actually adopted. That gap leads to wasted investment and parallel local solutions. The strongest corrective is to model the platform as a product and make consumer value explicit.
7.2 Unclear Service Boundaries and Ownership
When ownership of shared services, domain services, data products, and controls remains ambiguous, organizations end up with duplicated implementation, unresolved incidents, and lifecycle confusion. This is why the governance and operating model domain described in Section 3 is not optional. Clear service definitions, support expectations, and accountability boundaries matter as much as technical design.
7.3 Overengineering or Under-Designing the Platform
Some enterprises respond to fragmentation by creating an overly comprehensive platform with deep abstractions, broad mandatory standards, and heavy control workflows before real needs are proven. Others go too far in the opposite direction and end up with a loose toolset rather than a platform. The success factor is disciplined scope: standardize where enterprise value is clear, and avoid centralizing capabilities that consumers do not need or cannot yet adopt.
7.4 Legacy Coexistence and Migration Drag
Coexistence is unavoidable in most transformations. The risk is that temporary coexistence becomes permanent, leaving the enterprise with duplicated cost and complexity. Success depends on explicitly designing migration pathways, interface stability rules, and decommissioning criteria rather than assuming legacy retirement will happen on its own.
7.5 Adoption Friction
Adoption should be treated as an architectural concern, not just a change-management concern. A platform capability may be secure and elegant yet still fail if onboarding is difficult, documentation is weak, or operational support is poor. Useful measures include onboarding time, reuse rates, exception volumes, and incident patterns.
7.6 Progressive Standardization
Enterprises usually gain more from a small number of high-value, well-enforced standards than from a large catalogue of weakly adopted rules. Standards should focus on areas where consistency materially improves resilience, security, interoperability, or cost efficiency. Beyond that, controlled variation should remain possible where domain differentiation creates value.
The overall pattern is straightforward: platform transformation succeeds when coherence and usability stay in balance. The platform has to be governed strongly enough to reduce fragmentation, but designed well enough that teams are willing to use it.
Conclusion
Architecture modeling gives platform transformation its decision structure. It turns modernization from a set of disconnected initiatives into a coordinated change agenda by making business intent, platform design, operating model choices, and migration sequencing visible through a coherent set of views.
No single model is enough. Capability maps, service taxonomies, transition architectures, control models, and operating views each answer different questions. Their value comes from staying connected. Business drivers should trace to target-state choices. Target-state choices should trace to roadmap sequencing. Roadmap stages should trace to governance decisions, adoption measures, and decommissioning outcomes.
The most effective modeling approach is iterative and evidence-led. Models should be updated as adoption patterns emerge, dependencies are uncovered, and platform services prove either valuable or unnecessary. In that sense, architecture artifacts are not static deliverables. They are working instruments used in investment planning, design governance, migration reviews, and service lifecycle management.
The practical lesson is simple. Platform transformation succeeds when architecture stays close to execution. Models need to help leaders decide where to standardize, help teams understand how to consume shared capabilities, and help governance functions enforce control without creating unnecessary friction. Treated as living decision assets, architecture models reduce ambiguity, expose trade-offs early, and provide a clearer path from platform ambition to measurable enterprise change.
Frequently Asked Questions
What is enterprise architecture?
Enterprise architecture is a discipline that aligns an organisation's strategy, business processes, information systems, and technology. It provides a structured approach to understanding the current state, defining the target state, and managing the transition — using frameworks like TOGAF and modeling languages like ArchiMate.
How does ArchiMate support enterprise transformation?
ArchiMate supports transformation by modeling baseline and target architectures across business, application, and technology layers. The Implementation and Migration layer enables architects to define transition plateaus, work packages, and migration events — creating a traceable roadmap from strategy through to implementation.
What tools are used for enterprise architecture modeling?
The most widely used tools are Sparx Enterprise Architect (ArchiMate, UML, BPMN, SysML), Archi (ArchiMate-only, free), and BiZZdesign Enterprise Studio. Sparx EA is the most feature-rich — supporting concurrent repositories, automated reporting, scripting, and integration with delivery tools like Jira and Azure DevOps.