⏱ 24 min read
ArchiMate Digital Platform Architecture Example | Enterprise Architecture Guide ArchiMate training
Explore an ArchiMate digital platform architecture example with practical insights into business, application, and technology layers for enterprise architecture teams. ArchiMate tutorial for enterprise architects
ArchiMate digital platform architecture example, ArchiMate example, digital platform architecture, enterprise architecture, ArchiMate model, ArchiMate business application technology layers, platform architecture diagram, enterprise architecture framework, digital transformation architecture, ArchiMate tutorial ArchiMate layers explained
Introduction
Digital platforms are now a standard architectural pattern for enterprises that need speed, scale, and the ability to work across products, channels, and partner ecosystems. Unlike traditional application landscapes organized around isolated business functions, a digital platform provides a shared foundation: reusable capabilities, common data access patterns, integration services, technology services, and governance mechanisms. With that foundation in place, organizations can create and evolve digital products faster and with greater consistency.
In enterprise architecture, a digital platform is more than a cloud environment, an API layer, or a collection of shared tools. It is a cross-layer architectural construct that connects business intent, the operating model, application services, and technology infrastructure. Its value comes from leverage. Capabilities such as identity, integration, workflow, analytics, observability, and policy enforcement are built once and used many times. That reduces duplication, improves consistency, and shortens delivery cycles.
ArchiMate is well suited to this kind of architecture because platforms cut across boundaries by design. They span strategy, business capabilities, value streams, application services, integrations, and runtime environments. ArchiMate provides a consistent language for showing how these elements connect, so the model becomes more than a technical inventory. It becomes a way to trace strategic goals into business capabilities, application services, and supporting technology. That traceability matters when assessing investment priorities, change impacts, risk concentration, and governance decisions. For instance, an architecture board might approve a common API gateway pattern for all external interfaces while rejecting a separate gateway proposed by one business unit because it would duplicate security controls, support processes, and licensing cost. ArchiMate relationship types
A practical digital platform architecture usually includes recurring elements at every layer. At the business layer, it supports capabilities and value streams such as customer onboarding, partner integration, digital product delivery, and service fulfillment. At the application layer, it exposes reusable services such as identity and access, API management, event distribution, notifications, workflow orchestration, payments, and analytics. At the technology layer, it relies on cloud foundations, container or managed runtime platforms, data services, event infrastructure, security controls, and operational tooling. The architecture works only when those layers are designed as a coherent whole.
This article uses an ArchiMate example to show how that coherence can be modeled. It starts with the business rationale for a platform, then moves through the application and technology layers, and finally shows how cross-layer traceability supports governance and roadmapping. The aim is not merely to document a platform, but to show how an enterprise can shape one so that reuse, interoperability, and controlled evolution are built in from the start. ArchiMate modeling best practices
What Is a Digital Platform in Enterprise Architecture?
In enterprise architecture, a digital platform is an intentionally designed foundation that enables multiple digital solutions to be created, integrated, operated, and evolved in a consistent way. It is not a single application, and it is not just infrastructure. It is a reusable enterprise asset that provides shared services, standards, data access mechanisms, and operational capabilities for many products, teams, and stakeholders.
The defining characteristic of a platform is leverage. Rather than having each project build its own identity management, monitoring, integration logic, partner connectivity, or workflow tooling, those capabilities are provided once as reusable services. That is what makes the platform strategically important. It allows the enterprise to build many digital products on top of a common backbone instead of repeatedly rebuilding the same foundations.
One useful way to distinguish a digital platform from a conventional solution is to look at its consumers. A traditional application usually serves a defined user group and a bounded business purpose. A platform serves many consumers at once: product teams, business units, operations teams, partners, external developers, and sometimes customers directly. As a result, platform services need to be modular, interfaces need to be stable, onboarding needs to be simple, and governance needs to be strong enough to preserve consistency without slowing delivery to a halt.
A platform is also a cross-layer construct. It links business needs to application and technology structures. An enterprise may offer multiple digital products across web, mobile, and partner channels, while all of them depend on the same authentication, API exposure, event handling, consent management, and analytics services. In that situation, the platform is not merely supporting delivery; it is shaping how the enterprise operates digitally.
A retail bank offers a simple example. Its mobile app, broker portal, and mortgage origination solution may look like separate products, but all three can rely on the same customer identity service, fraud event stream, document notification service, and audit logging pattern. From a platform perspective, those shared services matter more than the channel-specific user interfaces because they determine consistency, control, and delivery speed across the portfolio.
Another important point is that a true platform combines functional and non-functional capabilities. Functional services might include payments, notifications, search, or case management. Non-functional capabilities include security, resilience, scalability, observability, deployment automation, and policy enforcement. If the functional services exist but the non-functional controls are weak, the result is not an enterprise platform but a fragile shared environment.
That has direct implications for ownership and governance. A digital platform needs clear accountability for service design, interface standards, versioning, data contracts, service levels, and lifecycle management. It also requires a product mindset. Platform capabilities need to be managed as long-lived assets with roadmaps, adoption goals, and measurable outcomes, rather than as temporary outputs of a one-time transformation program. A common example is IAM modernization: instead of separate application logins and local role models, the enterprise introduces a shared identity service with federation, centralized policy, and standardized access patterns for new products.
In ArchiMate, that means the platform should be modeled as more than a technical layer. It may realize business capabilities, expose application services, use data objects, depend on technology services, and be constrained by principles and requirements. That broader representation is what makes ArchiMate valuable for platform architecture: it shows the platform as a mechanism for enterprise-wide reuse, control, and change.
Why Use ArchiMate for Digital Platform Modeling?
The main challenge in platform architecture is not documenting individual components. It is showing how the whole structure works across layers. ArchiMate is well suited to that task because it provides a single modeling language for strategy, business, application, and technology concerns. That consistency matters when a platform needs to be understood by executives, architects, delivery teams, and operational stakeholders alike.
One of the clearest reasons to use ArchiMate is that it moves the conversation beyond technical inventory. Many platform descriptions amount to little more than lists of cloud services, APIs, middleware, and tools. Those lists may be useful operationally, but they do not explain why the platform exists, which business capabilities it enables, or how it supports enterprise outcomes. ArchiMate allows architects to connect platform elements to business capabilities, value streams, and strategic drivers, turning the model into something that supports decisions rather than simply recording assets.
This becomes especially important when shared platform investments compete with visible product delivery. A customer-facing feature is easy to justify because its value is direct. A shared identity service, observability stack, or event backbone can seem indirect unless reuse is made visible. ArchiMate helps show that these are not isolated technical assets but enabling services used by many products and processes. That makes investment, prioritization, and governance discussions far more concrete.
ArchiMate also supports multiple levels of abstraction. The same platform can be represented conceptually for executives, logically for enterprise architects, and more concretely for engineering teams. An executive view may emphasize capabilities, value streams, and outcomes. A delivery view may focus on application services, interfaces, and dependencies. A technology view may show runtime environments, deployment patterns, and infrastructure controls. Because these views are based on the same underlying model, they remain semantically aligned.
There is also a practical benefit in dependency analysis. Platforms create leverage, but they also create concentration risk. Shared services such as identity, API management, event distribution, or observability can become critical dependencies for many teams. By modeling serving, realization, access, and flow relationships, ArchiMate makes those dependencies visible. That supports impact analysis when introducing a new integration style, changing a core service, or assessing resilience and operational risk.
Consider a healthcare provider exposing appointment booking through web, mobile, and partner referral channels. In a simple inventory, architects might list an API gateway, an identity provider, and a scheduling service. In an ArchiMate model, those components can be tied to the business capability of Care Access Management, the value stream Book Appointment, and the operational requirement for auditability. That changes the discussion. A gateway outage is no longer seen as a technical issue in isolation; it becomes a direct risk to patient access and partner operations.
Finally, ArchiMate is valuable because platforms are never finished. New products, data services, partner channels, and governance requirements appear over time. A structured model provides a baseline for gap analysis, transition planning, and roadmap communication. It helps the enterprise understand not only what exists, but how the target platform should evolve without losing coherence.
Business Layer View: Capabilities, Value Streams, and Stakeholders
If the platform is a shared enterprise asset, the business layer explains why it exists and who it serves. This is the foundation for the application and technology views that follow. Without a clear business purpose, the rest of the model quickly turns into a technical catalog rather than an architectural design.
A practical place to start is the capability map. In a digital platform context, capabilities often include Customer Identity Management, Partner Onboarding, Digital Product Management, API Consumption Management, Data Insight Delivery, Service Fulfillment Coordination, and Platform Governance. These are not systems; they are stable business abilities the enterprise must possess. In ArchiMate, capabilities can be linked to outcomes such as reduced onboarding time, a more consistent customer experience, improved compliance, or faster launch of digital services.
Value streams add the time dimension by showing how value is created. Common examples include Acquire Customer, Onboard Partner, Deliver Digital Service, Resolve Customer Issue, and Launch New Product Feature. Each value stream depends on multiple capabilities. Launch New Product Feature, for instance, may rely on Digital Product Management, Platform Governance, API Consumption Management, Identity Management, and Analytics Enablement. Modeling those relationships helps reveal where weak business capabilities will slow delivery.
Stakeholders should also be modeled explicitly. A digital platform usually serves customers, partners, product managers, internal development teams, operations teams, compliance officers, and executive sponsors. Their concerns are different. Customers care about seamless access and reliability. Partners want predictable integration and straightforward onboarding. Product teams want reusable services they can consume with minimal friction. Compliance stakeholders want traceability and policy enforcement. Making those actors visible keeps the platform grounded in real enterprise expectations rather than abstract technical ambition.
This is also where architectural tensions begin to surface. Platform initiatives often struggle because different stakeholders expect different outcomes: lower cost, faster delivery, stronger governance, ecosystem growth, or tighter standardization. ArchiMate helps by linking stakeholders to drivers, capabilities, and outcomes. That makes trade-offs explicit and supports more realistic governance and funding decisions.
In a manufacturing enterprise, for example, the partner onboarding capability may serve distributors, logistics providers, and aftermarket service partners. The value stream may look straightforward on paper, but stakeholder concerns differ sharply. A distributor may want fast API onboarding for inventory checks, while a regulated logistics provider may need stronger identity proofing and message retention. Modeling both concerns at the business layer prevents the platform from adopting a one-size-fits-all pattern that works for neither.
The business layer is also useful for deciding what should be shared. If a capability supports many value streams and many stakeholders, it is a strong candidate for platform ownership. If it supports only one narrow domain process, it may belong inside a product or business domain rather than the shared platform. This is one of the most important design decisions in enterprise platform architecture. Over-centralization creates bureaucracy; under-centralization creates duplication and inconsistency.
For that reason, the business layer should not be treated as a generic executive summary. It is a decision tool. It establishes the business rationale for shared services and creates the reference point for the application layer. Once the capabilities, value streams, and stakeholders are clear, reusable application services can be modeled with much greater precision.
Application Layer View: Platform Services, Components, and Integrations
Once the business rationale is clear, the next step is to show how the platform delivers reusable behavior. The application layer is where the platform becomes operationally meaningful. It should reflect the business-layer decisions about what is shared, who consumes it, and which value streams it supports.
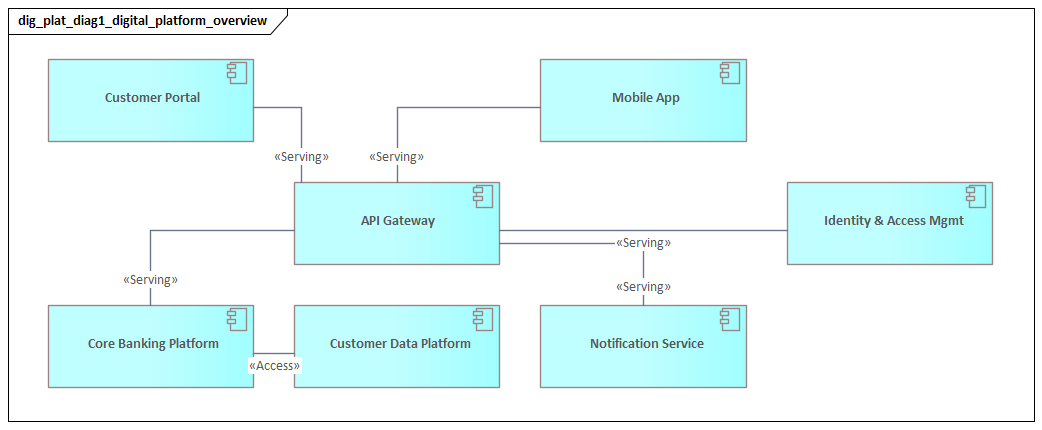
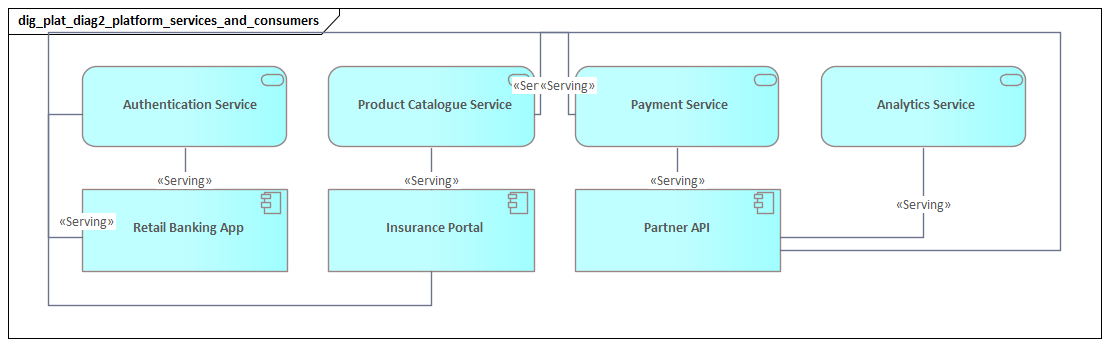
A helpful modeling pattern is to distinguish platform services from consumer solutions. Platform services are reusable application services exposed for use across many products and teams. Typical examples include Identity and Access Service, API Gateway Service, Event Publishing Service, Notification Service, Workflow Orchestration Service, Payment Service, Consent Management Service, and Analytics Service. These services represent what the platform provides to the rest of the enterprise.
Beneath those services sit the application components that realize them. An Identity Provider component may realize the Identity and Access Service. An API Management component may realize the API Gateway Service. An Event Broker may realize the Event Publishing Service. More complex services may be realized by several components working together. A Customer Insight Service, for example, may depend on a customer data platform, a rules engine, and an analytics engine. Modeling the service separately from its implementation matters because the service boundary should stay stable even when the underlying technology changes.
Integrations deserve particular attention because they determine whether the platform can scale across teams and domains. A digital platform usually supports multiple consumers, so it rarely relies on a single integration style. A good model shows where synchronous APIs are used, where asynchronous events make more sense, and where batch or file-based exchange still exists. ArchiMate can make those interaction patterns explicit through interfaces, flow relationships, and access relationships. For example, an order service may publish OrderCreated and OrderShipped events to Kafka, while customer-facing applications still call pricing and account APIs synchronously.
This is also where the distinction between shared services and domain-specific logic needs to remain sharp. Not every application used in a digital environment belongs inside the shared platform. Product-specific features, domain workflows, and channel-specific experiences often stay outside the platform while consuming its services through defined interfaces. That boundary should be visible in the model because it protects both platform coherence and domain autonomy. If too much domain logic is absorbed into the platform, the platform becomes slow and unwieldy. If too little is shared, teams end up rebuilding the same capabilities independently.
A realistic example is an insurance enterprise with separate claims, policy, and broker channels. The shared platform may provide authentication, document notification, payment initiation, and event distribution. The claims adjudication rules, however, remain in the claims domain because they reflect product-specific business logic and regulatory interpretation. In the model, the claims application consumes platform services but does not become part of the platform itself. That distinction avoids a common mistake: turning the platform team into the owner of every cross-domain process.
Non-functional concerns also shape the application structure. Versioning, throttling, auditability, observability, and contract management are not secondary details. They are part of what makes a service consumable at enterprise scale. An External Partner API Service, for example, is not really viable unless it is supported by gateway policies, developer onboarding, usage analytics, and lifecycle controls. In the same way, an internal event service is only reusable if event schemas, ownership, and subscription rules are governed.
This application view becomes especially valuable for impact analysis and planning. It shows which products depend on which shared services, which components are central points of failure or change, and where standardization or decoupling would have the greatest effect. In that sense, the application layer forms the bridge between the business rationale established earlier and the technology foundation described next.
Technology Layer View: Infrastructure, Cloud Foundations, and Deployment Patterns
If the application layer shows what the platform provides, the technology layer shows what makes those services reliable, secure, and scalable in production. A platform is not defined only by functional reuse. It also depends on non-functional strength. The technology layer is where that strength becomes visible.
A useful way to structure this view is by foundational technology domains rather than by vendor products. Common domains include cloud foundation services, container runtime platforms, network and connectivity services, data storage platforms, event infrastructure, security services, and operational management tooling. Modeling these as technology services and infrastructure elements keeps the architecture stable even when specific tools change.
In many enterprises, the platform depends on a cloud foundation that provides standardized deployment environments. This may include network segmentation, ingress and egress control, secrets management, key management, policy enforcement, centralized logging, backup services, and identity federation. These should not be treated as invisible background details. They are part of what turns shared application services into enterprise-grade platform services.
Deployment patterns matter just as much. A digital platform may combine containerized services, serverless functions, managed platform services, and packaged software. ArchiMate can show which application components are deployed on which nodes and supported by which system software. Customer-facing APIs may run on a Kubernetes cluster, event processing may run on a managed streaming platform, and analytics workloads may run in a separate data processing environment. Those distinctions matter because they affect resilience, ownership, and scaling behavior.
As with the business and application layers, boundaries are critical. One key decision is how to separate shared runtime services from team-specific workloads. Some organizations centralize almost everything. Others provide governed self-service environments in which teams deploy independently within approved constraints. The model should make that distinction visible, because it shows where standardization is required and where controlled autonomy is possible.
Resilience patterns should also be explicit. High availability, load balancing, failover arrangements, message durability, backup, and disaster recovery are not optional details in a digital platform. If many products depend on shared identity, integration, or event services, failures in those components create enterprise-wide risk. Modeling those dependencies supports better investment decisions around redundancy and operational testing.
A telecommunications provider offers a useful micro-example. Its customer self-service app, retail point-of-sale solution, and partner activation channel all depend on a shared identity platform and event backbone. The applications themselves may be distributed across different runtime environments, but the identity service runs active-active across two regions, while the event platform uses replicated brokers and durable topics. In the ArchiMate model, that deployment pattern is not operational trivia; it explains how customer activation remains available during a regional failure.
Security architecture belongs here as well. Network segmentation, certificate management, privileged access controls, runtime threat detection, and encryption services often underpin every platform capability. Showing these as part of the technology fabric reinforces a key point: security and governance are embedded in the platform, not reimplemented separately by every consuming team.
This technology view completes the structural picture started in the business and application layers. It shows that platform scalability is not achieved through application design alone. It depends on deliberate infrastructure architecture that standardizes environments, supports automation, and reduces operational friction across the enterprise.
Cross-Layer Relationships: Traceability from Strategy to Operations
The earlier sections described the platform one layer at a time. The real strength of ArchiMate, however, is its ability to connect those layers into a single traceable architecture. This is where the model becomes most useful for enterprise decision-making.
At the top of the chain are drivers, goals, outcomes, and principles. An enterprise may have a driver to grow digital revenue, a goal to reduce partner onboarding time, and a principle that new digital capabilities should be exposed through governed APIs. Those strategic elements should connect directly to the business capabilities and value streams described earlier, such as Partner Onboarding, Digital Product Management, or Deliver Digital Service.
The next step is to trace those business needs into the application services that enable them. If reducing partner onboarding time is a business goal, the model should show which services contribute to it: Identity and Access Service, API Gateway Service, Consent Management Service, Developer Portal Service, and Workflow Orchestration Service. Each of those services is then realized by specific application components.
From there, the trace continues into the technology layer. The relevant components are deployed on runtime environments, secured by infrastructure controls, and supported by operational tooling. In other words, a strategic outcome can ultimately be connected to specific infrastructure and operational capabilities. A goal of reliable customer access, for example, may depend on identity services, which in turn depend on load balancing, secrets management, observability, and incident response.
This traceability is especially useful for impact analysis. If the enterprise plans to replace an identity provider, introduce a new event backbone, or impose stricter data residency controls, the architect can assess not only the technical consequences but the business and strategic ones as well. Which value streams are affected? Which stakeholders experience disruption? Which strategic commitments are put at risk? Without cross-layer traceability, those questions are often answered informally and too late.
Traceability also supports governance and funding. Shared platform work can be difficult to justify because its benefits are distributed. A cross-layer model makes those benefits visible. It shows that investments in observability, API management, or security controls are not isolated infrastructure improvements; they directly support product speed, compliance, ecosystem growth, and service reliability.
In practice, this is the point where the model stops being documentation and becomes an operating tool. It supports design reviews, roadmap sequencing, dependency analysis, and change planning. More importantly, it keeps strategy, delivery, and operations from drifting into separate conversations. The platform is understood instead as one integrated system of enterprise change.
Governance, Roadmapping, and Best Practices
Because a digital platform is a long-lived enterprise asset, the model needs to support governance and evolution, not just description. The earlier sections established what the platform is, why it exists, and how it is structured. This section turns to how that coherence is maintained as adoption grows.
A first governance principle is to make ownership explicit. Shared services often deteriorate when accountability is unclear. An API gateway, event backbone, identity service, or shared data product may be widely used, but unless someone owns lifecycle management, policy enforcement, and service quality, the platform becomes fragmented. In ArchiMate, it is useful to model not only the technical elements but also the responsible roles, such as Platform Product Owner, Security Architect, Data Governance Lead, or Service Operations Team.
Roadmapping is just as important because platforms are rarely delivered in a single step. A practical roadmap often begins with foundational capabilities such as identity, API management, observability, and cloud governance. From there it expands into event-driven integration, shared analytics, developer self-service, and partner enablement. As the cross-layer section showed, these capabilities are not independent. Some are prerequisites for others. External API exposure, for example, may depend on prior investment in identity federation, throttling, monitoring, and support processes.
A useful planning practice is to distinguish platform essentials from adoption-dependent enhancements. Not every desirable capability needs to be built immediately. Some become valuable only when enough products or domains are ready to consume them. The model should help identify which capabilities are foundational for control and reuse, and which should be introduced later when demand and maturity justify them. That keeps the platform from becoming overengineered.
The model should also support conformance and exception management. In large enterprises, some teams will need to diverge from preferred platform patterns for valid reasons such as regulation, latency, or legacy constraints. Good governance does not eliminate variation; it makes variation visible and manageable. ArchiMate can show where a solution aligns with shared services, where it bypasses them, and what compensating controls are needed. A typical architecture board decision might approve Kafka as the default event backbone, while allowing a regulated business unit to retain managed file transfer temporarily under a time-bound exception.
Metrics and feedback loops are another important best practice. Structural architecture alone does not show whether the platform is working. Adoption rates, onboarding time, service reliability, API reuse, policy violations, and operational incidents provide that feedback. While ArchiMate is not a monitoring tool, it can show the relationships to which those measures apply. That makes governance conversations more evidence-based.
Technology lifecycle governance should be visible as well. Shared platforms accumulate risk when obsolete tools remain embedded in critical services. For example, the enterprise may set a policy that API gateways and IAM components must stay within vendor-supported versions, with quarterly review of technologies marked tolerate, invest, migrate, or retire. That turns lifecycle management into an architectural discipline rather than an afterthought.
Finally, the model should remain stable in structure but flexible in detail. The core service boundaries, ownership concepts, and cross-layer dependencies should remain understandable even as products, vendors, and deployment patterns change. That is the mark of a useful enterprise architecture model: it supports decisions over time rather than simply documenting a single moment in the current state.
Conclusion
A well-structured ArchiMate model of a digital platform does more than describe modern technology. It gives the enterprise a way to reason about reuse, control, speed, and change as parts of the same architectural problem. By linking strategy, business capabilities, application services, and technology foundations, the model provides a shared view of how digital delivery is enabled at scale.
The central idea running through this article is consistency across layers. The business layer defines why the platform exists and what should be shared. The application layer shows how reusable services are exposed and consumed. The technology layer shows how those services are made secure, resilient, and operable. Cross-layer traceability then ties the whole structure back to strategic goals and operational realities.
That is why ArchiMate is especially effective for digital platform architecture. It does not just show components; it shows relationships, dependencies, and intent. That makes it useful for design governance, investment planning, roadmap development, and impact assessment. It also helps enterprises manage one of the hardest platform questions: how to balance central standardization with domain autonomy.
Ultimately, a digital platform should be treated as an evolving operating capability, not a fixed target state. As products, channels, and ecosystem demands change, the platform model should be revisited to test whether service boundaries, ownership, and supporting technology still align with business value. Used that way, an ArchiMate digital platform architecture example becomes more than documentation. It becomes a practical tool for shaping how the enterprise scales digital delivery with coherence and intent.
Frequently Asked Questions
What is enterprise architecture?
Enterprise architecture is a discipline that aligns an organisation's strategy, business operations, information systems, and technology infrastructure. It provides a structured framework for understanding how an enterprise works today, where it needs to go, and how to manage the transition.
How is ArchiMate used in enterprise architecture practice?
ArchiMate is used as the standard modeling language in enterprise architecture practice. It enables architects to create consistent, layered models covering business capabilities, application services, data flows, and technology infrastructure — all traceable from strategic goals to implementation.
What tools are used for enterprise architecture modeling?
Common enterprise architecture modeling tools include Sparx Enterprise Architect (Sparx EA), Archi, BiZZdesign Enterprise Studio, LeanIX, and Orbus iServer. Sparx EA is widely used for its ArchiMate, UML, BPMN and SysML support combined with powerful automation and scripting capabilities.