⏱ 27 min read
ArchiMate Modeling Patterns for Enterprise Architects | Practical EA Guide ArchiMate training
Explore ArchiMate modeling patterns for enterprise architects, including practical techniques for structuring business, application, and technology architecture models with clarity and consistency. ArchiMate tutorial for enterprise architects
ArchiMate modeling patterns, enterprise architecture, enterprise architects, ArchiMate best practices, ArchiMate examples, architecture modeling, business architecture, application architecture, technology architecture, EA modeling techniques, ArchiMate framework, architecture design patterns ArchiMate layers explained
Introduction
ArchiMate remains widely adopted because it gives architects a structured way to describe how strategy, business operations, applications, data, and technology relate to one another. In practice, however, the difficulty is rarely the notation. Most architects become comfortable with the core elements and relationships reasonably quickly. The real challenge is producing models that remain consistent, useful, and repeatable across teams, programs, and governance cycles. ArchiMate relationship types
That is where modeling patterns earn their keep. A modeling pattern is a reusable way of organizing architectural content around a recurring concern. Instead of rebuilding each model from first principles, architects can apply proven arrangements of elements, relationships, and viewpoints that make intent explicit and reduce interpretation drift. These patterns help answer familiar questions: how should a capability connect to processes and applications? How should a transformation roadmap be shown without forcing every dependency onto one diagram? How should service exposure, ownership, and dependency be represented across domains?
As repositories expand, the need for patterns becomes more pronounced. Large enterprises do not depend on one architect producing one model. They rely on multiple teams working across business units, platforms, portfolios, and change initiatives. Without shared patterns, ArchiMate views quickly diverge in both structure and meaning. Similar situations end up modeled at different levels of detail or with different relationship choices, which makes comparison difficult and governance weaker. Patterns introduce standardization without reducing every model to a rigid template. They create enough discipline for coherence while still leaving room for context. ArchiMate modeling best practices
Patterns also make architecture more useful in day-to-day decision-making. Enterprise architecture is not produced for its own sake. It supports planning, investment decisions, solution design, risk management, and change execution. A sound pattern can expose dependencies early, reveal duplication, and show where strategic intent is not backed by operational or technical reality. That matters in application rationalization, capability-based planning, platform modernization, and post-merger integration, where stakeholders need concise but dependable views of a complex landscape.
They also provide a practical bridge between conceptual architecture and implementation discussions. Executives may want a capability-to-value-stream view. Portfolio managers may need a roadmap view. Delivery teams may need a service-to-application dependency model. Patterns make it possible to tailor views to those audiences while preserving traceability across the repository.
The sections that follow present a set of practical ArchiMate modeling patterns for enterprise architects. They begin with the principles that make patterns effective, then move through cross-layer traceability, strategy realization, application and integration design, technology and deployment, and finally governance and adoption. Taken together, these patterns show how ArchiMate can be used not only to describe an enterprise, but to support decisions about how it should change.
1. Foundations of ArchiMate Modeling Patterns
Before applying specific patterns, it helps to be clear about why they matter. A modeling pattern is more than a diagram layout or a preferred visual style. It is a repeatable structuring choice that combines scope, abstraction, relationship logic, and stakeholder intent. In practice, patterns help architects make consistent decisions about what to include, what to omit, and how to connect concepts so that a model supports analysis as well as communication.
The first principle is straightforward: patterns should be driven by architectural questions, not by notation. Many weak ArchiMate models are technically valid but practically unhelpful because they begin with available element types rather than the decision the model is supposed to support. The architect should start by asking what question the view needs to answer. Is the concern strategic alignment, operational dependency, technology risk, ownership, transition planning, or investment impact? The pattern should follow from that purpose. A model built to assess capability enablement will not be structured in the same way as one intended to show application integration exposure, even if both use some of the same concepts. An architecture board reviewing a customer onboarding initiative, for instance, may need a capability, risk, and transition-state view rather than a detailed interface model.
The second principle is disciplined abstraction. ArchiMate allows relationships across strategy, business, application, and technology layers, but that flexibility can easily produce views that mix levels of detail in confusing ways. Effective patterns set a clear abstraction boundary. A capability view should not suddenly drop into interface-level application components unless that detail is central to the purpose of the view. By the same logic, a technology dependency model should not be crowded with motivation elements unless they materially affect the analysis. Good patterns preserve coherence by controlling granularity.
The third principle is semantic consistency. Patterns only work when teams share a stable interpretation of elements and relationships. If one group uses business services to represent internal process outcomes while another uses them for externally consumed offerings, the repository quickly loses credibility. The same problem appears with relationships such as serving, realization, assignment, and access, which are often applied inconsistently. Useful patterns therefore depend on explicit conventions: what each element type means in the enterprise, when it should be used, and which relationships are acceptable between concepts.
The fourth principle is viewpoint design. Patterns are valuable because they can be reused for recurring stakeholder needs. That means defining not only the structure of the model, but also its intended audience, level of detail, and the decision it is meant to support. A portfolio governance pattern may consistently include capabilities, applications, lifecycle status, and strategic fit. A transformation planning pattern may include plateaus, gaps, and work packages. In both cases, the pattern has value because it supports a repeatable enterprise use case rather than a one-off presentation.
The final principle is to treat patterns as repository assets rather than isolated artifacts. Their value increases when they can be applied across domains, compared over time, and tied to governance processes. In mature practices, patterns become part of the architecture operating model. They influence how content is created, reviewed, reused, and consumed. That is the real foundation of ArchiMate modeling patterns: not visual consistency alone, but reliable architectural meaning at enterprise scale.
2. Layering and Cross-Layer Traceability Patterns
One of ArchiMate’s main strengths is its ability to connect strategic intent, business execution, applications, and technology without collapsing everything into a single overloaded view. The foundational principles matter most here. Abstraction has to remain controlled, and traceability needs to follow clear semantic rules. Layering patterns preserve the integrity of each domain, while cross-layer traceability patterns connect them in ways that support analysis.
A practical starting point is to treat each layer as its own analytical space. Strategy-oriented views may contain capabilities, value streams, outcomes, and courses of action. Business-layer views focus on processes, roles, services, and products. Application-layer views describe application services, components, and data objects. Technology-layer views cover infrastructure services, nodes, system software, and networks. The point is not just visual separation. It is conceptual clarity. Each view should answer a specific question well before it is connected to other layers.
In reality, enterprise decisions rarely stay within one layer. Leaders want to know which applications enable a capability. Portfolio managers want to understand which technology platforms create risk for critical business services. Transformation leaders need to trace work packages to the business outcomes they are supposed to deliver. This is where cross-layer traceability patterns become indispensable.
A common pattern is capability-to-process-to-application-to-technology. In this structure, a business capability is realized or supported by one or more business processes. Those processes use application services or are enabled by application components, and those applications are hosted on technology elements. This pattern is especially useful in impact analysis and modernization planning. If a platform is being retired, the architect can trace upward to the applications affected, the processes disrupted, and the capabilities put at risk. If a capability is being prioritized for improvement, the same pattern can be traced downward to identify the operational and technical constraints that stand in the way.
A familiar micro-example is IAM modernization. The Identity and Access Management capability traces to joiner-mover-leaver, authentication, and privileged access processes. Those processes depend on directory, federation, and access management services, which in turn rely on shared identity platforms and the infrastructure services hosting them. Once represented this way, a proposed platform change can be assessed in terms of process disruption, control impact, and business risk rather than infrastructure alone.
A second pattern is service cascading across layers. A business service may be supported by one or more application services, which in turn depend on technology services. This creates a service lineage that works well for resilience analysis, service ownership, and SLA discussions. It also avoids a common weakness in architecture repositories: linking applications directly to capabilities without showing the business-facing service context in between. By preserving the service chain, architects can explain how value is actually delivered.
Consider a retail bank’s “Card Dispute Handling” business service. It may be supported by case management and payment investigation application services, both of which depend on messaging, database, and identity technology services. If the messaging platform is unstable, the business impact can be traced through the application services to a customer-visible service, which makes the risk discussion far more concrete.
The key discipline here is selectivity. Cross-layer traceability does not mean drawing every possible relationship. If every business element is connected to every application and technology component, the model loses analytical value. A better approach is to define canonical trace routes. Capabilities may trace to business processes, for example, but not directly to infrastructure nodes except in specialized risk views. Technology elements may support applications, while business impact is inferred through the application and service chain. Conventions like these make models easier to compare and more dependable for analysis.
These patterns are particularly useful in governance. They support investment reviews by showing whether proposed technology changes contribute to priority capabilities. They support risk discussions by exposing concentrations of critical services on aging platforms. They support transformation planning by revealing where multiple initiatives act on the same dependencies. As later sections show, the same traceability logic underpins strategy realization, application integration analysis, and deployment governance.
3. Capability, Value Stream, and Strategy Realization Patterns
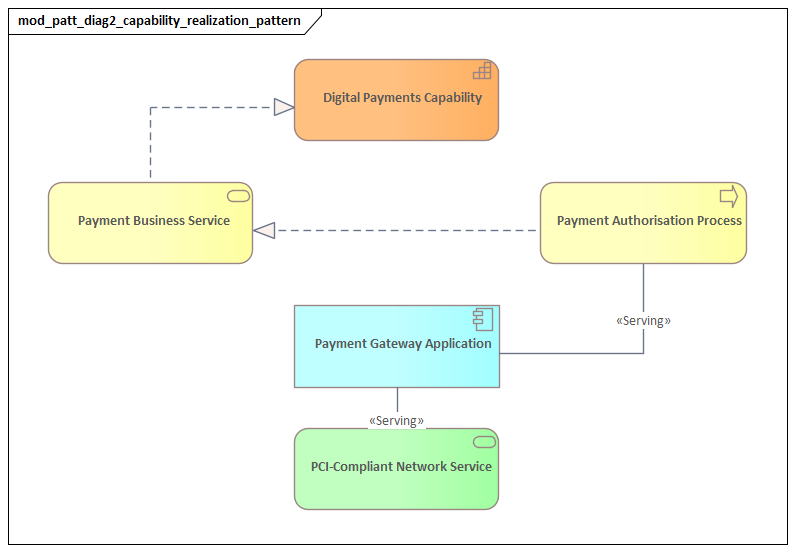
The traceability patterns described above become more powerful when applied to strategy. One of the recurring challenges in enterprise architecture is showing how strategic intent becomes operationally meaningful without reducing strategy to a list of projects or systems. ArchiMate is well suited to this because it allows architects to connect strategic constructs such as capabilities, outcomes, resources, and courses of action with the operational and technical structures that make them real.
A common pattern uses capability as the anchor of change. Capabilities represent what the enterprise needs to be able to do, independent of current organizational structures or application implementations. That makes them effective for strategic planning because they remain relatively stable even when processes, teams, or platforms change. In practice, architects often model strategic goals or outcomes as being supported by target capabilities, then connect those capabilities to the value streams in which they are exercised. The result is a structure in which strategy is expressed as required enterprise ability rather than abstract ambition.
Value streams add an essential dynamic. Capabilities show what the organization must possess; value streams show how value is created and realized from a stakeholder perspective. A useful pattern links value stream stages to the capabilities that enable them rather than treating the two as interchangeable. For example, Customer Onboarding may be modeled as a value stream with stages such as acquisition, verification, activation, and support, while capabilities such as identity management, product configuration, and case handling enable those stages. This helps stakeholders see not only which capabilities matter, but where in the value creation flow weaknesses or investment priorities appear.
A stronger realization pattern introduces courses of action and resources. If a capability is underperforming or strategically insufficient, the architect can model a course of action that addresses the gap, supported by resources such as funding, people, data, or technology assets. This avoids a simplistic direct line from strategy to project. Instead, the model shows that strategic realization depends on a chosen approach to change, backed by resources, and aimed at improving specific capabilities that influence value delivery.
Another effective structure is outcome-driven capability uplift. In this pattern, desired outcomes are associated with strategic goals. Those outcomes are enabled by improvements in selected capabilities, and the impact is observed in one or more value streams or business services. This creates a disciplined line of sight between investment and enterprise effect. Rather than claiming that a new platform “supports strategy,” the model shows which capability is being enhanced, what outcome is expected, and where stakeholder value should improve.
A realistic example is phased IAM modernization. An architecture board may approve the change not because “security needs improvement,” but because stronger identity capabilities are expected to reduce onboarding time, improve auditability, and enable passwordless access across digital channels. In the model, those outcomes can be linked to specific value stream stages such as verification and activation, then traced into the processes, application services, and platforms that must change.
Another example appears in a manufacturer pursuing predictive maintenance. The strategic outcome may be reduced unplanned downtime. That outcome depends on improving asset monitoring and analytics capabilities, which support value stream stages such as monitor, diagnose, and intervene. From there, the model can trace to condition-monitoring processes, IoT ingestion services, analytics applications, and the cloud data platform that underpins them. The strategy remains clear, but it no longer sits at arm’s length from implementation reality.
These patterns are useful in strategy execution and governance because they allow enterprise architects to challenge weak business cases that jump from ambition to solution without identifying the capability change required. They also support prioritization by showing when several initiatives are trying to improve the same capability, or when a strategically critical value stream depends on capabilities that are immature or fragmented.
As discussed in the previous section, this is where cross-layer traceability becomes more than a technical convenience. Once a target capability is identified, architects can trace downward into business processes, application services, and technology dependencies to understand what must actually change. The strategy model remains strategic, but it is no longer detached from execution.
4. Application, Integration, and Service Exposure Patterns
If strategy realization explains what must change, application architecture explains how digital enablement is structured to support that change. This section builds directly on the earlier ideas of layering and service lineage. Application models are most useful when they distinguish what an application does, how it is accessed, and how it interacts with other applications.
A core pattern is application component to application service to application interface. In this structure, the application component represents the logical or deployable system boundary, the application service represents the behavior it offers to consumers, and the application interface represents the access point through which that service is exposed. This pattern prevents architects from modeling integrations as vague lines between systems. Instead, one application component exposes a specific service through an interface, and another application or business process uses that service. The result is more precise and better suited to impact analysis, API governance, and platform planning.
A second important pattern is provider-consumer integration modeling. Rather than simply connecting two applications with a generic relationship, the architect identifies the provider application service, the consuming application component or business process, and the data objects exchanged where relevant. That makes the integration meaningful rather than merely visible. It allows stakeholders to ask practical questions about dependency, coupling, and information exchange without forcing every technical detail into a single view.
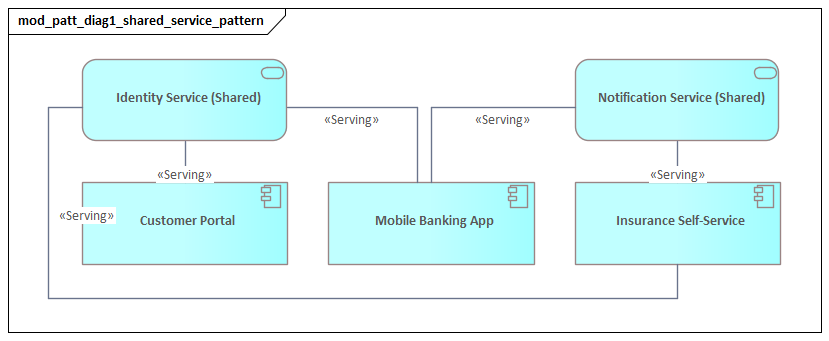
A third pattern is integration mediation through shared services or platforms. In large organizations, application landscapes often drift into point-to-point complexity, where each new solution creates another direct dependency. A cleaner ArchiMate structure introduces an integration service, application collaboration, or platform-centric application component that mediates exchange between producer and consumer systems. This works particularly well for representing API gateways, event hubs, enterprise service buses, or integration-platform-as-a-service environments. The analytical value is substantial: the pattern reveals where standardization reduces coupling, where integration has become concentrated in a strategic platform, and where that platform itself may represent a resilience or governance concern.
A useful micro-example is event-driven order processing. In an event architecture using Kafka, order, payment, and fulfillment applications can be shown as producers and consumers of event streams mediated by a shared event platform rather than as a web of direct integrations. That representation makes two things visible at once: reduced point-to-point coupling and increased dependency on the event platform as a shared operational asset.
Service exposure patterns also matter when separating internal enablement from externally visible digital products. Not every application service should be treated as business-facing. Some services exist only to support internal orchestration, data validation, identity management, or workflow execution. A strong pattern therefore distinguishes internal application services from those that directly support business services or digital channels. This matters because externally significant services often require stronger ownership, lifecycle management, SLA definition, and security controls than purely internal technical services.
An insurer’s quote platform provides a good example. A “Generate Quote” application service may directly support a broker portal and customer web channel, making it business-significant and externally visible in effect, even if not directly exposed to customers. By contrast, an internal “Rate Table Synchronization” service may be essential operationally but should not be modeled or governed in the same way. Treating both as equivalent service exposures obscures ownership and criticality.
These patterns are especially valuable in modernization and rationalization efforts. They help identify redundant service exposure, such as multiple systems offering overlapping customer profile or payment functions. They also reveal hidden fragility, for example where many business processes depend on a single legacy application service exposed through brittle interfaces. In cloud migration programs, the same patterns help architects show whether migration changes only the hosting location or also changes service contracts, integration style, and dependency structure.
As with the strategy patterns discussed earlier, the real value comes from traceability. An application service should not be modeled in isolation. It should connect upward to the business service or process it supports, and downward to the technology services on which it depends. That continuity makes the application layer a bridge between business intent and technical implementation rather than a standalone system inventory.
5. Technology, Infrastructure, and Deployment Patterns
Technology models are most useful when they do more than catalogue platforms, servers, and networks. Following the same principles established in the foundations section, they should be question-driven, semantically consistent, and held at a deliberate level of abstraction. Their purpose is to show how infrastructure supports applications, where deployment choices introduce risk or complexity, and how shared platforms shape enterprise resilience and control.
A foundational pattern is technology service to node to system software. In this structure, a technology service expresses what the infrastructure provides, such as compute hosting, container orchestration, database hosting, identity federation, or message transport. That service is realized by nodes and system software representing the runtime environment. This shifts the model away from device-centric thinking and toward service-centric infrastructure reasoning. Instead of showing only that an application runs on a server, the architect can show that it depends on a managed runtime or platform capability with specific operational characteristics.
A second useful pattern is deployment mapping across environments. Applications rarely exist in a single undifferentiated runtime context. They are deployed across development, test, staging, production, disaster recovery, edge, or region-specific environments, each with different controls and dependencies. ArchiMate deployment relationships can show how application components or artifacts are deployed onto nodes, while grouping and location concepts distinguish environment boundaries. This pattern is effective in governance because it reveals where deployment architectures are inconsistent, where critical systems lack resilient failover arrangements, or where environment sprawl is driving unnecessary cost.
Another important pattern is platform abstraction for shared infrastructure. In many organizations, solution teams model infrastructure as if each application owns its own stack. That quickly becomes misleading in modern enterprises where shared cloud landing zones, Kubernetes platforms, identity platforms, observability stacks, and managed data services support many workloads at once. A better pattern represents these as shared technology or platform services consumed by multiple applications. This makes concentration visible. It helps architects identify where standardization improves efficiency and where overreliance on a single platform creates systemic risk.
A practical example comes from container platform adoption. Instead of showing six customer-facing applications each deployed onto their own isolated runtime stack, the model may show them consuming a shared container orchestration service realized by a centrally managed Kubernetes platform. That single modeling choice changes the conversation. Governance can now assess platform resilience, patching obligations, tenancy boundaries, and operational ownership in one place rather than repeatedly at application level.
A further pattern concerns resilience and operational segmentation. Technology models are often weakest when they ignore availability zones, network domains, security boundaries, or recovery arrangements. ArchiMate can represent these concerns by separating nodes, communication networks, and locations into meaningful operational segments rather than flattening everything into one infrastructure view. For example, a customer-facing application may be deployed across multiple nodes in separate zones, depend on a shared identity service, and connect to a data platform in a protected network segment. Modeled at the right level, this helps architects assess whether critical business services are supported by genuinely resilient infrastructure or merely by duplicated components inside the same failure domain.
These patterns are highly relevant in cloud transformation, data center exit, zero-trust security programs, and operational risk reviews. They help distinguish superficial modernization from real architectural improvement. An application moved to cloud-hosted virtual machines may still carry the same fragility and recovery limitations as before. An application replatformed onto resilient managed services may materially change enterprise risk and agility.
This section also reinforces the cross-layer logic introduced earlier. Technology elements should not be linked upward indiscriminately. Their business significance is usually best understood through the application and service chains they support. That preserves abstraction while still allowing traceability from infrastructure choices to enterprise impact.
6. Governance, Viewpoint, and Repository Management Patterns
The previous sections describe patterns for modeling the enterprise. This section focuses on the patterns needed to sustain those models over time. ArchiMate becomes far more valuable when it is managed as part of an architecture operating model rather than as a collection of isolated diagrams. At enterprise scale, quality depends not only on notation skill, but also on governance, viewpoint discipline, and repository structure.
A core pattern is viewpoint standardization with purpose-based templates. Rather than allowing every architect to assemble views ad hoc, the architecture practice defines a set of repeatable viewpoints aligned to recurring decisions. Examples include an investment review viewpoint, a capability enablement viewpoint, an application dependency viewpoint, a transformation roadmap viewpoint, and a platform risk viewpoint. Each has a defined purpose, audience, element set, relationship set, and expected level of detail. This improves consistency without forcing every model into a single generic format.
A second pattern is separation of repository model from presentation view. In less mature practices, architects often create diagrams first and treat the diagram itself as the architecture asset. A stronger approach treats the repository as the primary source of truth and the diagram as a curated expression of that content. The practical benefit is considerable. The same underlying objects can support multiple views for different audiences without duplication or semantic drift. This directly reflects the repository-asset principle established in the foundations section.
Another useful pattern is object lifecycle governance. Repository quality declines quickly when concepts are added freely but rarely reviewed. Architecture teams should therefore define lifecycle states not only for applications and technologies, but also for model objects themselves. Elements may be proposed, validated, approved, in use, deprecated, or archived. This helps distinguish current-state fact from target-state design and prevents speculative content from being mistaken for approved architecture. The same logic applies to technology lifecycle governance: a database platform may be marked as tolerated, sunset, or prohibited, allowing governance teams to trace where exceptions still affect business-critical services.
Ownership and stewardship assignment is equally important. Repository objects should have clear accountability: who maintains the capability definition, who validates process relationships, who owns application metadata, and who approves technology standards. This can be modeled directly or managed through repository metadata, but the pattern matters because architecture content decays fastest where ownership is unclear. In large enterprises, federated stewardship often works best. Domain architects maintain local accuracy while central governance enforces common conventions.
Repository management also depends on controlled taxonomy and naming. Poor naming discipline undermines analysis faster than poor visual layout. If similar concepts are named inconsistently, duplicated across domains, or classified differently by different teams, reporting and traceability lose credibility. A mature pattern establishes canonical names, allowed aliases, domain tags, and reusable reference objects such as standard business capabilities, approved technology services, and enterprise platforms.
These governance patterns are what make the earlier modeling patterns scalable. Without them, cross-layer traceability becomes inconsistent, strategy realization models become hard to compare, and application or technology views drift into local interpretation. With them, ArchiMate supports repeatable reviews, trustworthy analysis, and a repository that can grow with the enterprise.
7. Common Pitfalls, Anti-Patterns, and Practical Adoption Guidance
The value of modeling patterns becomes clearest when architects encounter the ways modeling efforts fail. In many organizations, the issue is not a lack of notation knowledge but the emergence of anti-patterns that make models hard to use, hard to maintain, or easy to misread. Recognizing these pitfalls is essential if the patterns described earlier are to support decision-making rather than become another layer of documentation overhead.
One common anti-pattern is diagram-centric architecture. In this approach, teams focus on producing visually polished views for workshops or governance meetings without building a coherent underlying model. The immediate result may look persuasive, but the content often cannot be reused, queried, or traced across initiatives. Over time, each diagram becomes a standalone artifact with its own assumptions and terminology. The remedy, as discussed in the governance section, is to treat views as expressions of structured repository content rather than isolated deliverables.
A second pitfall is overmodeling. Because ArchiMate is expressive, teams sometimes try to capture every possible relationship, exception, and dependency in one repository, or even in one view. The result is technically rich but operationally unusable. Stakeholders cannot see what matters, and architects spend more time maintaining detail than supporting decisions. The earlier principle of disciplined abstraction is the corrective: model to the level required by the question being asked.
The opposite problem is shallow symbolic modeling. Here, architects use high-level ArchiMate elements as placeholders without enough semantic discipline to support analysis. Capabilities become generic labels, services are named inconsistently, and relationships are drawn because they seem approximately right. Such models may satisfy presentation needs, but they do not hold up in investment review, risk assessment, or transformation planning. This is why semantic consistency and naming conventions are not administrative details; they are prerequisites for trustworthy modeling.
Another frequent anti-pattern is tool-driven modeling behavior. Some teams model according to what their repository tool makes easy rather than what the enterprise actually needs to understand. If the tool favors certain object types, relationship shortcuts, or visualization styles, those conveniences can gradually define the architecture method. The practical lesson is simple: methods, metamodel constraints, and governance principles should shape tool configuration, not the reverse.
A further pitfall is isolated adoption within the architecture team. ArchiMate can struggle when it is treated as a specialist language used only by enterprise architects, disconnected from portfolio management, solution design, operational governance, or risk functions. In that situation, models may be internally elegant but externally irrelevant. Adoption improves when patterns are tied to real processes such as investment intake, technology lifecycle review, transformation planning, control assessments, or post-merger analysis. A lightweight architecture board decision record linked to the relevant ArchiMate view, for example, can make model content directly usable in governance rather than merely descriptive.
For successful adoption, organizations should start with a small set of high-value patterns rather than a comprehensive doctrine. It is usually more effective to standardize three or four recurring viewpoints that support important governance decisions than to publish an extensive metamodel guide that few people follow. These initial patterns should be tested on real initiatives, refined through review, and supported by exemplars that show both correct structure and the expected level of detail.
Finally, architecture leaders should treat pattern adoption as a capability-building exercise. Training matters, but coaching, peer review, and repository stewardship matter more. Teams need feedback on whether a model is useful, not merely whether it is notation-compliant. The strongest ArchiMate practices combine disciplined modeling with pragmatic governance, keeping patterns light enough to use, strong enough to trust, and closely tied to enterprise decisions.
Conclusion
ArchiMate modeling patterns matter because they turn a flexible language into an enterprise discipline. Notation alone does not create architectural value. Value appears when architects use consistent structures to answer recurring questions, compare change options reliably, and maintain traceability as the organization evolves.
A useful way to judge any pattern is to ask whether it improves decision quality. If a pattern helps leaders see concentration risk, clarify ownership, expose redundant investment, or understand the consequences of change, it is doing real architectural work. If it merely produces a cleaner picture, its value is modest.
The patterns in this article follow a clear progression. First, strong modeling depends on clear purpose, disciplined abstraction, semantic consistency, and reusable viewpoints. Second, layering and cross-layer traceability create the backbone that connects strategy, business, applications, and technology. Third, strategy realization patterns show how capabilities, value streams, outcomes, and courses of action can be connected to meaningful change. Fourth, application and technology patterns make service exposure, integration logic, platform dependency, and deployment structure visible. Finally, governance and repository patterns ensure that all of this remains usable at enterprise scale.
The most effective organizations do not treat patterns as rigid templates. They use them as controlled defaults: stable enough to support consistency, but adaptable enough to fit stakeholder needs and organizational maturity. Over time, that approach produces a repository that is easier to govern and more valuable for analysis.
Ultimately, ArchiMate modeling patterns help enterprise architects scale their practice. They reduce ambiguity across teams, improve communication with non-architect stakeholders, and provide a durable structure for linking strategy, execution, and technology. For enterprises facing continual transformation, that combination of clarity, reuse, and analytical rigor is what makes modeling a management tool rather than just documentation.
Frequently Asked Questions
What is enterprise architecture?
Enterprise architecture is a discipline that aligns an organisation's strategy, business operations, information systems, and technology infrastructure. It provides a structured framework for understanding how an enterprise works today, where it needs to go, and how to manage the transition.
How is ArchiMate used in enterprise architecture practice?
ArchiMate is used as the standard modeling language in enterprise architecture practice. It enables architects to create consistent, layered models covering business capabilities, application services, data flows, and technology infrastructure — all traceable from strategic goals to implementation.
What tools are used for enterprise architecture modeling?
Common enterprise architecture modeling tools include Sparx Enterprise Architect (Sparx EA), Archi, BiZZdesign Enterprise Studio, LeanIX, and Orbus iServer. Sparx EA is widely used for its ArchiMate, UML, BPMN and SysML support combined with powerful automation and scripting capabilities.