⏱ 25 min read
Organizing Application Landscape Models in Sparx EA for a Telco Client Sparx EA training
Learn how to organize application landscape models in Sparx Enterprise Architect for a telecommunications client, including repository structure, modeling governance, traceability, and scalable architecture documentation practices. Sparx EA best practices
Sparx EA, Sparx Enterprise Architect, application landscape modeling, telco architecture, telecommunications enterprise architecture, application portfolio management, architecture repository, EA modeling standards, enterprise architecture governance, solution architecture documentation, application landscape, architecture traceability, repository organization, ArchiMate, telco IT landscape
Introduction
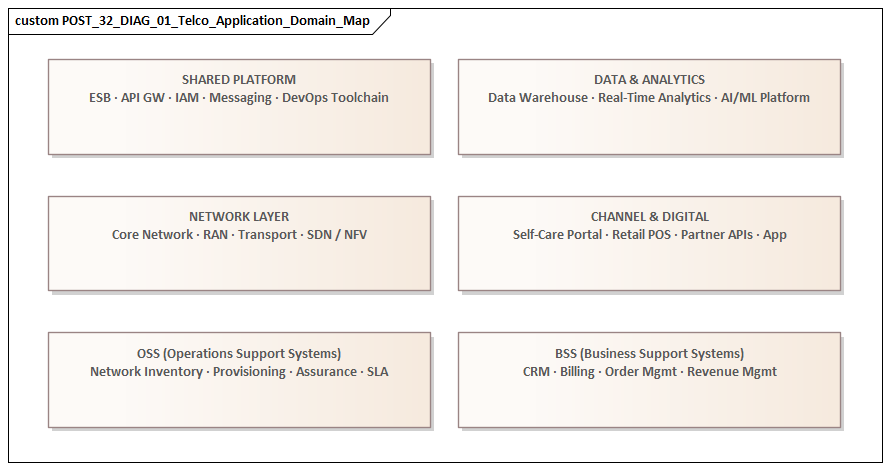
In a telecommunications provider, the application landscape is more than a system inventory. It is the operating map for how the business sells, fulfills, bills, supports, and evolves services. Customer channels, CRM, product catalog, order orchestration, activation, billing, charging, OSS, data platforms, and enterprise support systems all contribute to end-to-end value delivery. Because these chains cross commercial, operational, and technical boundaries, the quality of the model matters as much as the decision to model the estate in the first place.
That makes repository design in Sparx Enterprise Architect (EA) an architectural concern, not an administrative one. If applications are named inconsistently, duplicated in different packages, or connected through vague relationship types, confidence in the repository falls quickly. Teams may still produce diagrams, but the diagrams no longer support shared understanding. In a telco environment, the effect is immediate: delivery dependencies are missed, modernization plans understate transition complexity, and governance decisions rely on partial or conflicting views of the estate. It is not unusual, for example, for a design authority to approve a CRM enhancement as an apparently local change, only to discover later that product catalog, identity, and billing dependencies were modeled differently by separate teams.
A useful telco application landscape must serve several audiences at once. Executives need a view of strategic platforms, concentrated risk, and investment hotspots. Domain and solution architects need to understand application roles, dependencies, ownership, and lifecycle state. Delivery teams need traceability from business capability to application and interface. Operational stakeholders need visibility into criticality, resilience, and vendor exposure. Sparx EA becomes genuinely valuable when it can hold these concerns together through a single set of canonical elements rather than through disconnected project diagrams. Sparx EA guide
The practical challenge is balance. A repository with too little control becomes fragmented. One with too much control is bypassed because teams see it as detached from delivery. The most effective pattern is usually a domain-oriented structure supported by a small set of mandatory conventions: clear scope, stable taxonomy, canonical application elements, defined relationship types, and lightweight governance. In a telco setting, that normally means capturing metadata such as business domain, owner, lifecycle status, deployment model, architectural role, and key capability links.
The model must also reflect the reality of transformation rather than an idealized steady state. Telcos routinely operate legacy BSS and OSS platforms alongside newer digital, API-based, cloud, and event-driven components for years. Coexistence, migration bridges, duplicated capabilities, and phased retirement are normal conditions. A well-organized EA repository therefore needs to represent baseline, transition, and target states without collapsing them into a single blurred picture.
This article follows that line of thought. It begins with the telco architecture objectives for the landscape, then sets out scope, taxonomy, and modeling principles. From there, it describes repository structure, the treatment of core domains and relationships, the use of diagrams and traceability for governance, the role of ownership and lifecycle control, and the way the model can support reporting and roadmapping at scale. The aim is straightforward: to turn Sparx EA from a diagram store into a trusted architecture knowledge base for managing application complexity in a telecommunications enterprise. free Sparx EA maturity assessment
1. Telco Context and Enterprise Architecture Objectives
A telecommunications enterprise works under two constant pressures. It needs commercial speed to launch new offers, bundles, partner propositions, and digital experiences, yet many of the supporting application chains remain constrained by legacy platforms, regulatory obligations, and dependencies on network-facing systems. For enterprise architecture, that means the application landscape must provide end-to-end visibility, not just a collection of domain inventories.
In most telcos, the estate spans several tightly connected areas: customer and partner channels, CRM and case management, product catalog and configuration, order management and fulfillment, billing and charging, mediation, identity and access management, enterprise data platforms, and OSS applications for inventory, activation, assurance, and network operations. These areas do not function in isolation. A single customer journey may pass through channel applications, product systems, order orchestration, fulfillment engines, billing setup, notification services, and network activation. If the landscape is modeled as a set of separate system lists, the enterprise loses sight of how value is actually delivered.
The first architectural objective is decision support. The model should help answer recurring questions such as:
- Which applications are systems of record?
- Where are the orchestration points?
- Which domains contain duplicated functionality?
- Which dependencies slow product launch or increase change risk?
- Which legacy systems remain in critical paths?
- Where are ownership and accountability fragmented?
A second objective is to make operational criticality visible. In a telco, many applications directly affect revenue, customer service continuity, or regulatory obligations. A failure in activation, charging, or service assurance can have immediate business impact. The model therefore needs to distinguish technical complexity, business importance, and operational criticality rather than reducing them all to a single notion of an “important system.”
A third objective is transformation planning. Telco programs rarely move cleanly from current state to target state. More often, they involve coexistence, staged migration, temporary interfaces, duplicate process logic, and delayed retirement of legacy platforms. The application landscape has to support transition architecture, not just target architecture. This becomes particularly important in areas such as IAM modernization, where a telco may run a legacy customer identity store alongside a new centralized IAM platform until channels, CRM, and self-service journeys have been migrated.
A fourth objective is accountability. In large providers, responsibility is often split across business units, technology towers, managed service providers, and vendors. If ownership is unclear, governance slows and rationalization becomes difficult. The repository therefore needs to show who funds, governs, supports, and changes each application.
A simple micro-example illustrates the point. A mobile operator may treat “Order Management” as one domain in governance discussions, yet the actual order chain could include a digital capture layer, a legacy decomposition engine, a separate fulfillment orchestrator, and OSS activation adapters maintained by different teams. Without a model that makes those roles and dependencies explicit, a product launch delay is often attributed to “the order stack” when the real bottleneck sits in one handoff between BSS and OSS.
Taken together, these objectives define the role of the application landscape in Sparx EA. It is not documentation for its own sake; it is a navigable operating model for change. fixing Sparx EA performance problems
2. Defining Scope, Taxonomy, and Modeling Principles in Sparx EA
Consistency begins with a small number of explicit choices. The first is scope. Before architects define packages or diagrams, they need a clear statement of what the application landscape includes and what it does not.
For a telco repository, the core application landscape should represent:
- Deployable application assets
- Their business purpose
- Their domain placement
- Their key dependencies
- The minimum metadata needed for governance and analysis
Related viewpoints such as business capabilities, processes, data entities, technology platforms, and infrastructure should be linked to the application model, but they should not be confused with application elements themselves. If that distinction is not made early, one team will model “Billing” as an application, another as a capability, and a third as a process area. Repository quality then starts to erode almost immediately.
The next decision is taxonomy. For telco clients, the most effective approach is usually a domain-based taxonomy aligned to operational and commercial value streams. Typical top-level domains include:
- Channel and Digital Experience
- Customer Management
- Product and Offer Management
- Order Management and Fulfillment
- Billing and Charging
- Partner and Wholesale
- Network and Service Operations
- Enterprise Support
- Data and Analytics
- Integration Platforms
- Identity and Access Management
At the top level, simplicity matters. The purpose of the taxonomy is navigation, ownership, and reporting. Subdomains can be introduced where useful, but the top-level structure should remain stable over time.
Within that taxonomy, applications should also carry an architectural role. A channel front end, system of record, orchestration engine, integration hub, and reporting platform may all sit within the same broad domain, but they serve very different functions in the operating model. Capturing that role explicitly—through stereotypes, tagged values, or controlled attributes—makes filtered views and impact analysis far more effective.
Modeling principles should then define how elements are created and related. The strongest principle is simple:
Model once, view many times.
Each application should exist as a single canonical element in the repository and be reused across diagrams. Delivery teams should not create local copies for project convenience. Names should be recognizable and stable, using the commonly accepted product or platform name, with qualifiers added only where needed for geography, brand, or instance.
Relationship types also need control. A service call, event exchange, batch feed, orchestration dependency, and shared-data dependency are not interchangeable. If they are modeled inconsistently, the repository may look detailed while remaining analytically weak.
A final principle is to separate current-state fact from roadmap intent. Baseline, transition, and target relationships should not be mixed casually. They can be separated through package structure, diagram conventions, status attributes, or dedicated viewpoints, but the distinction must remain visible. In telco transformation, where coexistence and staged migration are standard conditions, this is essential.
Consider a realistic example from prepaid charging. A provider may introduce a new digital offer engine while still relying on a legacy charging platform for balance management and rating. If the repository shows only a neat target-state dependency from digital channels to the new platform, architects miss the transitional reality: the offer engine may still call the old charging stack for eligibility checks and voucher handling. Scope and relationship discipline are what keep those uncomfortable but important truths visible.
If scope, taxonomy, and principles are clear, the repository can be structured in a way that remains usable under delivery pressure.
3. Structuring the Repository: Packages, Views, Layers, and Naming Standards
Once scope and taxonomy are defined, they need to be translated into a repository structure that people can actually navigate. In Sparx EA, this is where many modeling efforts begin to drift: the conceptual model may be sound, but the package tree becomes cluttered, ownership is unclear, and teams no longer know where new content belongs.
A practical structure separates canonical layers from consumable views.
3.1 Canonical layers
Canonical layers hold the authoritative elements: applications, application services, interfaces, business capabilities, information objects, and technology platforms. These should sit in controlled packages and act as the source of truth.
For a telco client, the application branch is usually best organized by business domain. For example:
- Channel and Digital Experience
- Customer Management
- Product and Offer Management
- Order Management and Fulfillment
- Billing and Charging
- Partner and Wholesale
- Network and Service Operations
- Enterprise Support
- Data and Analytics
- Integration Platforms
- Identity and Access Management
Within each domain, a consistent substructure improves usability. A simple pattern is:
- Applications
- Application Services
- Interfaces
- Diagrams
That makes it immediately clear where canonical elements belong and where supporting diagrams should sit.
3.2 Cross-domain views
A separate top-level branch should hold cross-domain views. This is where enterprise maps, end-to-end journey views, transformation landscapes, and governance dashboards are assembled. As noted earlier, the same canonical application should appear in multiple views without being recreated.
Keeping these views separate prevents domain packages from filling up with short-lived project diagrams. It also preserves a distinction between repository fact and presentation artifact.
3.3 Layers inside the model
Many telco repositories also benefit from visual or analytical layering across applications, for example:
- Business-facing channels
- Process and orchestration platforms
- Systems of record
- Integration components
- Data-serving and reporting platforms
This does not need to become a rigid metamodel, but it helps reveal where control sits and where complexity accumulates. During transformation planning, the key question is often not only what connects to what, but which layer will absorb complexity during transition. An architecture board may, for instance, decide that a new orchestration layer should shield billing and OSS from repeated channel-specific change.
3.4 Naming standards
Naming should optimize searchability and recognition, not formalism. Application names should be stable and easily recognized by the business. If there are multiple instances by country, brand, or deployment model, those distinctions should be explicit and handled consistently.
Diagram names should also follow a predictable pattern, such as:
[Domain] – [Viewpoint] – [State]
Examples:
- Billing and Charging – Domain Landscape – Current State
- Order Management – Integration View – Transition State
- CRM – Capability Support Map – Target State
This basic discipline makes review and reuse much easier.
3.5 Ownership in the structure
Repository structure is also a form of governance. Packages should have clear custodians, and canonical elements should not be edited without control. When package ownership is visible and reuse is straightforward, the repository stays coherent. When it is not, the structure gradually starts to mirror organizational confusion rather than architectural intent.
A small but telling example comes from multi-brand telcos. It is common to find separate diagrams for consumer, SME, and wholesale channels, each containing what appears to be its own “Customer Profile” application. In reality, those may all point to the same CRM platform, with only brand-specific front ends differing. A repository structure that enforces canonical applications in domain packages prevents the landscape from multiplying into near-duplicates.
With that structure in place, the next step is to model the substance of the telco estate.
4. Modeling Core Telco Application Domains, Capabilities, and System Relationships
The purpose of modeling is not to create a complete technical inventory. It is to represent the telco estate at the level needed for architecture decisions. That means showing how applications support business capabilities, where control points sit, and which dependencies matter most.
4.1 Core domains
Most telco landscapes consistently include the following domains:
- Digital Channels and Assisted Sales
- Customer Management
- Product and Offer Management
- Order Management
- Service Fulfillment and Activation
- Billing and Charging
- Partner and Wholesale Management
- Identity and Access Management
- Network and Service Operations
- Enterprise Support
- Data and Analytics
- Integration Platforms
These should be treated as meaningful architectural groupings, not merely as folders. They help explain where responsibility sits, where complexity builds up, and where cross-domain dependencies are strongest.
4.2 Linking applications to capabilities
Applications should be linked to business capabilities, but selectively. The objective is not to model every minor function. It is to show where key capabilities depend on specific systems or on fragmented landscapes.
Examples include:
- Manage Customer Account
- Configure Product and Offer
- Capture Order
- Fulfill Service Order
- Activate Service
- Bill Customer
- Authenticate Customer
- Resolve Service Fault
- Manage Partner Settlement
Capability mapping helps answer questions such as:
- Which capabilities depend on legacy systems?
- Which capabilities are supported by too many applications?
- Where is functionality duplicated across brands or domains?
- Which systems are critical for a high-priority transformation?
Used well, capability mapping exposes structural issues that are easy to miss in integration diagrams. A “Manage Customer Account” capability supported by five applications across retail, care, billing, and self-service channels is a governance problem even if the interfaces between those systems are technically stable.
4.3 Modeling relationship types
In a telco landscape, “connected to” is too vague to be useful. Dependencies should be classified according to their role. At minimum, it is useful to distinguish between:
- Service consumption
- Event exchange
- Batch data movement
- Orchestration or control dependency
- Shared data dependency
This improves impact analysis because the effort and risk associated with each relationship type differ. Replacing a nightly batch feed is a different challenge from replacing a synchronous orchestration dependency in the order chain. Likewise, an event architecture built on Kafka may decouple order status publication from downstream consumers, but it still introduces governance questions around event ownership, schema evolution, and replay handling.
4.4 Representing architectural roles within domains
Applications within a domain should not appear as a flat list. Their architectural role matters. In Billing and Charging, the rating engine, billing engine, mediation platform, collections solution, and invoice presentment tool each play a different part in the revenue chain. In OSS, inventory, activation, fault management, and assurance platforms often form tightly coupled operational sequences. In IAM, customer authentication, workforce identity, access governance, and privileged access management should likewise be distinguished rather than collapsed into one generic “security” box.
Modeling these distinctions helps architects identify domain control points, duplicated logic, and overloaded integration paths.
4.5 Focusing on cross-domain dependencies
Cross-domain relationships often carry the highest transformation risk. Product, order, billing, identity, and network-support domains are usually governed by different teams, yet they depend heavily on one another. The repository should make these handoffs visible, especially where one domain acts as trigger, translator, or bottleneck for another.
A realistic micro-example is fiber provisioning. A customer order captured in a digital channel may be validated against product catalog rules, decomposed in order management, then handed to a fulfillment layer that checks service inventory and triggers network activation. If the repository models only the digital and BSS side, transformation plans may overlook the OSS dependency that actually dictates lead time and failure handling. In practice, many “simple” product launches stall not in the channel or catalog but in the activation chain behind them.
For governance and roadmap planning, this level of modeling is usually more valuable than documenting every internal integration within a single stack. The critical issue is where domain boundaries create delivery friction or operational fragility.
Modeled at this level, the landscape shows not just what exists, but how the telco operates and where change is hardest.
5. Using Sparx EA Diagrams, Matrices, and Traceability to Support Analysis and Governance
Once the core elements and relationships are in place, Sparx EA becomes valuable as an analysis platform rather than simply a modeling tool. Diagrams, matrices, and traceability each contribute something different. multi-team Sparx EA collaboration
5.1 Diagrams as decision views
Diagrams still matter, but each one should answer a specific question.
Examples include:
- Domain landscape diagrams for showing major applications and control points within Billing, Order Management, or OSS
- End-to-end value stream views for exposing cross-domain dependencies in journeys such as lead-to-cash or trouble-to-resolve
- Transition diagrams for showing coexistence between legacy and strategic platforms during modernization
- Capability support views for showing which applications realize critical business capabilities
A diagram should not try to serve as inventory, integration map, target vision, and migration plan all at once. When it does, it becomes visually dense and analytically weak.
5.2 Matrices for structural analysis
Matrices are particularly powerful in telco environments because they reveal patterns that diagrams often hide.
Useful examples include:
- Application-to-capability matrix: shows capability fragmentation or duplication
- Application-to-application matrix: shows dependency concentration around orchestration points or hubs
- Application-to-owner matrix: exposes fragmented accountability
- Application-to-vendor matrix: highlights supplier concentration risk
- Application-to-lifecycle matrix: shows how much of a domain remains dependent on sunset systems
These views move the repository beyond visual storytelling and into repeatable analysis. An architecture board can use them to support decisions such as rejecting a proposal to add a new dependency to a sunset mediation platform or requiring reuse of a strategic IAM service instead of another local login store.
5.3 Traceability for impact assessment
Traceability is what turns the model into a governance asset. An application should be traceable, where relevant, to:
- The business capabilities it supports
- The interfaces it exposes or consumes
- The data entities it depends on
- The technology platforms it runs on
- The change initiatives affecting it
This is especially useful when assessing the blast radius of planned change. A change in product catalog logic, for example, may affect channels, order decomposition, billing setup, partner feeds, and reporting. Traceability helps expose those downstream effects before delivery is underway.
One practical example is invoice redesign. What looks like a billing presentation change may involve the billing engine, document composition platform, CRM contact preferences, payment collections, data warehouse extracts, and regulatory retention controls. Without traceability, these dependencies are discovered piecemeal through project delivery. With traceability, they are visible during planning.
As with capability mapping, traceability should be selective. The most useful traces are the ones that answer recurring governance questions:
- Which applications are affected by this initiative?
- Which capabilities depend on this platform?
- Which interfaces create release coordination risk?
- Which legacy components remain in critical paths?
5.4 Filtered views and searches
Tagged values, searches, and filtered views allow architects to create governance-focused slices of the landscape, such as:
- All end-of-life applications in a domain
- All production-critical applications without clear ownership
- All systems involved in a specific customer journey
- All applications dependent on a strategic integration platform
- All sunset systems still receiving new interfaces
These views are often more useful than static diagrams because they can be refreshed as the repository changes.
Used together, diagrams provide narrative, matrices provide structure, and traceability provides confidence. That combination makes the repository useful in design authority, investment review, risk assessment, and transformation planning.
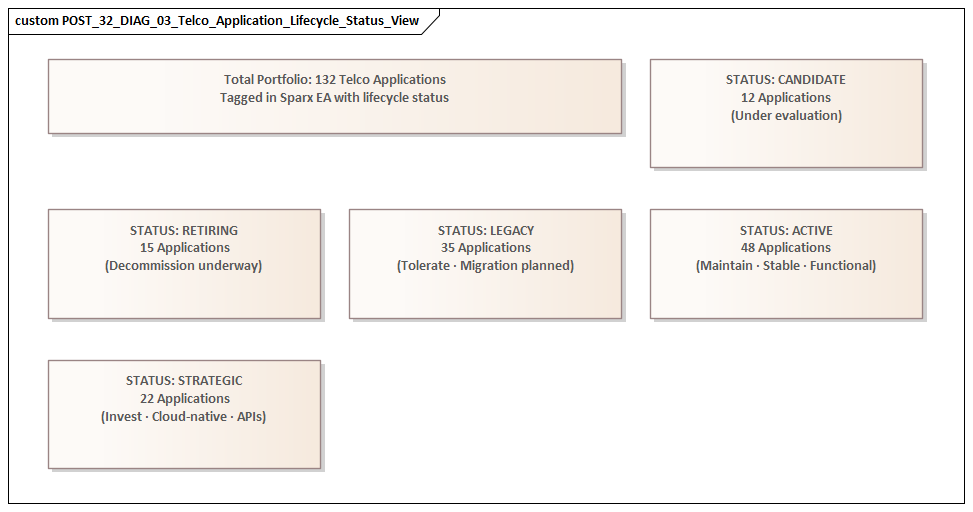
6. Establishing Ownership, Lifecycle Management, and Change Control
A model remains useful only as long as it remains trusted. In a telco environment, where the estate changes continuously, trust depends on ownership, lifecycle discipline, and proportionate change control.
6.1 Ownership at multiple levels
Ownership should be defined at several levels:
- Enterprise level: repository steward or architecture practice owner responsible for standards and coherence
- Domain level: architecture custodian for areas such as Billing, CRM, Order Management, OSS, IAM, or Data
- Application level: business owner, technology owner, operational support owner, and where relevant vendor or managed service provider
This layered model avoids a common failure mode: standards exist, but no one is clearly responsible for maintaining the content itself.
6.2 Lifecycle as meaningful governance data
Lifecycle should be modeled as first-class information, not optional metadata. For telcos, useful states often include:
- Proposed
- Active
- Strategic
- Contained
- Sunset
- Decommissioning
- Retired
These states are more useful than a simple current/target distinction because they reflect the transitional reality of the estate.
Lifecycle state should also have governance consequences. For example:
- Strategic applications should be preferred for new investment and onboarding
- Contained or Sunset applications should not receive new dependencies without exception approval
- Decommissioning applications should show replacement relationships and retirement milestones
This turns lifecycle from a descriptive label into a decision mechanism. A practical example is middleware governance: if an on-premises ESB is marked Sunset, new integrations may be directed to API management or event streaming instead, with exceptions reviewed explicitly.
6.3 Change control
Change control should be lightweight, but formal enough to protect trust. A practical model is to classify updates by impact:
- Minor changes: metadata updates such as owner or deployment detail; handled by domain custodians
- Structural changes: new canonical applications, domain reassignment, or major dependency changes; reviewed through architecture workflow
- High-impact changes: strategic platform changes, lifecycle changes, or cross-domain dependency shifts; aligned to portfolio or design governance forums
This allows the repository to stay current without becoming bureaucratic.
6.4 Embedding maintenance into delivery
Repository updates should be tied to delivery gates rather than left until project closure. Good update points include:
- Solution outline approval
- Interface design review
- Release readiness
- Production cutover
- Decommissioning sign-off
This ensures the model is updated while the information is still current and useful.
6.5 Quality control
Regular health checks should look for:
- Duplicate application elements
- Missing owners
- Outdated lifecycle states
- Orphaned interfaces
- Diagrams referencing obsolete elements
- Inconsistent naming or stereotypes
This is not clerical housekeeping. It is how the enterprise protects the credibility of the application landscape as a decision tool.
7. Scaling the Model for Reporting, Roadmapping, and Continuous Governance
Once the repository is structurally sound and properly governed, the next challenge is scale. A telco application landscape has to serve executives, architects, program leaders, and operational stakeholders without splitting into multiple versions of the truth.
7.1 Standard reporting outputs
Reporting views should be treated as governed products derived from canonical content. Rather than having each program create its own interpretation of the estate, the repository should support a standard set of outputs, such as:
- Enterprise application domain maps
- Strategic platform dashboards
- Lifecycle heatmaps
- Transformation overlap views
- Dependency concentration reports
- Sunset and decommissioning reports
Where possible, these should be generated from repository attributes and relationships rather than manually redrawn.
7.2 Linking the model to roadmaps
Telco transformation usually involves staged migration and coexistence. The repository should therefore link applications to roadmap constructs such as:
- Transition states
- Work packages
- Milestones
- Planned retirement dates
- Dependency sequences
This allows architects to show not only the current and target states, but also how the organization intends to move between them.
Examples might include:
- When a legacy order platform stops accepting new product types
- When charging logic is split between old and new stacks
- When OSS integration moves from point-to-point links to mediated APIs or event streams
- When regional CRM instances are consolidated into a strategic platform
- When customer authentication is migrated from brand-specific login stores to a central IAM platform
7.3 Exposing sequencing constraints
Roadmaps are useful only if they reflect real constraints. The repository should help expose:
- Product model dependencies
- Shared customer data dependencies
- Release freeze periods
- Vendor upgrade windows
- Temporary coexistence requirements
- Migration readiness of dependent systems
This is where relationship type, lifecycle state, criticality, and retirement metadata become especially valuable.
7.4 Supporting continuous governance
The repository should support recurring review cycles that answer consistent questions, for example:
- Which applications changed lifecycle state this quarter?
- Where have new cross-domain dependencies been introduced?
- Which strategic platforms are accumulating exceptions?
- Which sunset systems still attract new demand?
- Which domains remain heavily dependent on legacy integration patterns?
Used this way, Sparx EA becomes part of the governance cadence rather than a reference consulted only during major programs.
7.5 Controlled abstraction
Large repositories become difficult to use if every audience sees the same level of detail. The model therefore needs layered reporting:
- Executive level: domain maps, strategic platforms, risk and investment heatmaps
- Architecture working level: applications, interfaces, dependencies, and transition views
- Specialist level: deeper integration, resilience, operational, or data analysis
The objective is not to simplify the truth, but to present the right level of truth for each decision context.
If reporting is standardized, roadmaps are traceable to repository facts, and governance uses the model continuously, the application landscape becomes a durable management instrument for enterprise change.
Conclusion
Organizing an application landscape model in Sparx EA for a telco client is fundamentally about making complexity governable. The repository becomes valuable when it helps the enterprise move from fragmented system knowledge to a shared architectural frame for action.
The strongest approach starts with clear scope, a stable domain taxonomy, and a small set of modeling principles. Those principles then need to be carried into a repository structure that separates canonical elements from stakeholder views, models applications by business capability and architectural role, and uses controlled relationship types to make dependencies meaningful. From there, Sparx EA can support analysis through diagrams, matrices, traceability, and filtered views, provided the model is sustained through clear ownership, lifecycle discipline, and proportionate change control.
One theme runs through the article: a telco repository has to support both stability and transition. It must be stable enough to act as a trusted source of truth, yet flexible enough to represent coexistence, phased migration, and cross-domain transformation. That balance is what allows the model to support governance, impact analysis, modernization sequencing, and stakeholder reporting over time.
In practice, the most effective repositories are rarely the most elaborate. They are the ones people reuse, curate, and embed in real decision processes. When that happens, Sparx EA stops being a diagram store and becomes what it should be: a practical architecture knowledge base for steering the telco application estate toward a more coherent and manageable future.
Frequently Asked Questions
What is enterprise architecture?
Enterprise architecture is a discipline that aligns an organisation's strategy, business processes, information systems, and technology. It provides a structured approach to understanding the current state, defining the target state, and managing the transition — using frameworks like TOGAF and modeling languages like ArchiMate.
How does ArchiMate support enterprise transformation?
ArchiMate supports transformation by modeling baseline and target architectures across business, application, and technology layers. The Implementation and Migration layer enables architects to define transition plateaus, work packages, and migration events — creating a traceable roadmap from strategy through to implementation.
What tools are used for enterprise architecture modeling?
The most widely used tools are Sparx Enterprise Architect (ArchiMate, UML, BPMN, SysML), Archi (ArchiMate-only, free), and BiZZdesign Enterprise Studio. Sparx EA is the most feature-rich — supporting concurrent repositories, automated reporting, scripting, and integration with delivery tools like Jira and Azure DevOps.