⏱ 22 min read
Modeling Application Landscapes with ArchiMate: A Practical Architecture Guide ArchiMate training
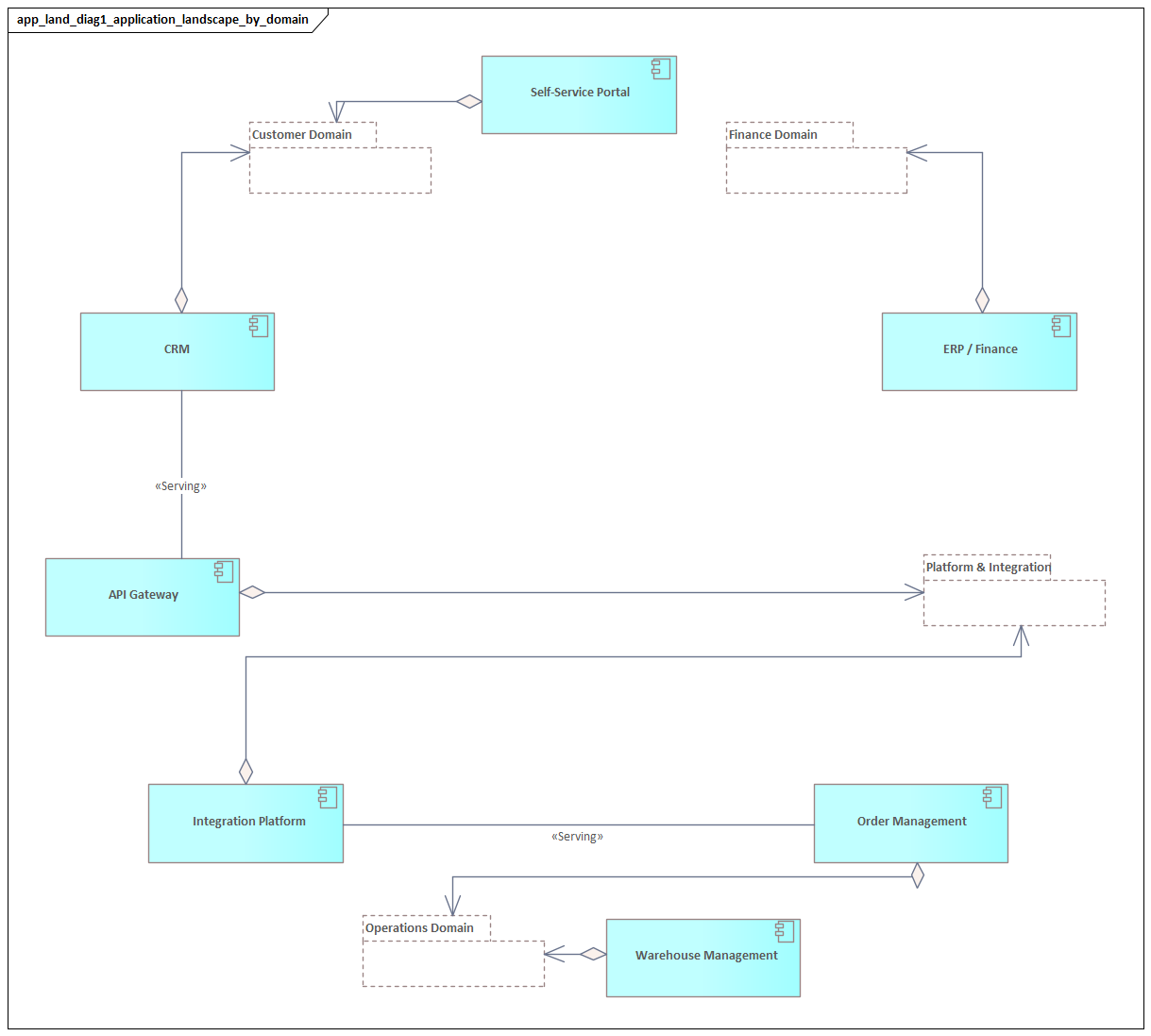
Learn how to model application landscapes with ArchiMate to visualize systems, dependencies, interfaces, and business alignment for better enterprise architecture decisions. ArchiMate tutorial for enterprise architects
Modeling Application Landscapes, ArchiMate, ArchiMate application architecture, enterprise architecture, application landscape modeling, application dependencies, architecture visualization, business capability mapping, IT portfolio management, systems integration, application interfaces, architecture governance ArchiMate layers explained
Introduction
Few enterprises have a tidy application estate. Most operate a layered mix of packaged platforms, custom systems, cloud services, legacy applications, middleware, data stores, APIs, and event-driven components accumulated over many years. The landscape keeps shifting as priorities change, regulations tighten, acquisitions add complexity, and delivery teams introduce new solutions. The architect’s task is not simply to catalog systems, but to model them in a way that makes dependencies, risks, and change options visible.
ArchiMate is well suited to this work because it provides a consistent language for representing applications in their wider enterprise context. Rather than treating applications as isolated software assets, it links them to business capabilities, processes, data, technology, and organizational concerns. The result is not just an inventory. It is a structured view of how the estate actually works. ArchiMate relationship types
A useful application landscape model answers practical questions. Which applications support a given business capability? Where are services duplicated? Which systems are tightly coupled and therefore hard to change? Where is critical data mastered, replicated, or exchanged? Which platforms are plausible candidates for modernization, consolidation, or retirement? These are not documentation questions; they are decision questions. An architecture board reviewing a proposal for a second customer onboarding solution, for example, needs to see more than the proposed application. It needs to understand overlap with existing platforms, identity dependencies, and the services already in use.
One of ArchiMate’s strengths is that it distinguishes structure, behavior, and exposure. In application landscape work, that means separating the application component itself from the services it provides, the interfaces through which those services are consumed, and the data it uses or produces. That distinction prevents a common modeling failure: turning every “system” into the same undifferentiated box. It also gives architects a firmer basis for reasoning about ownership, reuse, coupling, and replacement. ArchiMate modeling best practices
Notation matters, but modeling discipline matters more. A landscape model should be shaped by the decisions it needs to support, not by an urge to capture every available detail. In large enterprises, complete coverage is rarely achievable and often not especially helpful. A better approach is iterative: establish the core structural map, connect it to business meaning, add the data and dependency relationships that matter most, and publish targeted viewpoints for different stakeholders. The best model is not the most detailed one. It is the one that makes change easier to understand and govern.
The sections that follow build on that foundation. First, we examine why application landscape modeling matters in enterprise architecture. Then we introduce the core ArchiMate concepts and relationships needed to model the application layer effectively. From there, the article outlines a practical step-by-step method, reviews common patterns and viewpoints, and closes with governance practices that keep the model useful over time.
Why Model Application Landscapes in Enterprise Architecture
Application landscape modeling matters because enterprise architecture exists to support informed change. Organizations rarely struggle simply because they have many applications. They struggle because the relationships between those applications are poorly understood. Decisions are then made locally, while the consequences surface elsewhere in the estate.
The application landscape is the operational result of years of accumulated decisions: acquisitions, project-led implementations, tactical integrations, local optimizations, regulatory responses, and platform choices. Modeling the landscape makes those decisions visible. It helps architects distinguish intentional architecture from accidental complexity. That distinction is essential when assessing whether the estate is coherent, fragmented, over-customized, or overly dependent on a small number of critical systems.
Application landscape models also provide meaning that a basic inventory usually cannot. A spreadsheet or CMDB may record products, owners, and lifecycle dates, but it rarely explains why an application exists, which business outcomes depend on it, or what else would be affected if it changed. By linking applications to business capabilities, processes, services, and data, enterprise architecture turns a list of systems into a decision instrument.
This becomes especially important during transformation. A cloud migration, ERP replacement, or post-merger integration cannot be planned safely from a portfolio list alone. Two applications may appear similar at a high level, yet one may expose stable services and have clear data ownership while the other depends on manual workarounds, local reporting, and undocumented integrations. The model brings those hidden dependencies into view and improves sequencing, funding decisions, and risk planning.
A realistic example is IAM modernization. Replacing the directory or identity provider is often the easy part. The harder task is identifying every application that consumes authentication, authorization, or provisioning services differently. In one estate, a customer portal may already use OIDC through a central identity platform, while an older call-center application still relies on LDAP lookups and a nightly role feed. Those distinctions materially affect migration effort and cutover risk.
There is also a strong operational case. Incidents and cyber events rarely stay confined to a single application. Their business impact depends on how they spread across integrations, shared platforms, identity services, and data exchanges. A landscape model helps identify concentration risk, unsupported technologies, and critical dependency chains. It gives architecture, operations, resilience, and security teams a shared understanding of what is business-critical and why.
It also improves decision traceability. Recommendations such as retain, replace, replatform, or retire carry more weight when they are tied to modeled evidence: duplicated services, excessive coupling, weak data ownership, poor strategic fit, or high change cost. A board decision to retire an unsupported integration server, for example, is easier to defend when the model shows which business processes, APIs, and downstream applications depend on it.
The point is not to produce a perfect diagram. The point is to create a reliable architectural instrument that supports analysis, governance, and execution. The rest of this article explains how ArchiMate provides that instrument, starting with the core concepts of the application layer.
Core ArchiMate Concepts for the Application Layer
ArchiMate is particularly effective here because it separates structure, behavior, exposure, and information. That separation is what allows a landscape model to say something precise about how applications fit together.
Application Component
The primary structural element in the application layer is the Application Component. It represents a software unit with a recognizable responsibility in the landscape, such as an ERP platform, billing engine, customer portal, API gateway, or mobile backend.
The modeling discipline is important. Application components should be meaningful architectural building blocks, not a direct copy of the software inventory. A commercial product may map neatly to one component, but a large platform may need to be split into several components if different modules are owned, changed, or consumed independently. The test is practical: does the distinction affect ownership, lifecycle, integration, or change planning?
Consider a bank that uses a core lending platform. Treating the whole platform as one application component may be too coarse if loan origination, servicing, and collections are managed by different teams and are being modernized on different timelines. In that case, separate components produce a more useful model than one large box labeled “Lending System.”
Application Behavior
ArchiMate provides several elements for application behavior:
- Application Function for stable internal behavior, such as pricing calculation or identity validation
- Application Process where sequence or flow matters, such as order orchestration
- Application Interaction for collaborative behavior between components
These elements help when stakeholders need to understand operational responsibility rather than just connectivity. Even so, they should be used selectively. In many landscape models, the main concern is what applications provide and consume, not every internal step they perform.
Application Service
The Application Service is one of the most important concepts in application landscape modeling. It represents externally visible behavior offered to consumers. Examples include customer profile management, payment authorization, shipment tracking, quotation generation, or token issuance in an IAM platform.
Services move the model away from product-centric thinking and toward consumer-oriented thinking. That shift is critical for identifying duplication and planning change. Two different applications may realize the same service, and that insight is often more useful than knowing they are different products.
A typical example appears in insurance. A legacy policy administration platform and a newer digital underwriting service may both provide a quotation service. On paper they are separate applications. Architecturally, the more important question is why two different components are realizing the same business-facing service, and whether that duplication is transitional, justified, or simply unmanaged overlap.
Application Interface
An Application Interface represents the access point through which a service is exposed. It may correspond to an API, message endpoint, batch boundary, file transfer mechanism, event topic, or user-facing interface.
Interfaces matter because they show how consumers access behavior. They also make integration style visible. Asynchronous messaging, synchronous APIs, events, and manual interaction each have different consequences for resilience, latency, and change impact.
Data Object
The Data Object represents information used or produced by applications, such as customer record, invoice, claim, or product catalog. It is not intended to replace a full data model. Its purpose is to show where business-relevant information is created, mastered, accessed, or replicated.
This becomes especially important when application problems are really data problems in disguise. A landscape may seem fragmented because there are many systems, while the deeper issue is unclear ownership of core data objects.
For example, a retailer may have e-commerce, POS, loyalty, and CRM platforms that all update customer contact details. The visible symptom is integration noise. The underlying architectural issue is that “Customer” has no clear system of record and no governed ownership pattern.
Why These Distinctions Matter
These concepts matter because they stop the model from collapsing into a vague set of “systems” connected by unlabeled lines. Decisions about modernization, consolidation, and risk depend on understanding more than what applications exist. Architects need to know:
- what they are responsible for
- what services they expose
- how those services are consumed
- what data they depend on
Once those distinctions are in place, the next task is to connect them using the right ArchiMate relationships.
Key ArchiMate Relationships for Representing Application Landscapes
If elements provide the nouns of the model, relationships provide the logic. Most architecture questions are dependency questions: what supports what, what consumes what, what changes when something is removed, and where risk propagates. Relationship discipline is therefore what makes a landscape model analytically useful.
Serving
The Serving relationship shows that one element provides useful behavior to another. In application landscapes, it is often used to show that an application service supports a business process, another application component, or a channel.
Serving is more informative than a generic connection line because it expresses dependency in terms of utility. It tells the reader that one element relies on the behavior offered by another.
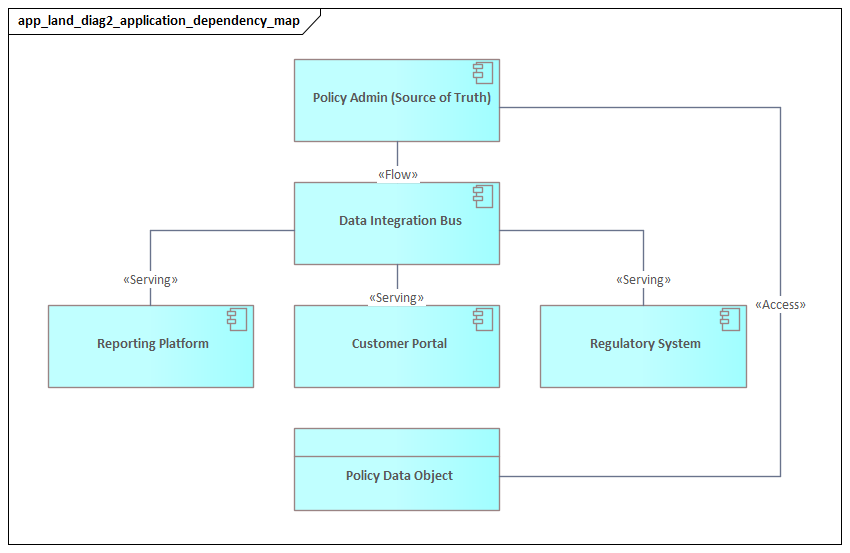
Realization
The Realization relationship connects an abstract element to the element that implements it. A common use is to show that an application component realizes an application service.
This matters because services and components are not the same thing. An enterprise may want to preserve a service while replacing the component that realizes it. Realization makes that distinction explicit.
Access
The Access relationship shows that a component or behavior element reads, writes, or otherwise uses a data object. This is one of the most valuable relationships when analyzing systems of record, data replication, and ownership ambiguity.
If many applications write to the same data object, the model may reveal weak governance or integrity risk. If many applications only read from a single source, that source may be a resilience hotspot.
Triggering
The Triggering relationship indicates that one behavior element starts or influences another. It is useful for showing orchestration, batch dependencies, event-driven flows, and operational handoffs.
Triggering should be used carefully because it implies temporal or causal dependency, not just interaction. In practice, it often exposes hidden fragility in business-critical chains. A nightly settlement process that triggers invoice generation, which in turn triggers a regulatory reporting extract, is a much more fragile sequence than three systems merely exchanging data independently.
Flow
The Flow relationship shows transfer between elements, such as the movement of information or events. In application landscape models, it can clarify how messages, files, or requests move across components without dropping into low-level integration design.
For instance, an order service may publish an OrderCreated event to Kafka, and that event then flows to fulfillment, billing, and analytics consumers. Modeling the flow makes it easier to discuss propagation paths, latency expectations, and failure handling without turning the landscape view into an implementation diagram.
Composition and Aggregation
Composition and Aggregation help structure the model itself. They are useful for grouping applications into suites, domains, or product families.
- Composition implies a stronger whole-part relationship
- Aggregation groups related elements more loosely
This distinction is useful when representing packaged ecosystems or domain groupings without overstating lifecycle dependency.
Relationship Discipline
Relationships should be chosen according to the questions the model needs to answer. For rationalization, serving and realization may be central. For resilience and operational risk, access, triggering, and flow are often more important. Overuse of generic associations weakens the model’s analytical value and makes diagrams harder to interpret.
With the core concepts and relationships in place, the next step is to build the model in a disciplined way.
A Step-by-Step Approach to Modeling an Application Landscape with ArchiMate
A useful application landscape model is built iteratively. The goal is not completeness for its own sake, but enough structure and dependency detail to support real decisions.
1. Define the Decision Context
Start with the question the model must support: portfolio rationalization, modernization planning, resilience assessment, merger integration, or target-state governance. This determines the level of detail required and the viewpoints that will matter later.
Without a clear purpose, models tend to become broad but shallow.
2. Set the Scope Boundary
“The entire application landscape” is usually too large to model effectively in a single view. Scope should be bounded by a business domain, capability cluster, value stream, geography, or transformation initiative.
A bounded scope improves ownership, validation, and maintainability. It also reduces the temptation to create an unreadable flat map of the whole estate.
3. Establish the Structural Backbone
Identify the major application components first: core platforms, channels, domain systems, integration hubs, and shared services. At this stage, focus on architectural building blocks rather than modules, microservices, or databases.
The purpose is to reveal the shape of the estate. Application components should reflect meaningful responsibility, not just software inventory entries.
4. Add Services and Interfaces
Once the main components are visible, identify the key application services they expose and the interfaces through which those services are consumed. This is where the model begins to show not just what systems exist, but how they provide value to other parts of the enterprise.
It also becomes much easier to spot duplicated services and tightly coupled integrations. A practical example is a manufacturer whose dealer portal, mobile service app, and contact-center desktop all consume “Warranty Claim Submission.” If one channel uses an API, another relies on file upload, and the third depends on manual re-entry into the core claims platform, the interface differences become architecturally significant.
5. Connect to Business Meaning
Link application services or components to business capabilities, processes, or value stream stages. This turns the model into an enterprise architecture asset rather than a technical topology diagram.
That traceability is what allows the model to support investment and transformation decisions. If a claims handling capability depends heavily on a platform nearing end of support, the case for remediation becomes much stronger when the dependency is visible.
6. Introduce Key Data Objects
Add a limited set of business-relevant data objects such as customer, order, policy, or invoice. Then use access relationships to show where those objects are created, mastered, read, or updated.
This often reveals that integration complexity is really data ownership complexity. In many estates, the issue is not that too many applications exchange data, but that nobody has defined where authoritative change is supposed to occur.
7. Refine Dependency Semantics
Now add the relationships that matter most for analysis: serving, realization, access, triggering, and flow. This is usually the point where hidden issues start to surface, including:
- circular dependencies
- point-to-point integration sprawl
- duplicated services
- excessive reliance on shared platforms
- unclear data ownership
In event-driven estates, this step often shows whether Kafka is being used as a clean event backbone or as a hidden integration layer carrying opaque, tightly coupled payloads.
8. Create Targeted Viewpoints
Maintain one coherent underlying model, but publish different views for different audiences. Executives may need a capability-to-application map. Domain architects may need service dependency views. Delivery teams may need transition-focused slices.
This is a repository-and-viewpoint discipline, not a diagramming preference. The repository holds the architectural truth; the viewpoints make that truth usable.
9. Validate and Operationalize
Review the model with application owners, integration specialists, business architects, and operations teams. Then connect it to governance processes such as project initiation, solution approval, lifecycle management, and incident impact assessment.
A landscape model becomes valuable when it is reused in decisions, not when it is simply documented.
Common Patterns, Viewpoints, and Use Cases
Once the core model exists, its value increases when recurring structures can be recognized and presented through targeted viewpoints. The underlying model should support multiple questions without forcing every audience to consume the same level of detail.
Common Landscape Patterns
System of Record with Surrounding Consumers
A central application owns a critical data domain, while multiple channels, reports, and downstream applications consume its services or replicated data. This pattern is common in customer, finance, product, and policy domains.
The key architectural question is not simply which system is the master, but how dependency is distributed around it. Stable service exposure creates manageable dependency. Direct database reads and uncontrolled extracts create fragility.
Integration Hub or Mediation Layer
Applications connect through an ESB, API platform, event broker, or iPaaS layer. This can represent genuine decoupling, but it can also conceal centralized complexity.
The model should show whether the hub acts as a clean interface boundary or whether it accumulates transformation logic, sequencing rules, and business behavior that belong elsewhere.
Suite-and-Satellite Landscape
A large packaged platform provides broad functional coverage, while specialized applications fill gaps around it. This is common with ERP, CRM, and core industry platforms.
The architectural question is whether satellites are strategic extensions exposed through governed services or unmanaged drift created by local workarounds and duplicate data handling.
Strangler or Transition Coexistence
Legacy and target systems operate in parallel while responsibilities gradually shift. This pattern sits at the center of many modernization programs.
A useful model shows which services remain on the legacy platform, which have moved, and what temporary synchronization or routing mechanisms exist between them. Transition complexity usually sits in that overlap zone.
A common example is a payments modernization program where account validation has moved to a new cloud service, settlement remains on the mainframe, and customer notifications are produced by a separate digital platform. The architecture risk is not any one component in isolation. It is the temporary coexistence arrangement and the dependencies created by it.
Useful Viewpoints
Capability-to-Application Viewpoint
Shows which applications support which business capabilities. This is effective for rationalization, investment planning, and identifying overlap or under-support.
Application Cooperation Viewpoint
Highlights service consumption, interactions, and dependency chains. This is useful for resilience analysis, impact assessment, and integration planning.
Data-Centric Application Viewpoint
Focuses on data objects, ownership, replication, and exchange. This is especially useful when governance issues are driven by inconsistent data definitions or fragmented reporting.
Plateau and Migration Viewpoint
Shows baseline, transition, and target states across a transformation program. This helps preserve traceability between current reality and intended design.
Typical Use Cases
These patterns and viewpoints support several high-value enterprise architecture use cases:
- identifying candidates for consolidation
- exposing technical debt that creates business risk
- assessing cloud migration complexity
- comparing overlapping estates after mergers
- understanding business blast radius during incidents
- planning resilience testing and control design
They also support practical governance cases. A legacy identity platform may be technically ready for retirement, but the model may show that several internal applications still depend on proprietary authentication flows. Likewise, a middleware product nearing end of support may look like a simple technology refresh until the landscape view reveals that it underpins revenue-critical order and billing integrations.
The principle is straightforward: not every stakeholder needs the whole model. Strong application landscape practices rely on one coherent repository that can produce focused views for specific decisions.
Governance, Maintenance, and Best Practices
An application landscape model only delivers lasting value if it is maintained as an architectural asset. Otherwise, it quickly becomes a one-off project artifact that stakeholders stop trusting.
Establish Clear Accountability
Each major application component, service, and integration should have an identifiable owner or steward. Enterprise architecture should define standards and quality rules, but it should not become the sole source of truth for operational detail.
A federated stewardship model is usually more sustainable than a fully centralized one.
Define “Good Enough” by Risk and Change
Not every application needs the same modeling depth. A business-critical platform in active transformation may justify detailed services, interfaces, data objects, and dependency paths. A low-impact utility may need only basic metadata and a few key relationships.
Model depth should reflect decision relevance, not modeling ambition.
Tie Updates to Delivery and Change Processes
The best trigger for maintenance is not an annual review. It is project initiation, solution approval, production go-live, lifecycle status change, or major incident review.
When model updates are built into delivery governance, the repository stays aligned with reality.
Use Lightweight Modeling Standards
Models degrade quickly when naming is inconsistent, abstraction levels vary, and relationships are used loosely. Define simple conventions such as:
- how to distinguish products from application components
- when to model an interface explicitly
- which relationships are preferred in common scenarios
- how to represent integration patterns consistently
A small set of enforced standards is usually more effective than a large manual.
Maintain Baseline, Transition, and Target Views
Transformation programs often require more than a current-state model. Architects also need to preserve approved target states and intermediate plateaus.
This is especially important in large programs where different teams might otherwise work from inconsistent assumptions.
Optimize for Usefulness, Not Just Accuracy
A model can be accurate and still have limited value if it does not answer common questions quickly. Stakeholders should be able to ask:
- Which applications depend on this platform?
- Which services expose customer data?
- What breaks if this component is retired?
- Which capabilities rely on this legacy system?
If the model cannot support those questions, the answer is usually not more detail. It is better structure, better viewpoints, or better governance.
Technology lifecycle governance is a good example. If a database platform is moved to sunset status, the model should quickly show which applications still run on it, which capabilities they support, and whether replacement depends on other transition work already in flight.
Conclusion
Modeling an application landscape with ArchiMate is valuable when it turns architectural complexity into decision-ready insight. The notation is not the goal. The goal is a coherent, maintainable representation of the application estate that supports planning, governance, delivery, and operations.
The strongest models begin with a clear purpose, use a disciplined set of application-layer concepts, and apply relationships carefully enough to make dependency visible. They are built iteratively, tied to business meaning, and published through targeted viewpoints rather than forced into a single all-purpose diagram.
They also need to be governed as living assets. Without stewardship, standards, and integration into change processes, even a well-designed model loses credibility. With those practices in place, however, the model becomes more than documentation. It becomes a practical instrument for rationalization, modernization, resilience analysis, and investment decision-making.
Ultimately, the quality of an application landscape model should be judged by whether it helps the enterprise evolve with greater control. If it reveals duplication, clarifies ownership, exposes risk, and improves the sequencing of change, then ArchiMate is doing what it should: providing a shared architectural language for understanding and improving the application estate.
Frequently Asked Questions
What is enterprise architecture?
Enterprise architecture is a discipline that aligns an organisation's strategy, business operations, information systems, and technology infrastructure. It provides a structured framework for understanding how an enterprise works today, where it needs to go, and how to manage the transition.
How is ArchiMate used in enterprise architecture practice?
ArchiMate is used as the standard modeling language in enterprise architecture practice. It enables architects to create consistent, layered models covering business capabilities, application services, data flows, and technology infrastructure — all traceable from strategic goals to implementation.
What tools are used for enterprise architecture modeling?
Common enterprise architecture modeling tools include Sparx Enterprise Architect (Sparx EA), Archi, BiZZdesign Enterprise Studio, LeanIX, and Orbus iServer. Sparx EA is widely used for its ArchiMate, UML, BPMN and SysML support combined with powerful automation and scripting capabilities.